
ANNUAL REPORT 2022


UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
Washington, D.C. 20549
FORM 10-K
(Mark One)
☒ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934
For the fiscal year ended January 29, 2023
or
☐TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934
For the transition period from to
Commission file number 1-8207
THE HOME DEPOT, INC.
(Exact name of registrant as specified in its charter)
Delaware 95-3261426
(State or other jurisdiction of incorporation or organization)
(I.R.S. Employer Identification No.)
2455 Paces Ferry Road
Atlanta, Georgia 30339
(Address of principal executive offices) (Zip Code)
Registrant’s telephone number, including area code: (770) 433-8211
Securities registered pursuant to Section 12(b) of the Act:
Title of each class Trading Symbol Name of each exchange on which registered
Common Stock, $0.05 Par Value Per Share HD New York Stock Exchange
Securities registered pursuant to section 12(g) of the Act: None
Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. Yes ☒ No ☐
Indicate by check mark if the registrant is not required to file reports pursuant to Section 13 or Section 15(d) of the Act. Yes ☐ No ☒
Indicate by check mark whether the registrant (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities
Exchange Act of 1934 during the preceding 12 months (or for such shorter period that the registrant was required to file such reports),
and (2) has been subject to such filing requirements for the past 90 days. Yes ☒ No ☐
Indicate by check mark whether the registrant has submitted electronically every Interactive Data File required to be submitted
pursuant to Rule 405 of Regulation S-T (§ 232.405 of this chapter) during the preceding 12 months (or for such shorter period that the
registrant was required to submit such files). Yes ☒ No ☐
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, a smaller
reporting company, or an emerging growth company. See the definitions of “large accelerated filer,” “accelerated filer,” “smaller
reporting company,” and “emerging growth company” in Rule 12b-2 of the Exchange Act.
Large accelerated filer ☒ Accelerated filer ☐Non-accelerated filer ☐Smaller reporting company ☐ Emerging growth company ☐
If an emerging growth company, indicate by check mark if the registrant has elected not to use the extended transition period for
complying with any new or revised financial accounting standards provided pursuant to Section 13(a) of the Exchange Act. ¨
Indicate by check mark whether the registrant has filed a report on and attestation to its management’s assessment of the
effectiveness of its internal control over financial reporting under Section 404(b) of the Sarbanes-Oxley Act (15 U.S.C. 7262(b)) by the
registered public accounting firm that prepared or issued its audit report. ☒
If securities are registered pursuant to Section 12(b) of the Act, indicate by check mark whether the financial statements of the
registrant included in the filing reflect the correction of an error to previously issued financial statements. ☐
Indicate by check mark whether any of those error corrections are restatements that required a recovery analysis of incentive-based
compensation received by any of the registrant’s executive officers during the relevant recovery period pursuant to §240.10D-1(b). ☐
Indicate by check mark whether the registrant is a shell company (as defined in Rule 12b-2 of the Act). Yes ☐ No ☒
The aggregate market value of voting common stock held by non-affiliates of the registrant on July 29, 2022 was $308.0 billion.
The number of shares outstanding of the registrant’s common stock as of March 1, 2023 was 1,014,955,506 shares.
DOCUMENTS INCORPORATED BY REFERENCE
Portions of the registrant’s proxy statement for the 2023 Annual Meeting of Shareholders are incorporated by reference in Part III of
this Form 10-K to the extent described herein.
Table of Contents

TABLE OF CONTENTS
Commonly Used or Defined Terms ii
Forward-Looking Statements iii
PART I
Item 1. Business. 1
Item 1A. Risk Factors. 10
Item 1B. Unresolved Staff Comments. 22
Item 2. Properties. 22
Item 3. Legal Proceedings. 23
Item 4. Mine Safety Disclosures. 24
PART II
Item 5. Market for Registrant’s Common Equity, Related Stockholder Matters and Issuer Purchases of
Equity Securities.
24
Item 6. Reserved. 25
Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations. 25
Item 7A. Quantitative and Qualitative Disclosures About Market Risk. 32
Item 8. Financial Statements and Supplementary Data. 33
Item 9. Changes in and Disagreements With Accountants on Accounting and Financial Disclosure. 62
Item 9A. Controls and Procedures. 63
Item 9B. Other Information. 65
Item 9C. Disclosure Regarding Foreign Jurisdictions that Prevent Inspections. 65
PART III
Item 10. Directors, Executive Officers and Corporate Governance. 65
Item 11. Executive Compensation. 66
Item 12. Security Ownership of Certain Beneficial Owners and Management and Related Stockholder
Matters.
66
Item 13. Certain Relationships and Related Transactions, and Director Independence. 66
Item 14. Principal Accountant Fees and Services. 66
PART IV
Item 15. Exhibit and Financial Statement Schedules. 67
Item 16. Form 10-K Summary. 71
SIGNATURES 72
Fiscal 2022 Form 10-K
i
COMMONLY USED OR DEFINED TERMS
ASU Accounting Standards Update
BODFS Buy Online, Deliver From Store
BOPIS Buy Online, Pickup In Store
BORIS Buy Online, Return In Store
BOSS Buy Online, Ship to Store
CDP The not-for-profit organization formerly known as the Carbon Disclosure Project
Comparable sales As defined in the Results of Operations section of MD&A
DIFM Do-It-For-Me
DIY Do-It-Yourself
EH&S Environmental, Health, and Safety
EPA U.S. Environmental Protection Agency
ESG Environmental, social, and governance
ESPP Employee Stock Purchase Plan
Exchange Act Securities Exchange Act of 1934, as amended
FASB Financial Accounting Standards Board
fiscal 2020 Fiscal year ended January 31, 2021 (includes 52 weeks)
fiscal 2021 Fiscal year ended January 30, 2022 (includes 52 weeks)
fiscal 2022 Fiscal year ended January 29, 2023 (includes 52 weeks)
fiscal 2023 Fiscal year ending January 28, 2024 (includes 52 weeks)
GAAP U.S. generally accepted accounting principles
IRS Internal Revenue Service
LIBOR London interbank offered rate
MD&A Management’s Discussion and Analysis of Financial Condition and Results of Operations
MRO Maintenance, repair, and operations
NOPAT Net operating profit after tax
NYSE New York Stock Exchange
PLCC Private label credit card
Pro Professional customer
Restoration Plans Home Depot FutureBuilder Restoration Plan and HD Supply Restoration Plan
ROIC Return on invested capital
SEC Securities and Exchange Commission
Securities Act Securities Act of 1933, as amended
SG&A Selling, general, and administrative
Term Definition
Table of Contents
Fiscal 2022 Form 10-K
ii
FORWARD-LOOKING STATEMENTS
Certain statements contained herein, as well as in other filings we make with the SEC and other written and oral
information we release, regarding our performance or other events or developments in the future constitute
“forward-looking statements” as defined in the Private Securities Litigation Reform Act of 1995. Forward-looking
statements may relate to, among other things, the demand for our products and services; net sales growth;
comparable sales; the effects of competition; our brand and reputation; implementation of store, interconnected
retail, supply chain and technology initiatives; inventory and in-stock positions; the state of the economy; the state of
the housing and home improvement markets; the state of the credit markets, including mortgages, home equity
loans, and consumer credit; the impact of tariffs; issues related to the payment methods we accept; demand for
credit offerings; management of relationships with our associates, potential associates, suppliers and service
providers; cost and availability of labor; costs of fuel and other energy sources; international trade disputes, natural
disasters, climate change, public health issues (including the continuing impacts of the COVID-19 pandemic and the
related recovery), cybersecurity events, military conflicts or acts of war, supply chain disruptions, and other business
interruptions that could compromise data privacy or disrupt operation of our stores, distribution centers and other
facilities, our ability to operate or access communications, financial or banking systems, or supply or delivery of, or
demand for, our products or services; our ability to address expectations regarding ESG matters and meet ESG
goals; continuation or suspension of share repurchases; net earnings performance; earnings per share; dividend
targets; capital allocation and expenditures; liquidity; return on invested capital; expense leverage; changes in
interest rates; changes in foreign currency exchange rates; commodity or other price inflation and deflation; our
ability to issue debt on terms and at rates acceptable to us; the impact and expected outcome of investigations,
inquiries, claims, and litigation, including compliance with related settlements; the challenges of international
operations; the adequacy of insurance coverage; the effect of accounting charges; the effect of adopting certain
accounting standards; the impact of legal and regulatory changes, including changes to tax laws and regulations;
store openings and closures; financial outlook; and the impact of acquired companies on our organization and the
ability to recognize the anticipated benefits of any acquisitions.
Forward-looking statements are based on currently available information and our current assumptions, expectations
and projections about future events. You should not rely on our forward-looking statements. These statements are
not guarantees of future performance and are subject to future events, risks and uncertainties – many of which are
beyond our control, dependent on the actions of third parties, or currently unknown to us – as well as potentially
inaccurate assumptions that could cause actual results to differ materially from our historical experience and our
expectations and projections. These risks and uncertainties include, but are not limited to, those described in Part I,
Item 1A. Risk Factors, and elsewhere in this report and also as may be described from time to time in future reports
we file with the SEC. You should read such information in conjunction with our consolidated financial statements
and related notes and Part II, Item 7. Management's Discussion and Analysis of Financial Condition and Results of
Operations in this report. There also may be other factors that we cannot anticipate or that are not described herein,
generally because we do not currently perceive them to be material. Such factors could cause results to differ
materially from our expectations. Forward-looking statements speak only as of the date they are made, and we do
not undertake to update these statements other than as required by law. You are advised, however, to review any
further disclosures we make on related subjects in our filings with the SEC and in our other public statements.
Table of Contents
Fiscal 2022 Form 10-K
iii

PART I
Item 1. Business.
INTRODUCTION
The Home Depot, Inc. is the world’s largest home improvement retailer based on net sales for fiscal 2022. We offer
our customers a wide assortment of building materials, home improvement products, lawn and garden products,
décor products, and facilities maintenance, repair and operations products. We also provide a number of services,
including home improvement installation services and tool and equipment rental. As of the end of fiscal 2022, we
operated 2,322 stores located throughout the U.S. (including the Commonwealth of Puerto Rico and the territories
of the U.S. Virgin Islands and Guam), Canada, and Mexico. The Home Depot stores average approximately
104,000 square feet of enclosed space, with approximately 24,000 additional square feet of outside garden area.
We also maintain a network of distribution and fulfillment centers, as well as a number of e-commerce websites in
the U.S., Canada and Mexico. When we refer to “The Home Depot,” the “Company,” “we,” “us” or “our” in this report,
we are referring to The Home Depot, Inc. and its consolidated subsidiaries.
The Home Depot, Inc. is a Delaware corporation that was incorporated in 1978. Our Store Support Center
(corporate headquarters) is located at 2455 Paces Ferry Road, Atlanta, Georgia 30339. Our telephone number at
that address is (770) 433-8211.
OUR BUSINESS
OUR STRATEGY
The retail landscape has changed rapidly over the past several years, with customer expectations constantly
evolving. In fiscal 2022, we continued to operate with agility to meet the challenges created by a fluid domestic and
global business environment, including supply chain disruptions, tight labor market conditions, and ongoing
inflationary pressures. Our ability to operate successfully and meet the needs of our customers was due in
significant part to our investments over the past several years aimed at creating an interconnected, frictionless
shopping experience that enables our customers to seamlessly blend the digital and physical worlds. Going forward,
we will leverage the momentum of these investments and continue to invest in our business in support of the
following goals:
• We intend to provide the best customer experience in home improvement;
• We intend to extend our position as the low-cost provider in home improvement; and
• We intend to be the most efficient investor of capital in home improvement.
We believe that these goals will help us grow faster than the market and deliver value to our shareholders. We are
steadfast in this commitment, while also recognizing that exercising corporate responsibility and being informed by
the needs of our other stakeholders, including our customers, associates, supplier partners, and communities,
creates value for all stakeholders, including our shareholders.
DELIVER SHAREHOLDER VALUE
We deliver on our objective to create shareholder value through our disciplined approach to capital allocation. Our
capital allocation principles are as follows:
• First, we intend to reinvest in our business to drive growth faster than the market.
• Second, after meeting the needs of the business, we look to pay a quarterly dividend, which we intend to
increase as we grow earnings.
• Third, after reinvesting in our business and paying our dividend, we intend to return excess cash to our
shareholders through share repurchases.
In fiscal 2022, we invested $3.1 billion in capital expenditures to support our business, advance our goals, and
continue to build an interconnected customer experience. We also focused on driving productivity throughout the
business to lower our costs. The combination of reinvesting in the business to drive higher sales and supporting
productivity to lower costs creates what we refer to as a virtuous cycle, which has allowed us to improve the
customer experience, increase our competitiveness in the market, and deliver shareholder value.
In fiscal 2022, we returned over $14 billion to shareholders in the form of cash dividends and share repurchases.
Our capital allocation is discussed further in Part II, Item 7. Management’s Discussion and Analysis of Financial
Condition and Results of Operations.
Table of Contents
Fiscal 2022 Form 10-K
1

OUR CUSTOMERS
We serve two primary customer groups — consumers (including both DIY and DIFM customers) and professional
customers — and have developed varying approaches to meet their diverse needs:
DIY Customers
These customers are typically homeowners who purchase products and complete their own projects and
installations. Our associates assist these customers both in our stores and through online resources and other
media designed to provide product and project knowledge. We also offer a variety of clinics and workshops both to
share this knowledge and to build an emotional connection with our DIY customers.
Professional Customers (or “Pros”)
These customers are primarily professional renovators/remodelers, general contractors, maintenance professionals,
handymen, property managers, building service contractors and specialty tradespeople, such as electricians,
plumbers and painters. These customers build, renovate, remodel, repair, and maintain residential properties,
multifamily properties, hospitality properties, and commercial facilities, including education, healthcare, government,
institutional, and office buildings.
We have a number of initiatives designed to drive growth with our Pros, including a customized online experience, a
dedicated sales force, an extensive delivery network, our Pro Xtra loyalty program, enhanced credit offerings, and
inventory management programs. Building on our historical strength as a destination for urgent purchase needs, we
are investing in capabilities that will help us better serve our Pros’ planned purchase needs (in-store or via our
dedicated sales team), including our expanded supply chain capabilities and advance ordering through our
interconnected digital platforms. We believe that focusing on meeting the Pros’ planned purchase needs, particularly
for larger renovator/remodeler Pros, will help us drive growth and deliver value to our shareholders.
We extended our reach in the MRO marketplace with our fiscal 2020 acquisition of HD Supply, a leading national
distributor and provider of MRO products and related value-added services to multifamily, hospitality, healthcare,
and government housing facilities, among others, and in fiscal 2021 we integrated our legacy Interline Brands
business into HD Supply. Our MRO operations use a distribution center-based model that sells products primarily
through a professional sales force and through e-commerce platforms and print catalogs.
We recognize the great value our Pros provide to their clients, and we strive to make their jobs easier and help them
grow their businesses. We believe that investments aimed at deepening our relationships with our Pros are yielding
increased engagement and will continue to translate into incremental sales to these customers.
DIFM Customers
Intersecting our DIY customers and our Pros are our DIFM customers. These customers are typically homeowners
who use Pros to complete their project or installation. Currently, we offer installation services in a variety of
categories, such as flooring, water heaters, bath, garage doors, cabinets, cabinet makeovers, countertops, sheds,
furnaces and central air systems, and windows. DIFM customers can purchase these services in our stores, online,
or in their homes through in-home consultations. In addition to serving our DIFM customer needs, we believe our
focus on the Pros who perform services for these customers helps us drive higher product sales.
OUR PRODUCTS AND SERVICES
A typical The Home Depot store stocks approximately 30,000 to 40,000 items during the year, including both
national brand name and proprietary products. Our online product offerings complement our stores by serving as an
extended aisle, and we offer a significantly broader product assortment through our websites and mobile
applications, including homedepot.com, our primary website; homedepot.ca and homedepot.com.mx, our websites
in Canada and Mexico; hdsupply.com, our website for our MRO products and related services; blinds.com, our
online site for custom window coverings; and thecompanystore.com, our online site featuring textiles and décor
products.
We believe our merchandising organization is a key competitive advantage, delivering product innovation,
assortment and value, which reinforces our position as the product authority in home improvement. In fiscal 2022,
we continued to invest in merchandising resets in our stores to refine assortments, optimize space productivity,
introduce innovative new products to our customers, and improve visual merchandising to drive a better shopping
experience. At the same time, we remain focused on offering everyday values in our stores and online.
To help our
merchandising organization keep pace with changing customer expectations and increasing desire for innovation,
localization, and personalization, we are continuing to invest in tools to better leverage our data and drive a deeper
level of collaboration with our supplier partners. As a result, we have continued to focus on enhanced
Table of Contents
Fiscal 2022 Form 10-K
2

merchandising information technology tools to help us: (1) build an interconnected shopping experience that is
tailored to our customers’ shopping intent and location; (2) provide the best value in the market; and (3) optimize our
product assortments. Our merchandising team leverages technology and works closely with our inventory and
supply chain teams, as well as our supplier partners, to manage our assortments, drive innovation, and adjust
inventory levels to respond to fluctuations in demand, which helped us navigate the challenges of continuing global
supply chain disruption in fiscal 2022. As cost pressures have risen in several product categories in the current
environment, our tools have helped our merchandising, finance and data analytics teams as they work with our
supplier partners to manage these pressures.
To complement our merchandising efforts, we offer a number of services for our customers, including installation
services for our DIY and DIFM customers, as noted above. We also provide tool and equipment rentals at locations
across the U.S. and Canada, providing value and convenience for both Pros and consumers. To improve the
customer experience and continue to grow this differentiated service offering, we are continuing to invest in more
locations (including piloting rental locations in Mexico), more tools, and better technology.
Sourcing and Quality Assurance
We maintain a global sourcing program to obtain high-quality and innovative products directly from manufacturers in
the U.S. and around the world. During fiscal 2022, in addition to our U.S. sourcing operations, we maintained
sourcing offices in Mexico, Canada, China, India, Vietnam and Europe. To ensure that suppliers adhere to our high
standards of social and environmental responsibility, we also have a global responsible sourcing program. Under
our supplier contracts, our suppliers are obligated to ensure that their products comply with applicable international,
federal, state and local laws. These contracts also require compliance with our responsible sourcing standards,
which cover a variety of expectations across multiple areas of social compliance, including supply chain
transparency, compliance with local laws, health and safety, environmental laws and regulations, compensation,
hours of work, and prohibitions on child and forced labor. To drive accountability with our suppliers, our standard
supplier buying agreement includes a factory audit right related to these standards, and we conduct factory audits
and compliance visits with non-Canada and non-U.S. suppliers of private branded and direct import products. Our
2022 Responsible Sourcing Report, available on our website at https://corporate.homedepot.com under
“Responsibility > Sourcing Responsibly,” provides more information about this program. In addition, we have both
quality assurance and engineering resources dedicated to establishing criteria and overseeing compliance with
safety, quality and performance standards for our private branded products.
Intellectual Property
Our business has one of the most recognized brands in North America. As a result, we believe that The Home
Depot
®
trademark has significant value and is an important factor in the marketing of our products, e-commerce,
stores and business. We have registered or applied for registration of trademarks, service marks, copyrights and
internet domain names, both domestically and internationally, for use in our business, including our proprietary
brands such as HDX
®
, Husky
®
, Hampton Bay
®
, Home Decorators Collection
®
, Glacier Bay
®
, Vigoro
®
, Everbilt
®
and
Lifeproof
®
. The duration of trademark registrations varies from country to country. However, trademarks are
generally valid and may be renewed indefinitely as long as they are in use and/or their registrations are properly
maintained.
We also maintain patent portfolios relating to our business operations, retail services, and products, and we seek to
patent or otherwise protect innovations we incorporate into our business. Patents generally have a term of twenty
years from the date they are filed. As our patent portfolio has been built over time, the remaining terms of the
individual patents across our patent portfolio vary. Although our patents have value, no single patent is essential to
our business. We continuously assess our merchandising departments and product lines for opportunities to expand
the assortment of products offered within The Home Depot’s portfolio of proprietary and exclusive brands.
COMPETITION AND SEASONALITY
Our industry is highly competitive, very fragmented, and evolving. As a result, we face competition for customers for
our products and services from a variety of retailers, suppliers, service providers, and distributors and
manufacturers that sell products directly to their respective customer bases. These competitors range from
traditional brick-and-mortar, to multichannel, to exclusively online, and they include a number of other home
improvement retailers; electrical, plumbing and building materials supply houses; and lumber yards. With respect to
some products and services, we also compete with specialty design stores, showrooms, discount stores, local,
regional and national hardware stores, paint stores, specialty and mass digital retailers, warehouse clubs,
independent building supply stores, MRO distributors, home décor retailers, and other retailers, as well as with
Table of Contents
Fiscal 2022 Form 10-K
3

providers of home improvement services and tool and equipment rental. The internet facilitates competitive entry,
price transparency, and comparison shopping, increasing the level of competition we face.
Both in-store and online, we compete primarily based on customer experience, price, quality, product availability
and assortment, and delivery options. We also compete based on store location and appearance, presentation of
merchandise, and ease of shopping experience. Our Pros also look for a dedicated sales team, competitive credit
and pricing options, project planning tools, and product depth and job lot quantities, particularly for their planned
purchase needs. Furthermore, with respect to delivery options, customers are increasingly seeking faster and/or
guaranteed delivery times, low-price or free shipping, and/or convenient pickup options. Our ability to be competitive
on delivery and pickup times, options and costs depends on many factors, including the success of our supply chain
investments, described more fully under “Our Supply Chain” below.
Our business is subject to seasonal influences. Generally, our highest volume of sales occurs in our second fiscal
quarter, as we move into the spring season in the regions in which we operate.
INTERCONNECTED SHOPPING EXPERIENCE
We continue to enhance our capabilities to provide our customers with a frictionless interconnected shopping
experience across our stores, online, on the job site, and in their homes, focusing on continued investments in our
website and mobile apps to enhance the digital customer experience.
Digital Experience
Enhancements to our digital properties are critical for our increasingly interconnected customers, who often
research products online and check available inventory before going into one of our stores to view the products in
person or talk to an associate and then make their purchase in store or online. While in the store, customers may
also go online to access ratings and reviews, compare prices, view our extended assortment, and purchase
additional products. Our investments in a truly interconnected experience are focused on bringing together the
power of our physical retail presence and the frictionless interaction of our digital capabilities.
A significant majority of the traffic in our digital channels is on mobile devices. Mobile customers expect more
simplicity and relevancy in their digital interactions. As a result, we have made investments to our digital properties
to improve the overall presentation and ease of navigation for the user. We have also enhanced the “shopability” of
an online product by including more information on the product’s landing page, including related products and/or
parts of a collection, as well as various fulfillment options. We believe our focus on improving search capabilities,
site functionality, category presentation, product content, speed to checkout, and enhanced fulfillment options has
yielded higher traffic, better conversion and continued sales growth.
Further, we do not view the interconnected shopping experience as a specific transaction; rather, we believe it
encompasses an entire journey from inspiration and know-how, to purchase and fulfillment, to post-purchase care
and support. Customers expect more personalized messaging, so we are continuing to focus on connecting
marketing activities with the online and in-store experiences to create seamless engagement across channels. From
the inspirational point of the purchase journey to providing product know-how, we continue to invest in the
infrastructure and capabilities needed to deliver the most relevant marketing messages to our customers based
upon what is important to them today.
Store Experience
Our stores remain the hub of our business, and we continue to invest to improve the customer shopping experience
through easier navigation and increased convenience and speed of checkout. In fiscal 2022, we continued to
leverage the investments made in our stores over the past several years to operate effectively and meet changing
customer expectations. These investments include wayfinding signage and store refresh packages; self-service
lockers, online order storage areas at front entrances and curbside pickup to provide convenient pickup options for
online orders; electronic shelf label capabilities; and the re-design of front-end areas, including reconfigured service
desks, improved layouts in checkout areas, and expanded and enhanced self-checkout options. To improve the
customer’s experience in our stores, we have also empowered our customers with additional self-help tools,
including mobile app-enabled store navigation. Our app provides store-specific maps, which allow customers to
pinpoint the exact location of an item on their mobile devices. We believe these investments are driving higher
customer satisfaction scores, and we will continue to invest to improve the customer experience going forward.
Investing in Associate Productivity. We continually strive to improve our store operations for our associates. Our
goal is to remove complexity and inefficient processes from the stores to allow our associates to focus on our
customers. To this end, we have continued to focus our efforts in such areas as optimizing product flow to decrease
the amount of time a store associate spends locating product and to improve on-shelf product availability; creating a
Table of Contents
Fiscal 2022 Form 10-K
4

simpler order management system; expanding in-aisle, real-time mobile learning tools for our associates’ own
development and to assist with customer questions; and using labor model tools to better align associate activity
with customer needs. For several years, our associates have used web-enabled handheld devices to help them
more efficiently meet the needs of the business and serve customers. In fiscal 2022, we began rolling out the next
generation of digital phones to our stores, which we call “hdPhones,” so that each associate will have a digital
device during their shift. The new devices offer enhanced functionality to allow associates to readily query inventory,
access applications that support customer service, and drive on-shelf availability of product.
Investing in Safety. We are committed to maintaining a safe shopping and working environment for our customers
and associates. We empower trained EH&S associates to evaluate, develop, implement and enforce policies,
processes and programs on a Company-wide basis. Our EH&S policies are woven into our everyday operations
and are part of The Home Depot culture. Common program elements include daily store inspection checklists (by
department); routine follow-up audits from our store-based safety team members and regional, district and store
operations field teams; equipment enhancements and preventative maintenance programs to promote physical
safety; departmental merchandising safety standards; training and education programs for all associates, with
varying degrees of training provided based on an associate’s role and responsibilities; and awareness,
communication and recognition programs designed to drive operational awareness and an understanding of EH&S
matters.
OUR SUPPLY CHAIN
We continue to focus on building best-in-class competitive advantages in our supply chain to be responsive to our
customers’ expectations for how, when and where they choose to receive our products and services. As part of
enhancing the interconnected shopping experience, we continue to invest in expanding our supply chain network,
with the goal of achieving the fastest, most efficient and most reliable delivery capabilities in home improvement.
Our efforts are focused on ensuring product availability and increasing the speed and reliability of delivery for our
customers while managing our costs. Our supply chain investments have helped us to operate effectively and meet
our customers’ needs throughout the challenging environment over the past few years.
We centrally forecast and replenish the vast majority of our store products through sophisticated inventory
management systems and utilize our network of distribution centers to serve both our stores’ and customers’ needs.
Our supply chain includes multiple distribution center platforms in the U.S., Canada, and Mexico tailored to meet the
needs of our stores and customers based on types of products, location, transportation, and delivery requirements.
These platforms include rapid deployment centers, stocking distribution centers, bulk distribution centers, and direct
fulfillment centers, among others. As part of the expansion of our supply chain, we have invested to further
automate and mechanize our rapid deployment center network to drive efficiency and faster movement of product.
We are also continuing to expand our fulfillment network, investing in a significant number of new fulfillment facilities
to drive speed and reliability of delivery for our customers and to help us ultimately meet our goal of reaching 90%
of the U.S. population with same or next day delivery for extended home improvement product offerings, including
big and bulky products. These facilities include omni-channel fulfillment centers, which deliver product directly to
customers, and market delivery operations, which function as local hubs to consolidate freight for dispatch to
customers for the final mile of delivery, with a focus on appliances. In fiscal 2022, we realized our goal to control
more of our appliance delivery end-to-end and began managing all of our appliance delivery volume through our
market delivery operations. We have also added flatbed distribution centers, which handle large items like lumber
and building materials that are transported on flatbed trucks. As of the end of fiscal 2022, we have opened a number
of additional fulfillment facilities, and we will continue to build out our fulfillment network to support our business. Our
network is designed to create a competitive advantage with unique, industry-leading capabilities for home
improvement needs for both Pros and consumers.
In addition to our distribution and fulfillment centers, we leverage our stores as a network of convenient customer
pickup, return, and delivery fulfillment locations. Our premium real estate footprint provides a distinct structural and
competitive advantage. For customers who shop online and wish to pick up or return merchandise at, or have
merchandise delivered from, our stores, we have implemented four interconnected retail programs: BOSS, BOPIS,
BODFS, and BORIS. We also provide curbside pickup to complement our BOPIS offerings, in addition to the self-
service lockers at the front entrance of many of our stores. We also offer express car and van delivery service that
covers over 80% of the U.S. population. For fiscal 2022, approximately 50% of our U.S. online orders were fulfilled
through a store. We also continue to focus on developing new capabilities to improve both efficiency and customer
experience in our store delivery program. Our strategic intent is to have a portfolio of efficient, timely and reliable
sources and methods of delivery to choose from, optimizing order fulfillment and delivery based on customer needs,
inventory locations and available transportation options.
Table of Contents
Fiscal 2022 Form 10-K
5
CORPORATE RESPONSIBILITY AND HUMAN CAPITAL MANAGEMENT
We view environmental, social and governance matters through the lens of our business, with an understanding that
if we support our associates, our customers, our supplier partners, and the communities we serve, we also support
our business and create long-term value for our shareholders. As a result, we believe that ESG is fundamentally
embedded in our operations and culture. We organize our efforts around three pillars: (1) Focus on Our People, (2)
Operate Sustainably, and (3) Strengthen Our Communities. Highlights of each of these pillars are set forth below.
For further information on our three pillars and other ESG-related matters, see our annual ESG Report, available on
our website at https://corporate.homedepot.com/responsibility.
Focus on Our People
Our culture and our associates provide intangible and hard-to-replicate competitive advantages, which have been
key to helping us navigate challenging market conditions. Our associates are essential to providing the experience
and service that our customers demand. To preserve and protect that customer experience, we focus on cultivating
a compelling associate experience, which we believe supports our ability to attract and retain our associates. This
includes investing in competitive wages and benefits while also providing the culture, tools, training and
development opportunities that make working at The Home Depot an enjoyable and rewarding experience. These
actions are the foundation of our key tenets of putting customers first and taking care of our associates.
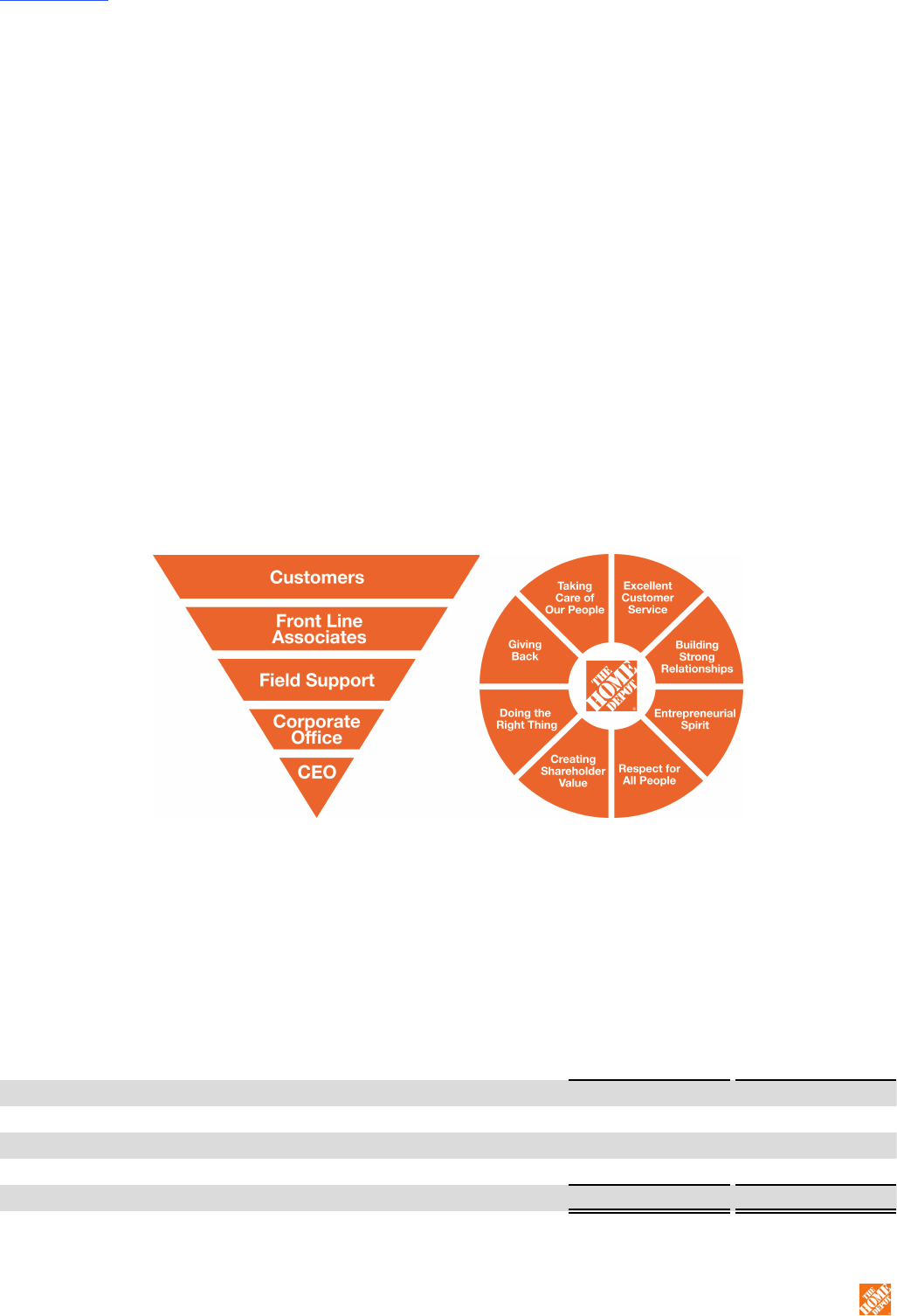
Culture and Values. The Home Depot has a strong commitment to ethics and integrity, and we are a values- and
culture-centric business. Our commitment to our core values drives our approach to human capital management.
Our culture is based on our servant leadership philosophy represented by the inverted pyramid, which puts primary
importance on our customers and our associates by positioning them at the top, with senior management at the
base in a support role. We bring our culture to life through our core values, which serve as the foundation of our
business and as the guiding principles behind the decisions we make every day.
Our values also guide our efforts to create an environment that will help us attract and retain skilled associates in
the competitive marketplace for talent. We empower our associates to deliver a superior customer experience by
living our values, and we position our associates to embody our core values by integrating the importance of our
culture into ongoing development programs, performance management practices, and rewards programs. Leaders
participate in programs designed to build and strengthen our culture, such as training on leadership skills, cross-
functional collaboration, inclusiveness, and associate engagement, and all associates receive annual training on
unconscious bias. Our core values are at the root of our human capital management programs.
Our Workforce. At the end of fiscal 2022, we employed approximately 471,600 associates, of whom approximately
46,500 were salaried, with the remainder compensated on an hourly basis. Set forth below is the geographic
makeup of our workforce:
Geographic Location Number of Associates % of Total Workforce
United States 418,900 88.8%
Canada 34,500 7.3%
Mexico 17,900 3.8%
Other
(1)
300 0.1%
Total 471,600 100%
————
(1) Includes associates in our sourcing organization located in China, Vietnam, India, Italy, Poland and Turkey.
Table of Contents
Fiscal 2022 Form 10-K
6
Talent Attraction and Development. As we attract and hire new associates, we strive to create a customer-like
experience for jobseekers as they progress through the steps of our recruiting process by focusing on speed and
personalization. We employ targeted marketing practices through our careers website, which personalizes the
user’s experience based on jobseeker location and searching behavior. Jobseekers can also apply for roles from
anywhere using desktop or mobile devices. Once a jobseeker has applied for a role and has been selected to move
forward in the recruiting process, we provide self-service by allowing candidates to schedule or reschedule pre-hire
activities directly from their mobile device. Lastly, we created a quick hiring process for candidates by leveraging
job-matching automation that matches candidates to jobs that fit their needs.
We offer all of our associates the opportunity to benefit from robust development opportunities. Our Home Depot
University, or “HDU,” program, is a key part of this development, offering relevant content through multiple
platforms, including instructor-led classes, e-learning, mobile learning, and additional online resources. We invest in
ongoing growth and development by integrating our culture and values into our performance management
practices, providing coaching through continuous leader support, and empowering our associates to learn new skills
at their own pace through mobile applications our associates can access at any time. We equip our leaders with the
tools they need to develop themselves and their teams through several programs designed to help them lead
inclusively, empower their teams, and serve as mentors for our associates.
In fiscal 2022, we supported both associate development and engagement by starting the year with a new store
leadership structure. We created new management positions in our stores focused on the customer service
experience, increasing the number of managers on the floor at any given time. This new structure frees up time for
other store leaders to devote to associate training and development. The result is an improved customer and
associate experience, while also providing new career paths for associates.
Associate Engagement. Associate engagement is the emotional commitment associates have to The Home
Depot. It is vital to our culture and to our success. We create an engaging workplace by continuously listening to
and acting on associate feedback. We provide several pulse check surveys to associates throughout the year that
help us determine how emotionally connected those associates are to our customers, the Company, their jobs,
fellow associates, and leaders. In addition, our annual Voice of the Associate survey, which includes all associates,
serves as our primary means of gauging associates’ level of engagement within their roles. We use the feedback
from these surveys to help improve the overall associate experience. We also maintain a digital associate
engagement platform that links associates with common interests and fuels connections to co-workers and
Company leaders. Additionally, we have a number of programs to recognize stores and individual associates for
exceptional customer service and demonstrating our core values.
Diversity, Equity and Inclusion. Guided by our core values and grounded in our culture, we believe that having a
diverse, equitable and inclusive Company is key to our success. We are focused on building a workplace and retail
space that reflect the customers and communities we are proud to serve. We strive to maintain a Company where
our associates are valued and respected and feel a sense of belonging in the workplace, so that they can provide
the customer experience that supports our business. Our Office of Diversity, Equity and Inclusion supports our focus
on associate diversity, supplier diversity, and engagement with our communities. Below is the fiscal 2022 diversity
data for our U.S. associates:
Associate Population
Race/Ethnicity Gender
% Minority % White % Undisclosed % Female % Male % Undisclosed
U.S. Workforce 48% 50% 2% 38% 62% 1%
U.S. Managers & Above
(1)
39% 60% 1% 35% 65% 0%
U.S. Officers 26% 73% 2% 29% 69% 2%
————
(1) Does not include officers.
Note: Certain percentages may not sum to totals due to rounding.
As a Company, we have identified several priorities designed to guide our efforts to enhance diversity, equity and
inclusion. We believe these associate-, supplier- and community-focused priorities will further enhance our
customers’ experience and make a sustainable difference within the workplace, marketplace, and community:
• Associate Engagement
◦ Increase diverse representation throughout our organization
◦ Create an environment where every associate feels included and valued for who they are
◦ Promote equal opportunity in recruitment, hiring, training, development and advancement
Table of Contents
Fiscal 2022 Form 10-K
7
• Supplier Diversity
◦ Increase use of and spend with diverse suppliers
◦ Develop diverse suppliers by providing mentorship and sharing resources
• Community Engagement
◦ Partner with organizations on programs designed to close the wealth gap
◦ Support programs that advance education for all
Compensation and Benefits. Consistent with our core values, we take care of our people by offering competitive
compensation and comprehensive benefits programs. We continuously make wage investments to ensure our
compensation packages reflect the evolving circumstances across our markets, and our profit-sharing program for
hourly associates provides semi-annual cash awards for performance against our business plan. We transitioned
from the enhanced pay and benefits we provided for our associates in fiscal 2020 to alleviate some of the
challenges presented by the COVID-19 pandemic to permanent compensation enhancements for our frontline,
hourly associates, which we have continued to make since fiscal 2020. Our associates can take advantage of a
range of benefits, including healthcare and wellness programs, vacation and leave of absence benefits including
parental leave and paid sick/personal time off, a 401(k) match, our ESPPs, personal finance education and advisory
services, assistance programs to help with managing personal and work-life challenges, family support programs,
and educational assistance.
Operate Sustainably
We have a long-standing and substantial commitment to sustainable business operations, understanding that if we
make our operations more efficient and sustainable, we can support both our business and the environment. This
philosophy extends from the products and services we offer to our customers; to our store construction,
maintenance and operations; to our supply chain and packaging initiatives; to our ethical sourcing program. As we
strive to operate sustainably, we have focused on efforts that help protect the climate, reduce our environmental
impact, and source products responsibly, and we have set goals to drive progress in these areas.
Our 2022 ESG Report, available on our website at https://corporate.homedepot.com/responsibility, includes more
information on our goals, as well as specific initiatives we have in place to help achieve these goals. Below are
highlights of our sustainability strategy.
Our Environmental Goals. We currently have several goals to help address climate impact and reduce our
environmental footprint:
Year Announced Goal Goal Date Status
2018
Cleaning Products Chemical Reduction: Eliminate certain
added chemicals from residential household cleaning products
sold in-store or online by the end of fiscal 2022
2022 Complete
(1)
2018
Science-Based Carbon Emissions Targets: Reduce Scope 1
and 2 carbon emissions by 2.1% per year, with the goal to
achieve a 40% reduction by the end of fiscal 2030 and a 50%
reduction by the end of fiscal 2035
2030; 2035 In Process
2019
Recyclable Packaging: Exclude expanded polystyrene foam
(EPS) and polyvinyl chloride (PVC) film from the packaging of
private-brand products we sell, replacing them with easier-to-
recycle materials by the end of fiscal 2023
2023 In Process
2020 Renewable/Alternative Energy Sources: Produce or procure,
on an annual basis, 335 megawatts of renewable or alternative
energy by the end of fiscal 2025
2025 In Process
2021
100% Renewable Electricity: Produce or procure renewable
electricity equivalent to the needs for all Home Depot facilities
worldwide by the end of fiscal 2030
2030 In Process
————
(1) A de minimis number of suppliers are still in the process of reformulating and transitioning their product assortment.
These goals follow the completion of a number of previously announced goals, including goals related to reducing
store electricity use, eliminating certain chemicals from products we sell, and helping customers reduce their
greenhouse gas emissions and water use and save on electricity costs.
Table of Contents
Fiscal 2022 Form 10-K
8

Our Environmental Programs and Initiatives. In order to progress against our goals, we have a number of
environmentally-focused programs and initiatives, including:
• Store Operations and Renewable/Alternative Energy. We have reduced store energy consumption through
initiatives such as LED lighting upgrades; installation of energy-efficient HVAC systems; participation in
demand mitigation; on-site alternative or renewable energy projects such as fuel cells and solar panels; and
contracts with off-site wind and solar power providers. We have continued to work toward our goal to
produce or procure renewable electricity equivalent to the electricity needs for all Home Depot facilities by
the end of fiscal 2030. We have also continued our focus on saving water, implementing smart irrigation
systems capable of reducing irrigation-related water use in more than 500 U.S. stores.
• Product Offerings. Through our Eco Actions
TM
program, we have helped our customers more easily identify
products related to five areas: carbon emissions, circularity, responsible chemistry, sustainable forestry, and
water use. Under our Eco Actions program, we sell ENERGY STAR
®
certified appliances; WaterSense
®
-
labeled bath faucets, showerheads, aerators, toilets, and irrigation controllers; LED light bulbs; tankless
water heaters; and many other products. These products, through proper use, help our customers save
money on their utility bills and reduce their environmental impact. Through Eco Actions, we also provide
customers with resources, such as project tutorials, to take individual action on environmental issues.
• In-Store Recycling Programs. We offer customer-facing recycling programs in the U.S., including in-store
recycling programs for compact fluorescent light bulbs, rechargeable batteries, and lead acid batteries.
• Chemical Strategy. We are committed to increasing our assortment of products that meet high
environmental standards, and we encourage our suppliers to invest in developing environmentally-
innovative products. We periodically evaluate our Chemical Strategy to ensure our approach and goals are
appropriate.
• Sustainable Packaging. In addition to our goal related to eliminating EPS and PVC from our private-brand
products, we are continually working with our suppliers to find ways to make product packaging more
recyclable or simply use less materials, such as through the reduction of single-use plastics.
• Supply Chain Optimization. Through our supply chain initiatives such as space sharing and optimization
technology, we are working to maximize our use of every mile to make our supply chain more efficient. We
also utilize hydrogen fuel cell technology in a number of our forklifts to make our supply chain even more
environmentally responsible.
• CDP Participation. We are a long-standing participant in the annual CDP Climate Change reporting
process. CDP is an independent, international, not-for-profit organization providing a global system for
companies and cities to measure, disclose, manage, and share environmental information. In February
2023, we received a score of “B” from CDP. We have also announced that we plan to begin participating in
CDP’s Forests reporting process.
• Assessment of SBTi Goals. In fiscal 2021, we announced plans to adopt, by the end of fiscal 2023, new
Science Based Targets Initiative (SBTi) goals to reduce Scope 1, 2 and 3 emissions in line with Paris
Agreement goals. Adoption of SBTi goals would build on our current science-based goals to reduce Scope
1 and 2 carbon emissions by 2.1% per year, to achieve a 40% reduction by the end of fiscal 2030 and a
50% reduction by the end of fiscal 2035. In fiscal 2022, we continued to work on evaluating potential SBTi
goals.
Over the past several years, our commitment to sustainable operations has resulted in a number of environmental
awards and recognitions. In 2022, we received the following awards: an EPA WaterSense
®
Partner of the Year
Award for our commitment to offering and promoting water-efficient products; an EPA SmartWay High Performer
Award, which recognized us as an industry leader in improving freight efficiency and environmental performance; an
EPA Safer Choice Partner of the Year Award, which recognizes achievement in products with safer chemicals that
furthers innovative source reduction; and an EPA ENERGY STAR
®
Partner of the Year Award for our contribution to
promoting energy efficiency.
Strengthen our Communities
One of our core values is “Giving Back,” and we support our communities in a number of ways. The Home Depot
Foundation focuses on improving the homes and lives of U.S. veterans, assisting communities affected by natural
disasters, and training skilled tradespeople to fill the labor gap. The Company and The Home Depot Foundation are
partnering with industry leaders on training programs to train the next generation of skilled tradespeople and help
them find careers in the home improvement industry through our Path to Pro program, which includes a new career
networking site to connect skilled tradespeople to industry Pros. Our Team Depot associate volunteers also extend
Table of Contents
Fiscal 2022 Form 10-K
9
the mission of the Home Depot Foundation in communities across the country, donating thousands of volunteer
hours each year on a wide variety of projects.
We partner with diverse suppliers and organizations to further support our diversity, equity and inclusion efforts. As
noted above, our Office of Diversity, Equity and Inclusion partners with community organizations on programs
designed to close the wealth gap and enhance education outcomes across underserved and underrepresented
communities. To further advance diversity, equity and inclusion in our communities, we have a supplier diversity
program through which we provide supplier development and other resources to our diverse suppliers, and in fiscal
2021 we launched a Tier II supplier diversity program that aims to drive more spending from our direct suppliers to
diverse suppliers. In fiscal 2022, the Company joined the Billion Dollar Roundtable Inc., or BDR, a not-for-profit
organization that promotes supplier diversity excellence and best practices. The BDR consists of U.S.-based
corporations that spend $1.0 billion or more annually with minority- and woman-owned suppliers. We are working to
cultivate a supplier base that creates long-lasting growth and mutual business success, while reflecting the diversity
of our customers and strengthening the communities in which our customers and associates live.
Please see our 2022 ESG Report for additional information about our efforts to support the communities we serve.
GOVERNMENT REGULATION
As a company with both U.S. and international operations, we are subject to the laws of the U.S. and foreign
jurisdictions in which we operate and the rules and regulations of various governing bodies, which may differ among
jurisdictions. Compliance with these laws, rules and regulations has not had, and is not expected to have, a material
effect on our capital expenditures, results of operations, or competitive position as compared to prior periods.
AVAILABLE INFORMATION
Our internet website is www.homedepot.com. We make available on the Investor Relations section of our website,
free of charge, our Annual Reports to shareholders, Annual Reports on Form 10-K, Quarterly Reports on Form 10-
Q, Current Reports on Form 8-K, Proxy Statements, and Forms 3, 4 and 5, and amendments to those reports, as
soon as reasonably practicable after filing such documents with, or furnishing such documents to, the SEC.
We include website addresses throughout this report for reference only. The information contained on these
websites is not incorporated by reference into this report.
Item 1A. Risk Factors.
Our business, results of operations, and financial condition are subject to numerous risks and uncertainties. In
connection with any investment decision with respect to our securities, you should carefully consider the following
risk factors, as well as the other information contained in this report and our other filings with the SEC. Additional
risks and uncertainties not presently known to us or that we currently deem immaterial may also impair our business
operations. Should any of these risks materialize, our business, results of operations, financial condition and future
prospects could be negatively impacted, which in turn could affect the trading value of our securities. You should
read these Risk Factors in conjunction with Part II, Item 7. Management’s Discussion and Analysis of Financial
Condition and Results of Operations and our consolidated financial statements and related notes in Item 8.
STRATEGIC RISKS
Strong competition could adversely affect prices and demand for our products and services and could
decrease our market share.
Our industry is highly competitive, highly fragmented, and evolving. As a result, we face competition for customers
for our products and services from a variety of retailers, suppliers, service providers, and distributors and
manufacturers that sell products directly to their respective customer bases. These competitors range from
traditional brick-and-mortar, to multichannel, to exclusively online, and they include a number of other home
improvement retailers; electrical, plumbing and building materials supply houses; and lumber yards. With respect to
some products and services, we also compete with specialty design stores, showrooms, discount stores, local,
regional and national hardware stores, paint stores, specialty and mass digital retailers, warehouse clubs,
independent building supply stores, MRO distributors, home décor retailers, and other retailers, as well as with
providers of home improvement services and tool and equipment rental. The internet facilitates competitive entry,
price transparency, and comparison shopping, increasing the level of competition we face.
We compete primarily based on customer experience, price, quality, product availability and assortment, and
delivery options, both in-store and online. We also compete based on store location and appearance, presentation
of merchandise, and ease of shopping experience. Our Pros also look for a dedicated sales team, competitive credit
Table of Contents
Fiscal 2022 Form 10-K
10

and pricing options, project planning tools, and product depth and job lot quantities, particularly for their planned
purchase needs. Furthermore, customers are increasingly shopping online and seeking faster and/or guaranteed
delivery times, low-price or free shipping, and/or convenient pickup options. Our ability to be competitive on delivery
and pickup times, options and costs depends on many factors, including leveraging the momentum of our strategic
investments in our supply chain and our interconnected retail capabilities to further enhance the customer shopping
experience. Failure to successfully manage these factors and offer competitive delivery and pickup options could
negatively impact our profit margins and the demand for our products.
We use our marketing, advertising and promotional programs to drive customer traffic and compete more effectively,
and we must regularly assess and adjust our efforts to address changes in the competitive landscape. Intense
competitive pressures from one or more of our competitors, such as through aggressive promotional pricing or
liquidation events, or our inability to adapt effectively and quickly to a changing competitive landscape, could
adversely affect our prices, our margins, or demand for our products and services. If we are unable to timely and
appropriately respond to these competitive pressures, including through the delivery of a superior interconnected
customer experience or through maintenance of effective sales and marketing, advertising or promotional programs
leveraging both our digital and physical platforms, our market share and our financial performance could be
adversely affected. In addition, we are operating in a highly inflationary environment. If inflation increases beyond
our ability to control our related costs, we may not be able to adjust prices to sufficiently offset the effect of the
various cost increases without negatively impacting consumer demand, or it may adversely affect our ability to
compete based on price.
We may not timely identify or effectively respond to consumer needs, expectations or trends, which could
adversely affect our relationship with our customers, the demand for our products and services, and our
market share.
The success of our business depends in part on our ability to identify and respond promptly to evolving trends in
demographics; shifts in consumer preferences, expectations and needs; and unexpected weather conditions, public
health issues (including pandemics and related impacts), natural disasters, or changes in the macroeconomic
environment that impact our customers, while also managing appropriate inventory levels in our stores and
distribution or fulfillment centers and maintaining an excellent customer experience. It is difficult to successfully
predict the products and services our customers will demand. As our customers expect a more personalized
experience, our ability to collect, use and protect relevant customer data is important to our ability to effectively meet
their expectations. Our ability to collect and use that data, however, is subject to a number of external factors,
including the impact of legislation or regulations governing data privacy and security and customer expectations
around data collection and use. In addition, each of our primary customer groups has different needs and
expectations, many of which evolve as the demographics in a particular customer group change. Customer
preferences and expectations related to sustainability of products and operations are also changing. If we do not
successfully differentiate the shopping experience to meet the individual needs and expectations of or within a
customer group, we may lose market share with respect to those customers.
Customer expectations about the methods by which they purchase and receive products or services are also
becoming more demanding. Customers routinely and increasingly use technology and a variety of electronic
devices and digital platforms to rapidly compare products and prices, read product reviews, determine real-time
product availability, and purchase products, and new channels and tools to expand the customer experience appear
and change rapidly. Our Pros also look for additional capabilities, including a dedicated sales team, competitive
credit and pricing options, project planning tools, and product depth and job lot quantities, particularly for their
planned purchase needs. Once products are purchased, customers seek alternate options for delivery of those
products, including advance ordering through digital platforms for Pros, and they often expect quick, timely, and low-
price or free delivery and/or convenient pickup options. We must continually anticipate and adapt to these changes
in the shopping and purchasing process by continuing to adjust and enhance the online and in-store customer
experience as well as our delivery options. The coordinated operation of our network of physical stores, distribution
facilities, and online platforms is fundamental to the success of our interconnected strategy. We cannot guarantee
that our current or future fulfillment options will be maintained and implemented successfully or that we will be able
to meet customer expectations on delivery or pickup times, options and costs. In addition, as our customers
continue to leverage our enhanced interconnected shopping and fulfillment options, a greater concentration of
online sales with direct fulfillment could result in a reduction in the amount of traffic in our stores, which would, in
turn, reduce the opportunities for cross-selling of merchandise that such traffic creates and could reduce our overall
sales and adversely affect our financial performance. A greater concentration of online sales with direct fulfillment
could also result in higher costs for delivery, potentially impacting our profit margins.
Table of Contents
Fiscal 2022 Form 10-K
11

Failure to provide a relevant or effective online customer experience in a timely manner that keeps pace with
technological developments and dynamic customer expectations; to maintain appropriate inventory; to provide quick
and low-price or free delivery alternatives and convenient pickup options; to differentiate the customer experience
for our primary customer groups; to effectively implement an increasingly localized merchandising assortment; or to
otherwise timely identify or respond to changing consumer preferences, expectations and home improvement needs
could adversely affect our relationship with our customers, the demand for our products and services, and our
market share.
A positive brand and reputation are critical to our business success, and, if our brand and reputation are
damaged, it could negatively impact our relationships with our customers, current and potential associates,
suppliers, vendors, and shareholders, and, consequently, our business and results of operations or the
price of our stock.
Our brand and reputation are critical to attracting customers, current and potential associates, suppliers and
vendors to do business with us. We must continue to manage and protect our brand and reputation. Negative
incidents can erode trust and confidence quickly, and adverse publicity about us could damage our brand and
reputation; undermine our customers’ confidence in us; reduce demand for our products and services; affect our
ability to recruit, engage, motivate and retain associates; attract regulatory scrutiny; and impact our relationships
with current and potential suppliers and vendors. Further, our actual or perceived position or lack of position on
social, environmental, governance, political, public policy, economic, geopolitical, or other sensitive issues, and any
perceived lack of transparency about those matters, could harm our reputation with certain groups. Customers are
also increasingly using social media to provide feedback and information about our Company, including our
products and services, in a manner that can be quickly and broadly disseminated. Negative sentiment about the
Company shared over social media, or misinformation from fraudulent accounts impersonating the Company, could
impact our brand and reputation, whether or not it is based in fact.
The execution of initiatives to expand our supply chain and enhance the interconnected shopping
experience could disrupt our operations in the near term, and these initiatives might not provide the
anticipated benefits or might fail.
We continue to invest in our interconnected retail strategy, including by making significant investments to expand
our supply chain. These investments are designed to streamline our operations to allow our associates to continue
to provide high-quality service to our customers; simplify customer interactions; provide our customers with a more
interconnected shopping experience; better address Pro planned purchase needs; and create the fastest, most
efficient delivery network for home improvement products. Failure to choose the right investments and implement
them in the right manner and at the right pace could disrupt our operations. Executing our interconnected retail
strategy requires continual investment in our operations and information technology systems, as well as the
development and execution of new processes, systems and support. Building out our supply chain also involves
significant real estate projects as we expand our distribution network, requiring us to identify and secure available
locations with appropriate characteristics needed to support the different types of facilities. If we are unable to
effectively manage the volume, timing, nature, location, and cost of these investments, projects and changes, our
business operations and financial results could be materially and adversely affected. The cost and potential
problems, defects of design, and interruptions associated with the implementation of these initiatives, including
those associated with managing third-party service providers, employing new online tools and services,
implementing new technologies, implementing and restructuring support systems and processes, securing
appropriate facility locations, and addressing impacts on inventory levels, could disrupt or reduce the efficiency of
our operations in the near term, lead to product availability issues, and impact our profitability.
In addition, our stores are a key element of our interconnected retail strategy, serving as the hub of our customers’
interconnected shopping experience. We have an aging store base that requires maintenance, investment, and
space reallocation initiatives to deliver the shopping experience that our customers desire. We also need to identify
and secure available locations with appropriate characteristics for new stores to ensure we can continue to serve
our customers effectively. Our investments in our stores may not deliver the relevant shopping experience our
customers expect or fully support an interconnected shopping experience. We must also maintain a safe store
environment for our customers and associates, as well as protect against loss or theft of our inventory (also called
“shrink”), including as a result of organized retail crime. High rates of shrink, which we continue to experience, or an
unsafe store environment, requires operational changes that may increase costs and adversely impact the customer
and associate experience.
Our investments to enhance our interconnected shopping experience and expand our supply chain might not
provide the anticipated benefits, might take longer than expected to complete or realize anticipated benefits, or
Table of Contents
Fiscal 2022 Form 10-K
12
might fail altogether, each of which could adversely impact our competitive position and our financial condition,
results of operations, or cash flows.
If we are unable to effectively manage and expand our alliances and relationships with certain suppliers of
both brand name and proprietary products, we may be unable to effectively execute our strategy to
differentiate ourselves from our competitors.
As part of our focus on product differentiation, we have formed strategic alliances and exclusive relationships with
certain suppliers to market products under a variety of well-recognized brand names. We have also developed
relationships with certain suppliers to allow us to market proprietary products that are comparable to national
brands. Our proprietary products differentiate us from other retailers and generally carry higher margins than
national brand products. If we are unable to manage and expand these alliances and relationships, maintain
favorable terms with current suppliers, or identify alternative sources for comparable brand name and proprietary
products, we may not be able to effectively execute product differentiation, which may impact our sales and gross
margin results.
Our strategic transactions involve risks, which could have an adverse impact on our business, financial
condition and results of operations, and we may not realize the anticipated benefits of these transactions.
We regularly consider and enter into strategic transactions, including mergers, acquisitions, investments, alliances,
and other growth and market expansion strategies. We generally expect that these transactions will result in sales
increases, cost savings, synergies, enhanced capabilities or various other benefits. Assessing the viability and
realizing the benefits of these transactions is subject to significant uncertainty. For each of our acquisitions, we need
to determine the appropriate level of integration of the target company’s products, services, associates, and
information technology, financial, human resources, compliance, and other systems and processes, and then
successfully manage that integration into our corporate structure. Integration can be a complex and time-consuming
process, and if the integration is not fully successful or is delayed for a material period of time, we may not achieve
the anticipated synergies or benefits of the acquisition. In addition, the integration of businesses may create
complexity in our financial systems, internal controls, technology and cybersecurity systems, and operations and
may make them more difficult to manage. Even if the target companies are successfully integrated, the acquisitions
may fail to further our business strategy as anticipated, expose us to increased competition or challenges with
respect to our products or services, and expose us to additional risks and liabilities. Strategic transactions may also
be subject to significant regulatory uncertainty. The changing enforcement landscape may result in additional costs
or delays that affect the anticipated outcome of a transaction. Any failure in the execution of a strategic transaction
or investment, our approach to the integration of an acquired asset or business, or achievement of synergies or
other benefits could result in slower growth, higher than expected costs, the recording of an impairment of goodwill
or other intangible assets, and other actions which could adversely affect our business, financial condition and
results of operations.
OPERATIONAL RISKS
Our success depends upon our ability to attract, develop and retain highly qualified associates to provide
excellent customer service and to support our strategic initiatives while also controlling our labor costs.
Our customers expect a high level of customer service and product knowledge from our associates. To meet the
needs and expectations of our customers, we must attract, develop and retain a large number of highly qualified
associates and maintain a productive relationship with those associates. Our ability to meet our labor needs while
controlling labor costs is subject to numerous external factors, including increased market pressures with respect to
prevailing wage rates, unemployment levels, and health and other insurance costs; the impact of legislation or
regulations governing labor relations, employment, immigration, minimum wage, and healthcare benefits; changing
demographics and expectations among the workforce; public health concerns; and our reputation within the labor
market. We also compete with other retail businesses for many of our associates in hourly positions, and we invest
significant resources in training and motivating them to maintain a high level of job satisfaction. These positions
often have high turnover rates, which can lead to increased training and retention costs, particularly in a competitive
labor market. We have faced and may continue to face additional challenges in recruiting and retaining associates
due to wage pressure; flexible scheduling needs; disruption in the availability of childcare; challenges related to a
remote or hybrid working environment for associates who work in our store support centers; and health and safety
concerns. We are also subject to labor union efforts to organize groups of our associates from time to time and, if
successful, those organizational efforts may decrease our operational flexibility and efficiency, and/or otherwise
negatively impact our operations or reputation. These factors, together with growing competition among potential
employers, have resulted in and may continue to result in increased salaries, benefits, or other employee-related
Table of Contents
Fiscal 2022 Form 10-K
13

costs, and/or may impair our ability to recruit and retain associates, which could have an adverse impact on our
business operations, financial condition and results of operations.
In addition, to execute our interconnected retail strategy, including our supply chain investments, we must attract
and retain a large number of skilled professionals, including technology professionals, to implement our ongoing
technology and other investments. The market for these professionals is very competitive. An inability to provide
wages and/or benefits, including remote or hybrid work flexibility, that are competitive within the markets in which we
operate could adversely affect our ability to retain and attract associates. Further, changes in market compensation
rates may adversely affect our labor costs.
Additionally, our ability to successfully execute organizational changes, including management transitions within the
Company's senior leadership, and to effectively motivate and retain associates is critical to our business success. If
we are unable to locate, attract or retain qualified associates, or manage leadership transitions successfully, our
ability to effectively manage our strategy may be negatively impacted, the quality of service we provide to our
customers may decrease, and our financial performance may be adversely affected.
A failure of a key information technology system or process could adversely affect our business.
We rely extensively on information technology systems and related personnel to collect, process, retain, manage,
transmit, and protect transactions and data. Some of these systems are managed or provided by third-party service
providers, including certain cloud platform providers. In managing our business, we also rely heavily on the integrity
of, security of, and consistent access to, operational and financial data for information such as sales, customer data,
supplier data, associate data, job applicant data, partner data, demand forecasting, merchandise ordering, inventory
replenishment, supply chain management, payment processing, order fulfillment, customer service, and post-
purchase matters. For these information technology systems, applications, and processes to operate effectively, we
or our service providers must maintain and update them. Delays in the maintenance, updates, upgrading, or
patching of these systems, applications or processes could impair, and on occasion have impaired, their
effectiveness or could expose us to security risks. Our systems and the third-party systems with which we interact
are subject to and on occasion have experienced damage or interruption from a number of causes, including power
and other critical infrastructure outages; computer and telecommunications failures; computer viruses; data or
security breaches; internal or external data theft or misuse; cyber-attacks, including the use of malicious codes,
worms, phishing, smishing, vishing, spyware, denial of service attacks, and ransomware; responsive containment
measures by us that may involve voluntarily taking systems offline; natural disasters and catastrophic events such
as fires, floods, earthquakes, tornadoes, hurricanes, or other extreme weather events; public health concerns, such
as pandemics and quarantines; military conflicts, acts of war, terrorism or civil unrest; other systems outages;
inadequate or ineffective redundancy; and design or usage errors or malfeasance by our associates, contractors or
third-party service providers. In addition, as more business activities have shifted online, and as many of our store
support associates continue to work in a remote or hybrid environment, we face an increased risk due to the
potential failure of internal or external information technology infrastructure as well as increased cybersecurity
threats and attempts to breach our security networks.
Although we and our third-party service providers seek to maintain our respective systems effectively and to
successfully address the risk of compromise of the integrity, security and consistent operations of these systems,
such efforts are not always successful. As a result, we or our service providers could experience errors,
interruptions, delays or cessations of service in key portions of our information technology infrastructure, which
could significantly disrupt our operations or impair data security; impact our ability to operate or access
communications, financial or banking systems; be costly, time-consuming and resource-intensive to remedy; and
adversely impact our reputation and relationship with our customers, suppliers, shareholders or regulators.
In addition, we are currently making, and expect to continue to make, substantial investments in our information
technology systems, infrastructure and personnel, in certain cases with the assistance of strategic partners and
other third-party service providers. These investments involve replacing existing systems, some of which are older,
legacy systems that are less flexible and efficient, with successor systems; outsourcing certain technology and
business processes to third-party service providers; making changes to existing systems, including the migration of
applications to the cloud; maintaining or enhancing legacy systems that are not currently being replaced; or
designing or cost-effectively acquiring new systems with new functionality. These efforts can result in significant
potential risks, including failure of the systems to operate as designed, potential loss or corruption of data, failures in
security processes and internal controls, cost overruns, implementation delays or errors, disruption of operations,
and the potential inability to meet business and reporting requirements. Any system implementation and transition
difficulty may result in operational challenges, security failures, reputational harm, and increased costs that could
adversely affect our business operations and results of operations.
Table of Contents
Fiscal 2022 Form 10-K
14

Disruptions in our customer-facing technology systems could impair our interconnected retail strategy and
give rise to negative customer experiences.
Through our information technology systems, we are able to provide an improved overall shopping and
interconnected experience that empowers our customers to shop and interact with us from a variety of electronic
devices and digital platforms. We use our digital platforms as sales channels for our products and services, as
methods of providing inspiration, and as sources of product, project, and other relevant information to our customers
to help drive sales. We also have multiple online communities, digital platforms, and knowledge centers that allow
us to inform, assist and interact with our customers. The retail industry is continually evolving and expanding, with a
significant increase in sales initiated online and via mobile applications. We may not be successful at managing this
increased volume and related delivery options without interruption in the future. Additionally, we must effectively
respond to new developments and changing customer preferences with respect to a digital and interconnected
experience. We continually seek to enhance all of our online and digital properties to provide a personalized, user-
friendly interface for our customers. Disruptions, delays, failures or other performance issues with our customer-
facing technology systems, either due to increased volume, system modifications, or other factors, or a failure of
these systems to meet our or our customers’ expectations, could impair the value they provide, adversely impact
our sales, and negatively affect our relationship with our customers.
Disruptions in our supply chain and other factors affecting the availability and distribution of our
merchandise could adversely impact our business.
Disruption within our logistics or supply chain network, such as the industry-wide supply chain challenges resulting
from the COVID-19 pandemic, have in the past and may in the future adversely affect our ability to receive and
deliver inventory in a timely manner, impair our ability to meet customer demand for products, and result in lost
sales, increased supply chain costs, and/or damage to our reputation. Such disruptions may result from damage or
destruction to our distribution or fulfillment centers or those of our supply chain service providers; weather-related
events; cybersecurity incidents or attacks; natural disasters; international trade disputes, trade policy changes or
restrictions, or import- or export-related governmental sanctions or restrictions; customs actions, including
regulatory enforcement inquiries, holds, detentions, and exclusions; quotas, tariffs or other import-related taxes;
strikes, lock-outs, work stoppages or slowdowns; shortages of supply chain labor, including truck drivers; shipping
capacity constraints, including shortages of related equipment; raw material or other shortages; third-party contract
disputes or inability to maintain favorable contract terms; supply or shipping interruptions or costs; increased costs
or unavailability of fuel; military conflicts or acts of war, as well as any related sanctions or other government or
private responses; acts of terrorism; public health issues, including pandemics or quarantines (such as the
COVID-19 pandemic) and related shut-downs, re-openings, or other actions by government regulators or others;
civil unrest; or other factors beyond our control. In recent years, ports in the U.S. and elsewhere have been
impacted by capacity constraints, port congestion and delays, periodic labor disputes, security issues, weather-
related events, and natural disasters. Disruptions to our supply chain due to any of the factors listed above could
negatively impact our financial performance or financial condition.
If our efforts to maintain the privacy and security of customer, associate, job applicant, business partner,
and Company information are not successful, we could incur substantial costs and reputational damage
and could become subject to litigation and enforcement actions.
Our business, like that of most retailers, involves the collection, processing, retention, management, transmission,
and deletion of personal information (including identifiers, internet activity, preferences, and payment information)
from our customers, associates, job applicants, and business partners, as well as confidential Company information.
We also work with third-party service providers that provide technology, systems and services that we use in
connection with the handling of information. Our information systems, and those of our third-party service providers,
are vulnerable to continually evolving data protection and cybersecurity risks. Unauthorized parties have in the past
gained access, and will continue to attempt to gain access, to these systems and data through fraud or other means
of deceiving our associates or third-party service providers. Hardware, software or applications we develop or obtain
from third parties may contain exploitable vulnerabilities, bugs, or defects in design, maintenance or manufacture or
other problems that could unexpectedly compromise information security. We have experienced and continue to
face the ongoing risk of exploitation of our software providers and our software development and implementation
process, including from coding and process vulnerabilities and the installation of so-called back doors that provide
unauthorized access to systems and data. The increased use of a remote workforce has also expanded the
possible attack surface areas. In addition, the risk of cyber-attacks has increased in connection with Russia’s
invasion of Ukraine and the resulting geopolitical conflict. In light of this and other geopolitical events, nation-state
actors or their supporters may launch retaliatory cyber-attacks, and may attempt to cause supply chain and other
third-party service provider disruptions, or take other geopolitically-motivated retaliatory actions that may disrupt our
Table of Contents
Fiscal 2022 Form 10-K
15

business operations, result in data compromise, or both. Nation-state actors have in the past carried out, and may in
the future carry out, cyber-attacks to achieve their aims and goals, which may include espionage, monetary gain,
disruption, and destruction. To achieve their objectives, nation-state actors and other cyber criminals have used and
may continue to use numerous attack vectors and methods, including use of stolen passwords, social engineering,
phishing, smishing, vishing, identity spoofing, ransomware or other disruptive and destructive malware, supply chain
compromises, and man-in-the-middle and denial of service attacks. The methods used to obtain unauthorized
access, disable or degrade service, or sabotage systems are constantly changing and evolving, increasing in
frequency and sophistication, and may be difficult to anticipate or detect for long periods of time.
To protect against unauthorized access to or use of data, prevent data loss, preserve data integrity, and protect our
own access to systems, we have implemented and regularly review and update systems, processes, and
procedures; third-party assessments and testing; and annual associate training and other specific training initiatives.
However, the ever-evolving threats mean that we and our third-party service providers and business partners must
continually evaluate and adapt our respective systems and processes and overall security environment, as well as
those of companies we acquire. There is no guarantee that the measures we take will be adequate to safeguard
against all threats, including vulnerabilities, data security breaches, system compromises or misuses of data. As we
saw in connection with the data breach we experienced in 2014, any significant compromise or breach of our data
security, whether external or internal, or misuse of customer, associate, job applicant, business partner, or Company
data, could result in significant costs, including costs to investigate and remediate, as well as lost sales, fines,
lawsuits, regulatory investigations, and damage to our reputation. Furthermore, because the techniques used to
obtain unauthorized access, disable or degrade service, or sabotage systems change frequently and may not
immediately produce signs of anomalous activity or compromise, we may be unable to anticipate these techniques
or to implement adequate preventative measures. Additionally, as occurred in the case of the data breach we
experienced in 2014, we or our third-party service providers may not discover any security breach, vulnerability or
compromise of information for a significant period of time after the occurrence of a security incident.
In addition, data governance failures can adversely affect our reputation and business. Our business depends on
our customers’, associates’, job applicants’ and business partners’ willingness to entrust us with their personal
information. Events that adversely affect that trust, including inadequate disclosure to our customers, associates,
job applicants, or business partners of our uses of their information or failing to keep our information technology
systems and our customers’, associates’, job applicants’ and business partners’ personal information secure from
significant attack, theft, damage, loss or unauthorized disclosure or access, whether as a result of our action or
inaction (including human error or malfeasance) or that of our service providers or other third parties, could
adversely affect our brand and harm our reputation. Further, the regulatory environment related to data privacy and
cybersecurity is constantly changing, with new and increasingly rigorous requirements applicable to our business.
The implementation of these requirements has also become more complex. Maintaining our compliance with
evolving requirements, including state privacy laws, requires significant effort and cost, requires changes to our
business practices, and may limit our ability to collect and use certain data to support the customer experience. In
addition, failure to comply with applicable requirements could subject us to fines, sanctions, governmental
investigations, lawsuits or reputational damage. Additionally, our cyber insurance coverage may not be adequate for
liabilities or costs actually incurred, and we cannot be certain that insurance will continue to be available to us on
economically reasonable terms, or at all, or that any insurer will not deny coverage of a future claim.
We are subject to payment-related risks that could increase our operating costs, expose us to fraud or theft,
subject us to potential liability, and potentially disrupt our business.
We accept payments using a variety of methods, including credit and debit cards, our private label credit cards,
cash, checks, PayPal, installment loan programs, trade credit, and gift cards, and we may offer new payment
options over time. Acceptance of these payment options subjects us to rules, regulations, contractual obligations
and compliance requirements, including payment network rules and operating guidelines, data security standards
and certification requirements, and rules governing electronic funds transfers. These requirements may change over
time or be reinterpreted, making compliance more difficult, costly, or uncertain. For certain payment methods,
including credit and debit cards, we pay interchange and other fees, which may increase over time and raise our
operating costs. We rely on third parties to provide payment processing services, including the processing of credit
cards, debit cards, and other forms of electronic payment. If these companies become unable to provide these
services to us, or if their systems are compromised, it could potentially disrupt our business. The payment methods
that we offer, and the selling channels in which we operate, also subject us to potential fraud and theft by threat
actors, who are becoming increasingly more sophisticated, seeking to obtain unauthorized access to or exploit
weaknesses that may exist in our sales, payments and payment processing systems. If we fail to comply with
applicable rules or requirements for the payment methods we accept, or if payment-related data is compromised
Table of Contents
Fiscal 2022 Form 10-K
16

due to a breach or misuse of data, we may be liable for costs incurred by payment card issuing banks and other
third parties or we may be subject to fines and higher transaction fees, or our ability to accept or facilitate certain
types of payments may be impaired. In addition, our customers could lose confidence in certain payment types,
which may result in a shift to other payment types or potential changes to our payment systems that may result in
higher costs. As a result, our business and operating results could be adversely affected.
Our business is subject to seasonal influences, and uncharacteristic or significant weather conditions,
climate change, natural disasters, as well as other catastrophic events, could impact our operations.
Natural disasters, such as hurricanes, tropical storms, fires, floods, droughts or water scarcity, tornadoes, and
earthquakes; unseasonable, unexpected or extreme weather conditions, whether as a result of climate change or
otherwise; acts of terrorism or violence, including active shooter situations; public health concerns, such as
pandemics and quarantines and related shut-downs, re-openings, or other actions by government regulators or
others; civil unrest; military conflicts or acts of war, as well as any related sanctions or other government or private
responses; or similar disruptions and catastrophic events can affect consumer spending and confidence and
consumers’ disposable income, particularly with respect to home improvement or construction projects, and could
have an adverse effect on our financial performance. These types of events can also adversely affect our work force
and prevent associates and customers from reaching our stores and other facilities. They can also, temporarily or
on a long-term basis, disrupt or disable operations of stores, support centers, and portions of our supply chain and
distribution network, including causing reductions in the availability of inventory and disruption of utility services. In
addition, these events may affect our information systems and digital platforms, resulting in disruption to various
aspects of our operations, including our ability to transact with customers and fulfill orders; to communicate with our
stores, facilities, store support centers or senior management; or to access financial or banking systems.
Unseasonable, unexpected or extreme weather conditions such as excessive precipitation, warm temperatures
during the winter season, or prolonged or extreme periods of warm or cold temperatures, could render a portion of
our inventory incompatible with customer needs.
Furthermore, the long-term impacts of climate change, whether involving physical risks (such as extreme weather
conditions) or transition risks (such as regulatory or technology changes) are expected to be widespread and
unpredictable. These changes over time could affect, for example, the availability and cost of or demand for certain
consumer products, commodities, and energy (including utilities), which in turn may impact our ability to procure
certain goods or services for the operation of our business at the quantities and levels we consider optimal.
As a consequence of these or other catastrophic or uncharacteristic events, we may experience interruption to our
operations, increased costs, or losses of property, equipment or inventory, which would adversely affect our revenue
and profitability.
If we fail to identify and develop relationships with a sufficient number of qualified suppliers, or if our
suppliers experience financial difficulties or other challenges, our ability to timely and efficiently access
products that meet our high standards for quality could be adversely affected.
We buy our products from suppliers located around the world, who in turn procure materials from across the globe.
Our ability to continue to identify and develop relationships with qualified suppliers who can satisfy our high
standards for quality and responsible sourcing, as well as our need to access products in a timely and efficient
manner, is a significant challenge. Our ability to access products from our suppliers can be adversely affected by
economic or political instability; civil unrest; military conflicts or acts of war, as well as any related sanctions or other
government or private responses; acts of terrorism or violence; public health issues (including pandemics and
related impacts); the financial instability of suppliers; suppliers’ noncompliance with applicable laws; contract
disputes or inability to maintain favorable contract terms; trade restrictions; tariffs; currency exchange rates;
disruptions in our suppliers’ logistics or supply chain networks or information technology systems; inability to sell
certain products due to customs actions, including regulatory enforcement inquiries, holds, detentions, and
exclusions; raw material or other shortages; and other factors beyond our or our suppliers’ control. If we are unable
to access products to meet our customers’ demands and expectations in a timely and efficient manner, our sales
and gross margin results may be adversely impacted.
Failure to achieve and maintain a high level of product and service quality and safety and ensure
compliance with responsible sourcing laws and standards could damage our reputation with customers,
expose us to litigation or enforcement actions, and negatively impact our sales and results of operations.
Product and service quality issues could negatively impact customer confidence in our brands and our Company. If
our product and service offerings do not meet applicable product standards or our customers’ expectations
regarding safety or quality, we could experience lost sales and increased costs and be exposed to legal, financial
Table of Contents
Fiscal 2022 Form 10-K
17

and reputational risks, as well as governmental enforcement actions. Actual, potential or perceived product safety
concerns, including health-related concerns, could expose us to litigation or government enforcement actions, and
could result in costly product recalls and other liabilities. We may not be successful in obtaining adequate
contractual indemnification and insurance coverage from our suppliers and service providers, which may result in
claims having an adverse effect on our business, financial condition and results of operations. Even with adequate
insurance and indemnification, our reputation as a provider of high-quality products and services, including both
national brand names and our proprietary products, could suffer, damaging our reputation and impacting customer
loyalty. In addition, we and our customers have expectations around responsible sourcing, which is an increasing
focus of government regulators as well. All of our suppliers must comply with our responsible sourcing standards,
which cover a variety of expectations across multiple areas of social compliance, including supply chain
transparency, health and safety, environmental laws and regulations, compensation, hours of work, and prohibitions
on child and forced labor. We have a responsible sourcing audit process, but we are also dependent on our
suppliers to ensure that the products and services we provide to our customers comply with our standards and
applicable law. Actual, potential or perceived supplier non-compliance could, and in certain instances in the past
has, exposed us to litigation or governmental enforcement actions or resulted in costly product recalls; inability to
sell certain products due to customs actions, including regulatory enforcement inquiries, holds, detentions, and
exclusions; and/or other liabilities.
Our proprietary products subject us to certain increased risks, including regulatory, product liability,
intellectual property, supplier relations, and reputational risks.
In addition to other product-related risks discussed in this section, as we expand our proprietary product offerings,
we may become subject to increased risks due to our greater role in the design, manufacture, marketing and sale of
those products. The risks include greater responsibility to administer and comply with applicable regulatory
requirements, increased potential product liability and product recall exposure, and increased potential reputational
risks related to the responsible sourcing of those products. To effectively execute on our product differentiation
strategy, we must also be able to successfully protect our proprietary rights and successfully navigate and avoid
claims related to the proprietary rights of third parties. In addition, an increase in sales of our proprietary products
may adversely affect sales of our suppliers’ products, which in turn could adversely affect our relationships with
certain of our suppliers. Any failure to appropriately address some or all of these risks could damage our reputation
and have an adverse effect on our business, results of operations, and financial condition.
If we are unable to effectively manage our installation services business, we could suffer lost sales and be
subject to fines, lawsuits, reputational damage or the loss of our general contractor licenses.
We act as a general contractor to provide installation services to our DIFM customers through professional third-
party licensed and insured installers. As such, we are subject to regulatory requirements and risks applicable to
general contractors, which include management of background checks, licensing, permitting, and handling of
environmental risks, as well as quality of work performed by our third-party installers. We have established
processes and procedures to manage these requirements and manage customer satisfaction with the services
provided by our third-party installers. However, as we experienced in part with our recent EPA investigation and
resulting consent decree in April 2021, if we fail to manage these processes effectively, collect the appropriate
documentation, perform regular job site inspections, or provide proper oversight of these services, we could suffer
lost sales, fines, lawsuits, or governmental enforcement actions for violations of regulatory requirements, as well as
claims for property damage or personal injury. In addition, we may suffer damage to our reputation or the loss of our
general contractor licenses, which could adversely affect our business.
LEGAL, FINANCIAL, REGULATORY, GLOBAL AND OTHER EXTERNAL RISKS
Uncertainty regarding the housing market, economic conditions, political and social climate, public health
issues, and other factors beyond our control could adversely affect demand for our products and services,
our costs of doing business, and our financial performance.
Our financial performance depends significantly on the stability of the housing and home improvement markets, as
well as general economic conditions, including changes in gross domestic product. Adverse conditions in or
uncertainty about these markets, the economy or the political or social climate could adversely impact our
customers’ confidence or financial condition, causing them to decide against purchasing home improvement
products and services, causing them to delay purchasing decisions, or impacting their ability to pay for products and
services. Other factors beyond our control – including unemployment and foreclosure rates; inventory loss due to
theft (including as a result of organized retail crime); interest rate fluctuations; inflation or deflation; fuel and other
energy costs; raw material or other shortages; labor and healthcare costs; the availability of financing; the state of
Table of Contents
Fiscal 2022 Form 10-K
18

the credit markets, including mortgages, home equity loans and consumer credit; changes in tax rates and policy;
weather and natural disasters (including the potential impacts of climate change); acts of terrorism or violence,
including active shooter situations; public health issues, including pandemics and related impacts; military conflicts
or acts of war, as well as any related sanctions or other government or private responses; and civil unrest, could
further adversely affect demand for our products and services, our costs of doing business, and our financial
performance. A number of merchandise categories have been impacted by higher inflation than that which we have
experienced in recent years due to, among other things, the continuing impacts of the COVID-19 pandemic, global
supply chain disruptions, and the uncertain economic and geopolitical environment. If inflation increases costs
beyond our ability to control our related costs, we may not be able to adjust prices or use our portfolio strategy to
sufficiently offset the effect without negatively impacting consumer demand or our gross margin. Further, our MRO
customers, who have higher spend and longer-term relationships than a typical retail customer, primarily use trade
credit to finance their purchases, and some of our Pros use trade credit in order to purchase our products. As a
result, their ability to pay is highly dependent on the economic strength of the industry in their areas. If these
customers are unable to repay the trade credit from us, we may face greater default risk, which could reduce our
cash flow and adversely affect our results of operations.
Our costs of doing business could increase as a result of changes in, expanded enforcement of, or
adoption of new federal, state or local laws and regulations.
We are subject to various federal, state and local laws and regulations that govern numerous aspects of our
business. In recent years, a number of new laws and regulations have been adopted, there has been expanded
enforcement of certain existing laws and regulations by federal, state and local agencies, and the interpretation of
certain laws and regulations has become increasingly complex. These laws and regulations, and related
interpretations and enforcement activity, may change as a result of a variety of factors, including political, economic
or social events. Changes in, expanded enforcement of, or adoption of new federal, state or local laws and
regulations governing minimum wage or living wage requirements; the classification of exempt and non-exempt
employees; the distinction between employees and contractors; other wage, labor or workplace regulations;
healthcare; data privacy and cybersecurity; the sale, marketing, sourcing, and pricing of some of our products;
transportation, logistics and interstate delivery operations, including Department of Transportation regulations on
vehicles and drivers; international trade; supply chain transparency; taxes, including changes to corporate tax rates;
restrictions on carbon dioxide and other greenhouse gas emissions; competition and antitrust requirements; ESG
programs, transparency and reporting; unclaimed property; energy costs and consumption; or hazardous waste
disposal and other environmental matters, including with respect to our installation services business, could
increase our costs of doing business or impact our sales, operations or profitability.
If we cannot successfully manage the unique challenges presented by international markets, we may not be
successful in our international operations and our sales and profitability may be negatively impacted.
Our ability to successfully conduct retail operations in, and source products and materials from, international
markets is affected by many of the same risks we face in our U.S. operations, as well as unique costs and
difficulties of managing international operations. Our international operations, including any expansion in
international markets, may be adversely affected by local laws and customs, U.S. laws applicable to foreign
operations and other foreign legal and regulatory constraints, as well as political, social and economic conditions.
Risks inherent in international operations also include, among others, potential adverse tax consequences;
international trade disputes, trade policy changes or potential tariffs and other import-related taxes and controls;
inability to sell certain products due to customs actions, including regulatory enforcement inquiries, holds,
detentions, and exclusions; greater difficulty in enforcing intellectual property rights; limitations on access to ports;
risks associated with the Foreign Corrupt Practices Act and local anti-bribery law compliance; military conflicts or
acts of war, as well as any related sanctions or other government or private responses; compliance with forced labor
laws; and challenges in our ability to identify and gain access to local suppliers. For example, trade tensions
between the U.S. and China have led to a series of significant tariffs on the importation of certain product
categories. As a portion of our retail products are sourced, directly or indirectly, outside of the U.S., major changes
in tax or trade policies, tariffs or trade relations could adversely impact the cost of, demand for, and profitability of
retail product sales in our U.S. locations. Other countries may also change their business and trade policies in
anticipation of or in response to increased import tariffs and other changes in U.S. trade policy and regulations. In
addition, our operations in international markets create risk due to foreign currency exchange rates and fluctuations
in those rates, which may adversely impact our sales and profitability.
Table of Contents
Fiscal 2022 Form 10-K
19

The inflation or deflation of commodity and other prices could affect our prices, demand for our products,
our sales and our profit margins.
Prices of certain commodity products, including lumber and other raw materials, are historically volatile and are
subject to fluctuations arising from changes in domestic and international supply and demand, inflationary
pressures, labor costs, competition, market speculation, government regulations, tariffs and trade restrictions,
natural disasters, geopolitical conflicts, and periodic delays in delivery. For example, Russia’s invasion of Ukraine
and the related international responses have exacerbated inflationary pressures, including causing increases in
commodity prices as well as fuel and other energy costs. Rapid and significant changes in commodity and other
prices, such as changes in lumber prices, and our ability to pass them on to our customers or manage them through
our portfolio strategy, may affect the demand for our products, our sales and our profit margins. If product cost
inflation increases beyond our ability to control our related costs, we may not be able to adjust prices to sufficiently
offset the effect of the various cost increases without negatively impacting consumer demand.
The continuing impacts of the COVID-19 pandemic are highly unpredictable, volatile, and uncertain, and
could adversely affect our business operations, demand for our products and services, our costs of doing
business, availability of labor, access to inventory, supply chain operations, our ability to predict future
performance, our exposure to litigation, and our financial performance, among other things.
The COVID-19 pandemic has caused significant public health concerns as well as economic disruption, uncertainty,
and volatility, all of which have impacted our business. While we have taken numerous steps to mitigate the impact
of the pandemic on our results of operations, there can be no assurance that these efforts will continue to be
successful. While efforts to address the pandemic, including vaccinations, have fostered progress and many
restrictions have relaxed, due to numerous uncertainties and factors beyond our control, we are unable to predict
the ongoing impact that the pandemic and recovery efforts will have on our business, results of operations, cash
flows, and financial condition. These factors and uncertainties include, but are not limited to:
• the ongoing impact of COVID-19, including whether there are further “waves” or other continued increases
or spikes in the number of COVID-19 cases in future periods in areas in which we or our suppliers operate,
and the potential for longer-term impact as COVID-19 becomes endemic;
• the rapidly changing and fluid circumstances caused by the pandemic and efforts to contain and recover
from it and our ability to respond quickly enough or appropriately to those circumstances;
• the duration and degree of governmental, business or other actions in response to the pandemic, including
but not limited to quarantine or shut-down measures and other governmental orders, or the termination of
those measures; fiscal policy changes; or additional measures that may yet be enacted;
• the health of, and longer-term effect of the pandemic on, our associates and our ability to maintain staffing
needs to effectively operate our business;
• changes in labor markets affecting us and our suppliers, including labor shortages and increased employee
turnover;
• evolving macroeconomic factors, including general economic uncertainty, unemployment rates, inflation and
deflation, rising interest rates, and recessionary pressures, and their ongoing impact on consumer
confidence, economic well-being, spending, and shopping behaviors;
• impacts – financial, operational or otherwise – on our supply chain, including on manufacturers or suppliers
of our products and logistics or transportation providers, and on our service providers, subcontractors, or
other business partners;
• the effects on our internal control environment and data security as a result of the remote and hybrid work
environment;
• the impact of regulatory and judicial changes in liability for workers’ compensation;
• potential increases in insurance premiums, medical claims costs, and workers’ compensation claims costs;
and
• the impact of litigation or claims from customers, associates, suppliers, regulators or other third parties
relating to COVID-19 or our actions in response thereto.
In addition, as the pandemic subsides, customers have shifted more of their spending away from home
improvement and back to other areas, compared to the historic levels of home improvement spending we saw
during the heights of the pandemic, which may have an adverse impact on our sales.
The above factors and uncertainties, or others of which we are not currently aware, may result in adverse impacts to
our business, results of operations, cash flows, and financial condition. In addition to the factors above, the
Table of Contents
Fiscal 2022 Form 10-K
20

COVID-19 pandemic has increased a number of other risks to our business, including but not limited to those
discussed below and elsewhere in these Risk Factors:
Associate and Customer Safety-Related Risks. The health and safety of our associates and customers are of
primary concern to our management team. In response to the COVID-19 pandemic, we took several steps to
support our associates, including expanding certain compensation and benefits to help alleviate some of the
challenges our associates were facing as a result of COVID-19, and adopted a number of enhanced safety
measures in our stores and other facilities. We have transitioned from these temporary pay and benefits programs,
as well as many of the enhanced safety measures. However, due to the unpredictable nature of COVID-19 and the
consequences of our actions, we may see unexpected outcomes from rolling back safety measures as conditions
evolve, particularly if there are further outbreaks. If we do not respond appropriately to any further COVID-19
outbreaks, if our customers or associates do not participate in safety measures, or if rolling back safety measures
results in additional outbreaks, the well-being of our associates and customers could be at risk. Furthermore, any
failure to appropriately respond, or the perception of an inadequate response, could cause reputational harm to our
brand and/or subject us to claims and litigation from associates, customers, suppliers, regulators or other third
parties. Additionally, we have faced, and may continue to face, periodic labor shortages at our stores due to
COVID-19 and other illnesses like influenza that were less prevalent during the height of the pandemic, which can
result in modifications to our operations and negatively impact our business, costs and results of operations.
Additionally, some jurisdictions have taken measures intended to expand the availability of workers’ compensation
or to change the presumptions applicable to workers compensation measures. These actions may increase our
exposure to workers’ compensation claims and increase our cost of insurance.
Supply Chain-Related Risks. Circumstances related to the COVID-19 pandemic significantly impacted the global
supply chain, with restrictions and limitations on business activities and impacts of the COVID-19 pandemic causing
cost increases, labor shortages, capacity constraints, disruptions and delays. These issues, which may continue or
expand depending on the progression of the pandemic, have placed strain on the domestic and international supply
chain, which has affected and may continue to negatively affect the flow or availability of certain products. Even if
we are able to find alternate sources for certain products, they may cost more or require us to incur higher
transportation costs, which could adversely impact our profitability and financial condition. Similarly, increased
demand for online purchases of products impacted our fulfillment operations, as well as those of our third-party
carriers, resulting in delays in delivering products to customers. The operation of our distribution and fulfillment
centers is crucial to our business operations. We and our suppliers have experienced, and may continue to
experience, labor shortages at some of our distribution and fulfillment centers, and any such labor shortages,
whether temporary or sustained, may adversely impact the flow or availability of products to our stores and
customers. Any of these circumstances could impair our ability to meet customer demand for products and result in
lost sales, increased supply chain costs, or damage to our reputation.
To the extent the COVID-19 pandemic and related recovery efforts continue to adversely affect the U.S. and global
economy and/or to adversely affect our business, results of operations, cash flows, or financial condition, they may
also heighten other risks described in this section and other SEC filings, including but not limited to those related to
consumer behavior and expectations, competition, brand and reputation, implementation of strategic initiatives,
cybersecurity threats, associate and customer privacy, technology systems disruption, supply chain disruptions,
labor availability and cost, litigation, and regulatory requirements.
We may incur property, casualty or other losses not covered by our insurance.
We are predominantly self-insured for a number of different risk categories, such as general liability (including
product liability), workers’ compensation, employee group medical, employment practices liability and wage and
hour claims, automobile claims, and network security and privacy liability, with insurance coverage for certain
catastrophic risks above the self-insurance levels. The types and amounts of insurance may vary from time to time
based on our decisions with respect to risk retention and regulatory requirements. The occurrence of significant
claims, a substantial rise in costs to maintain our insurance, the failure to maintain adequate insurance coverage, or
disputes with insurers regarding coverage could have an adverse impact on our financial condition and results of
operations.
Changes in accounting standards and subjective assumptions, estimates and judgments by management
related to complex accounting matters could significantly affect our financial results or financial condition.
GAAP and related accounting pronouncements, implementation guidelines and interpretations with regard to a wide
range of matters that are relevant to our business, such as asset impairment, inventories, lease obligations, self-
insurance, vendor allowances, tax matters, business combinations, and litigation, are complex and involve many
Table of Contents
Fiscal 2022 Form 10-K
21
subjective assumptions, estimates and judgments. Changes in accounting standards or their application or
interpretation, or changes in underlying assumptions, estimates or judgments, could significantly change our
reported or expected financial performance or financial condition. The implementation of new accounting standards
could also require certain systems, internal process, internal controls, and other changes that could increase our
operating costs.
We are involved from time to time in a number of legal, regulatory and governmental enforcement
proceedings, and while we cannot predict the outcomes of those proceedings and other contingencies with
certainty, some of these outcomes may adversely affect our operations or increase our costs.
We are involved in a number of legal proceedings and regulatory matters, including government inquiries and
investigations, and consumer, employment, tort and other litigation that arise from time to time in the ordinary
course of business. Litigation is inherently unpredictable, and the outcome of some of these proceedings and other
contingencies could require us to take or refrain from taking actions which could adversely affect our operations or
could result in excessive adverse verdicts, fines, or results. Additionally, as we have seen in the past, involvement in
these lawsuits, investigations and inquiries, and other proceedings, as well as compliance with any settlements or
consent decrees that result from those proceedings, can involve significant expense, divert management’s attention
and resources from other matters, and impact the reputation of the Company.
Item 1B. Unresolved Staff Comments.
Not applicable.
Item 2. Properties.
The following table presents the percentage of our owned versus leased facilities in operation at the end of fiscal
2022, along with the total square footage:
square footage in millions
Owned Leased
Total Square
Footage
Stores
(1)
89 % 11 % 240.9
Warehouses and distribution centers
(2)
4 % 96 % 103.1
Offices and other
(3)
21 % 79 % 5.2
Total 349.2
—————
(1) Our owned stores include those subject to ground leases.
(2) We operated over 400 warehouses and distribution centers at the end of fiscal 2022.
(3) Our Store Support Center (corporate headquarters) is located in Atlanta, GA.
Table of Contents
Fiscal 2022 Form 10-K
22
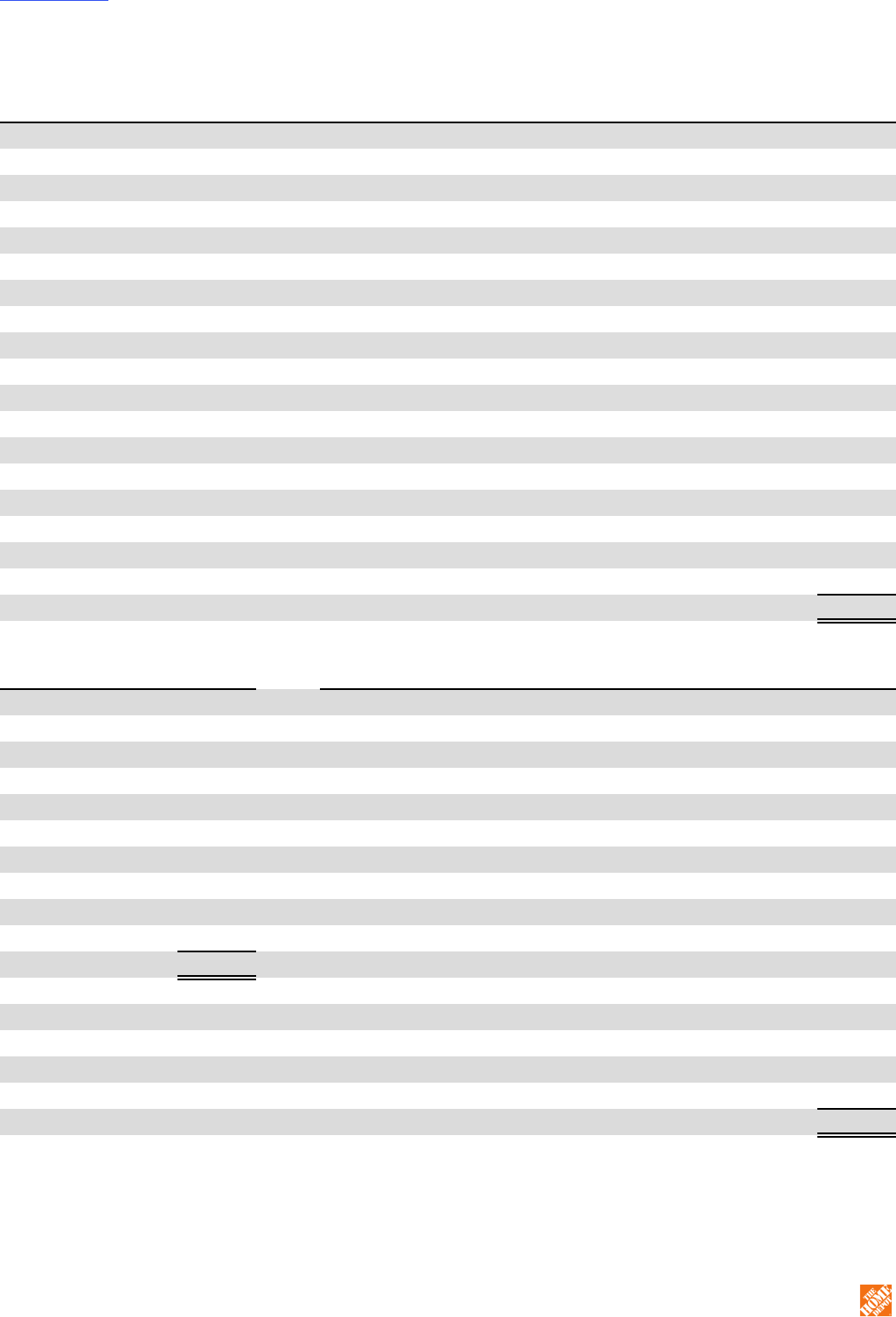
The following table presents our U.S. store locations (including the Commonwealth of Puerto Rico and the territories
of the U.S. Virgin Islands and Guam) at the end of fiscal 2022:
U.S. Stores U.S. Stores U.S. Stores
Alabama
28
Kentucky
14
Ohio
70
Alaska
7
Louisiana
28
Oklahoma
16
Arizona
57
Maine
11
Oregon
27
Arkansas
14
Maryland
41
Pennsylvania
70
California
246
Massachusetts
45
Puerto Rico
10
Colorado
46
Michigan
70
Rhode Island
8
Connecticut
30
Minnesota
33
South Carolina
26
Delaware
9
Mississippi
14
South Dakota
1
District of Columbia
1
Missouri
34
Tennessee
39
Florida
156
Montana
6
Texas
182
Georgia
90
Nebraska
8
Utah
22
Guam
1
Nevada
21
Vermont
3
Hawaii
7
New Hampshire
20
Virgin Islands
2
Idaho
11
New Jersey
67
Virginia
50
Illinois
76
New Mexico
13
Washington
46
Indiana
24
New York
101
West Virginia
6
Iowa
10
North Carolina
40
Wisconsin
27
Kansas
16
North Dakota
2
Wyoming
5
Total U.S. 2,007
The following table presents our store locations outside of the U.S. at the end of fiscal 2022:
Canada Stores Mexico Stores Mexico Stores
Alberta
27
Aguascalientes
2
Nayarit
1
British Columbia
26
Baja California
6 Nuevo León 13
Manitoba
6
Baja California Sur
2 Oaxaca 1
New Brunswick
3
Campeche
2 Puebla 5
Newfoundland
1
Chiapas
2
Querétaro
5
Nova Scotia
4
Chihuahua
6
Quintana Roo
3
Ontario
88
Coahuila
5
San Luis Potosí
2
Prince Edward Island
1
Colima
2
Sinaloa
5
Quebec
22
Distrito Federal
10
Sonora
4
Saskatchewan
4
Durango
2
State of Mexico
16
Total Canada 182 Guanajuato 5
Tabasco
1
Guerrero
2
Tamaulipas
5
Hidalgo
1
Tlaxcala
1
Jalisco
9
Veracruz
5
Michoacán
4
Yucatán
2
Morelos
3
Zacatecas
1
Total Mexico 133
Item 3. Legal Proceedings.
The Company is party to various legal proceedings arising in the ordinary course of its business, but is not currently
a party to any legal proceeding that management believes will have a material adverse effect on our consolidated
financial position or our results of operations.
Table of Contents
Fiscal 2022 Form 10-K
23
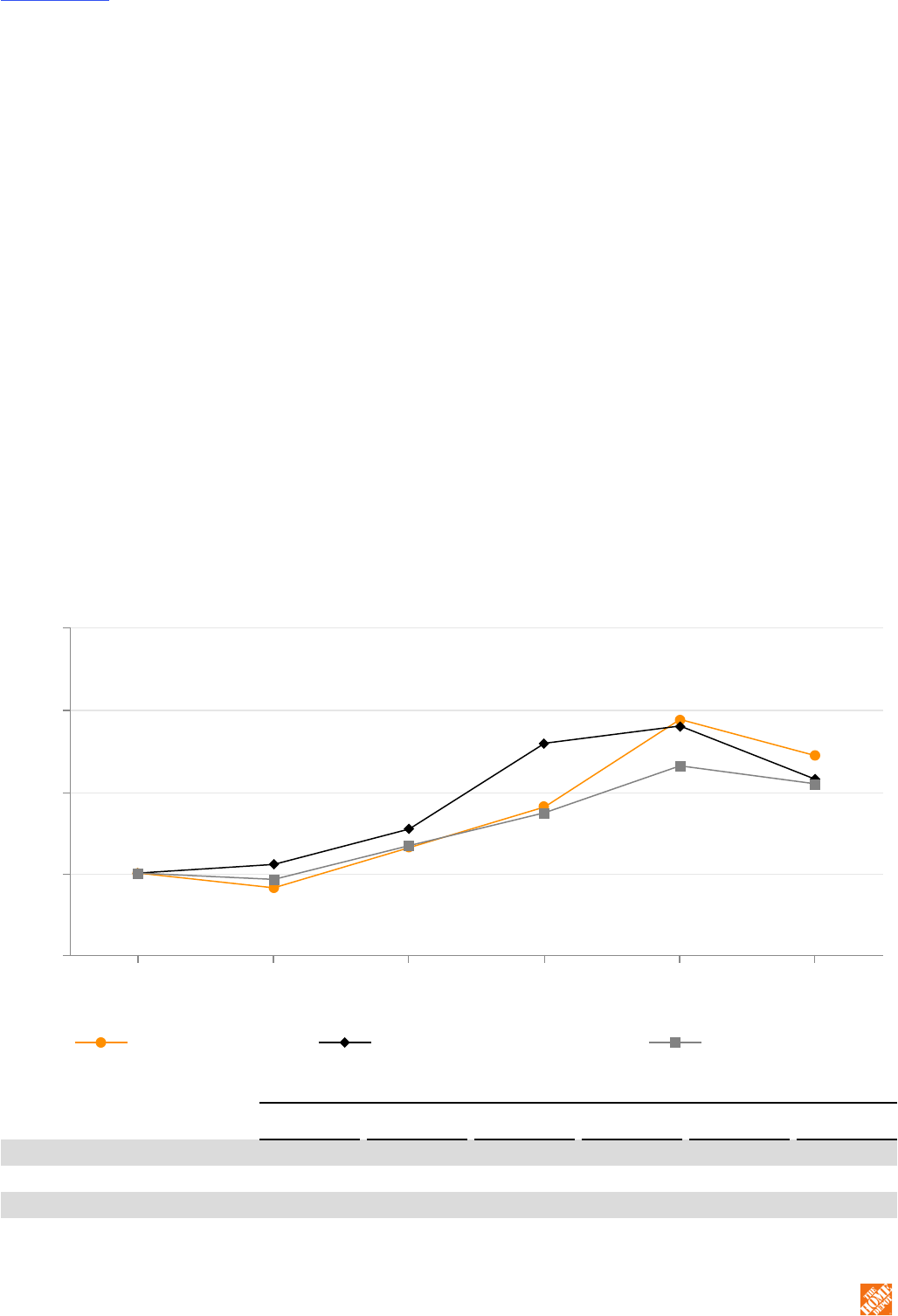
SEC regulations require us to disclose certain information about proceedings arising under federal, state or local
environmental regulations if we reasonably believe that such proceedings may result in monetary sanctions above a
stated threshold. Pursuant to SEC regulations, the Company uses a threshold of $1 million for purposes of
determining whether disclosure of any such proceedings is required.
Item 4. Mine Safety Disclosures.
Not applicable.
PART II
Item 5. Market for Registrant’s Common Equity, Related Stockholder Matters and Issuer
Purchases of Equity Securities.
Since April 19, 1984, our common stock has been listed on the NYSE, trading under the symbol “HD.” We paid our
first cash dividend on June 22, 1987 and have paid a cash dividend during each subsequent quarter. While we
currently expect a cash dividend to be paid in the future, future dividend payments will depend on our earnings,
capital requirements, financial condition, and other factors considered relevant by our Board of Directors.
At March 1, 2023, there were approximately 110,000 holders of record of our common stock and approximately
4,938,000 additional “street name” holders whose shares are held of record by banks, brokers, and other financial
institutions.
STOCK PERFORMANCE GRAPH
The graph and table below present our cumulative total shareholder returns relative to the performance of the S&P
Retail Composite Index and the S&P 500 Index for the five most recent fiscal years. The graph assumes $100 was
invested at the closing price of our common stock on the NYSE and in each index on the last trading day of the
fiscal year ended January 28, 2018 and assumes that all dividends were reinvested on the date paid. The points on
the graph represent fiscal year-end amounts based on the last trading day in each fiscal year.
The Home Depot S&P Retail Composite Index S&P 500 Index
January 28,
2018
February 3,
2019
February 2,
2020
January 31,
2021
January 30,
2022
January 29,
2023
$50
$100
$150
$200
$250
Fiscal Year Ended
January 28,
2018
February 3,
2019
February 2,
2020
January 31,
2021
January 30,
2022
January 29,
2023
The Home Depot $ 100.00 $ 90.96 $ 115.58 $ 140.52 $ 194.16 $ 171.96
S&P Retail Composite Index 100.00 105.29 126.99 179.55 190.14 157.46
S&P 500 Index 100.00 96.12 116.83 136.97 165.71 154.70
Table of Contents
Fiscal 2022 Form 10-K
24
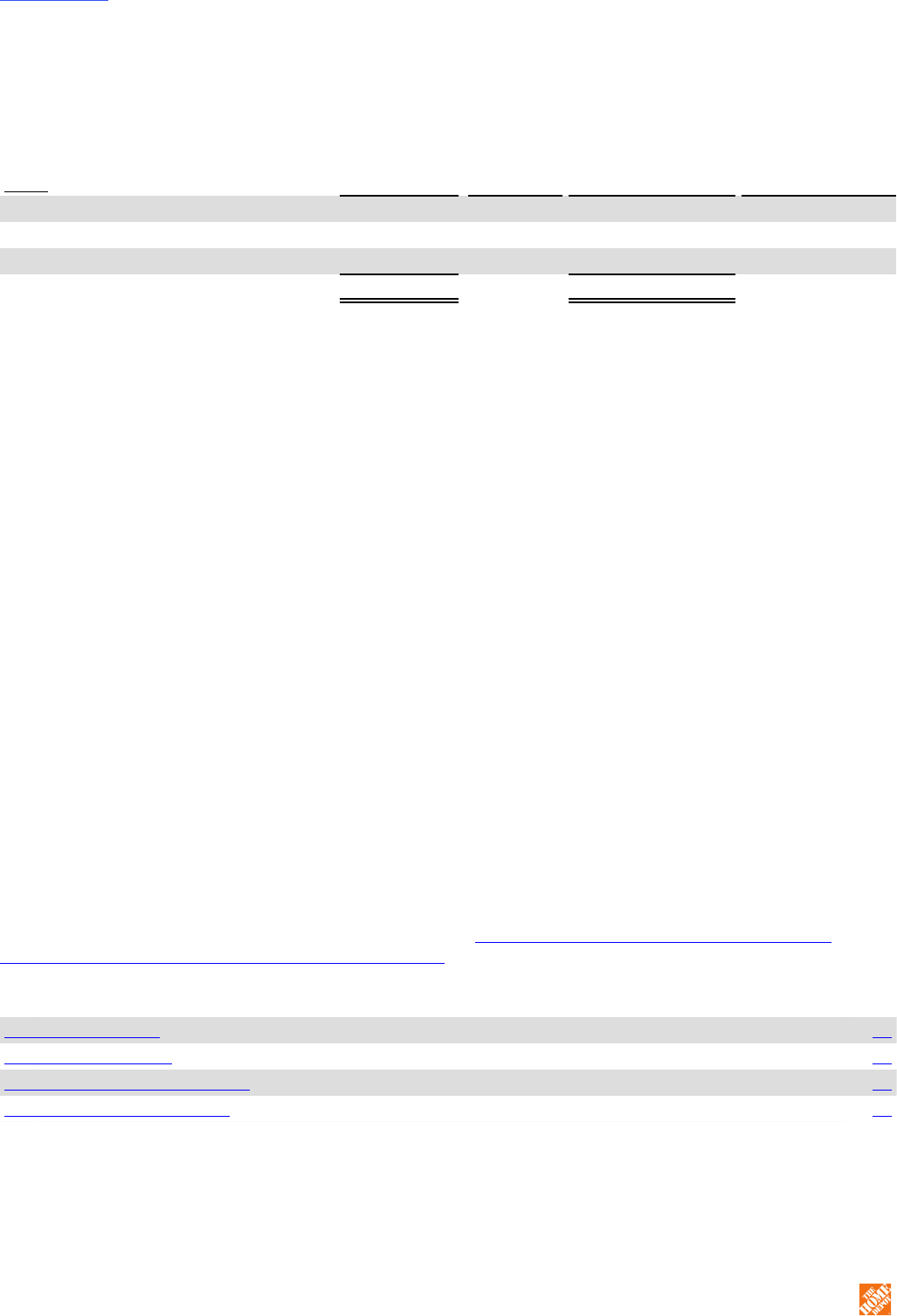
ISSUER PURCHASES OF EQUITY SECURITIES
The following table presents the number and average price of shares purchased in each fiscal month of the fourth
quarter of fiscal 2022:
Period
Total Number of
Shares
Purchased
(1)
Average
Price
Paid
Per Share
(1)
Total Number of
Shares Purchased
as Part of Publicly
Announced Program
(2)
Dollar Value of
Shares
that May Yet
Be Purchased
Under the Program
(2)
October 31, 2022 – November 27, 2022
1,989,907 $ 307.36 1,984,980 $ 13,384,512,799
November 28, 2022 – December 25, 2022
2,797,536 321.81 2,796,708 12,484,515,553
December 26, 2022 – January 29, 2023
2,242 321.75 — 12,484,515,553
Total
4,789,685 315.80 4,781,688
—————
(1) These amounts include repurchases pursuant to our Omnibus Stock Incentive Plan, as Amended and Restated May 19, 2022, and our 1997
Omnibus Stock Incentive Plan (collectively, the “Plans”). Under the Plans, participants may surrender shares as payment of applicable tax
withholding on the vesting of restricted stock. Participants in the Plans may also exercise stock options by surrendering shares of common
stock that the participants already own as payment of the exercise price. Shares so surrendered by participants in the Plans are
repurchased pursuant to the terms of the Plans and applicable award agreement and not pursuant to publicly announced share repurchase
programs.
(2) On August 18, 2022, our Board of Directors approved a $15.0 billion share repurchase authorization that replaced the previous
authorization of $20.0 billion, which was approved on May 20, 2021. This new authorization does not have a prescribed expiration date.
SALES OF UNREGISTERED SECURITIES
During the fourth quarter of fiscal 2022, we issued 483 deferred stock units under the Home Depot, Inc.
Nonemployee Directors’ Deferred Stock Compensation Plan pursuant to the exemption from registration provided
by Section 4(a)(2) of the Securities Act and Rule 506 of the SEC’s Regulation D thereunder. The deferred stock
units were credited during the fourth quarter of fiscal 2022 to the accounts of those non-employee directors who
elected to receive all or a portion of board retainers in the form of deferred stock units instead of cash. The deferred
stock units convert to shares of common stock on a one-for-one basis following a termination of service as
described in this plan.
During the fourth quarter of fiscal 2022, we credited 923 deferred stock units to participant accounts under the
Restoration Plans pursuant to an exemption from the registration requirements of the Securities Act for involuntary,
non-contributory plans. The deferred stock units convert to shares of common stock on a one-for-one basis
following a termination of service as described in these plans.
Item 6. Reserved.
Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations.
The following discussion provides an analysis of the Company’s financial condition and results of operations from
management's perspective and should be read in conjunction with the consolidated financial statements and related
notes included in this report. The discussion in this Form 10-K generally focuses on fiscal 2022 compared to fiscal
2021. A discussion of our results of operations and changes in financial condition for fiscal 2021 compared to fiscal
2020 has been excluded from this report, but can be found in Part II, Item 7. Management’s Discussion and
Analysis of Financial Condition and Results of Operations of our Form 10-K for fiscal 2021.
TABLE OF CONTENTS
Executive Summary 26
Results of Operations 27
Liquidity and Capital Resources 29
Critical Accounting Estimates 32
Table of Contents
Fiscal 2022 Form 10-K
25
EXECUTIVE SUMMARY
The following table presents highlights of our annual financial results:
dollars in millions, except per share data
Fiscal Fiscal Fiscal
2022 2021 2020
Net sales $ 157,403 $ 151,157 $ 132,110
Net earnings 17,105 16,433 12,866
Diluted earnings per share $ 16.69 $ 15.53 $ 11.94
Net cash provided by operating activities $ 14,615 $ 16,571 $ 18,839
Payments for businesses acquired, net — 421 7,780
Proceeds from long-term debt, net of discounts 6,942 2,979 7,933
Repayments of long-term debt 2,491 1,532 2,872
We reported net sales of $157.4 billion in fiscal 2022. Net earnings were $17.1 billion, or $16.69 per diluted share.
During fiscal 2022, we opened two new stores in the U.S. and four new stores in Mexico, and we lost one store in
the U.S. due to a fire, resulting in a total store count of 2,322 at January 29, 2023. At the end of fiscal 2022, a total
of 315 of our stores, or 13.6% of our total store count, were located in Canada and Mexico. Total sales per retail
square foot were $627.17 in fiscal 2022. Our inventory turnover ratio was 4.2 times at the end of fiscal 2022,
compared to 5.2 times at the end of fiscal 2021. The decrease in our inventory turnover ratio was driven by an
increase in average inventory levels during fiscal 2022 resulting from strategic investments to promote higher in-
stock levels and pull forward merchandise in response to ongoing global supply chain disruption, as well as
continued investment in our new supply chain facilities and carryover of some spring seasonal inventory.
We generated $14.6 billion of cash flow from operations and issued $6.9 billion of long-term debt, net of discounts,
during fiscal 2022. This cash flow, together with cash on hand, was used to fund cash payments of $7.8 billion for
dividends and $6.7 billion for share repurchases. In addition, we repaid $2.5 billion of long-term debt and $1.0 billion
of net short-term debt and funded $3.1 billion in capital expenditures during fiscal 2022. In February 2023, we
announced a 10% increase in our quarterly cash dividend to $2.09 per share.
Our ROIC was 44.6% for fiscal 2022 and 44.7% for fiscal 2021. See the Non-GAAP Financial Measures section
below for our definition and calculation of ROIC, as well as a reconciliation of NOPAT, a non-GAAP financial
measure, to net earnings (the most comparable GAAP financial measure).
Table of Contents
Fiscal 2022 Form 10-K
26
RESULTS OF OPERATIONS
The following table presents the percentage relationship between net sales and major categories in our
consolidated statements of earnings:
Fiscal Fiscal Fiscal
2022 2021 2020
dollars in millions $
% of Net
Sales $
% of Net
Sales $
% of Net
Sales
Net sales $ 157,403 $ 151,157 $ 132,110
Gross profit 52,778 33.5 % 50,832 33.6 % 44,853 34.0 %
Operating expenses:
Selling, general and administrative 26,284 16.7 25,406 16.8 24,447 18.5
Depreciation and amortization 2,455 1.6 2,386 1.6 2,128 1.6
Total operating expenses 28,739 18.3 27,792 18.4 26,575 20.1
Operating income 24,039 15.3 23,040 15.2 18,278 13.8
Interest and other (income) expense:
Interest income and other, net (55) — (44) — (47) —
Interest expense 1,617 1.0 1,347 0.9 1,347 1.0
Interest and other, net 1,562 1.0 1,303 0.9 1,300 1.0
Earnings before provision for income taxes 22,477 14.3 21,737 14.4 16,978 12.9
Provision for income taxes 5,372 3.4 5,304 3.5 4,112 3.1
Net earnings $ 17,105 10.9 % $ 16,433 10.9 % $ 12,866 9.7 %
—————
Note: Certain percentages may not sum to totals due to rounding.
% Change
Selected financial and sales data:
Fiscal Fiscal Fiscal Fiscal Fiscal
2022 2021 2020 2022 vs. 2021 2021 vs. 2020
Comparable sales (% change) 3.1 % 11.4 % 19.7 % N/A N/A
Comparable customer transactions (% change)
(1)
(5.4) % (0.1) % 8.6 % N/A N/A
Comparable average ticket (% change)
(1)
8.8 % 11.7 % 10.5 % N/A N/A
Customer transactions (in millions)
(1)
1,666.4 1,759.7 1,756.3 (5.3) % 0.2 %
Average ticket
(1) (2)
$90.36 $83.04 $74.32 8.8 % 11.7 %
Sales per retail square foot
(1) (3)
$627.17 $604.74 $543.74 3.7 % 11.2 %
Diluted earnings per share
$16.69 $15.53 $11.94 7.5 % 30.1 %
—————
(1) Does not include results for HD Supply, including the legacy Interline Brands business, which was integrated into HD Supply during the
fourth quarter of fiscal 2021.
(2) Average ticket represents the average price paid per transaction and is used by management to monitor the performance of the Company,
as it represents a primary driver in measuring sales performance.
(3) Sales per retail square foot represents sales divided by retail store square footage. Sales per retail square foot is a measure of the
efficiency of sales based on the total square footage of our stores and is used by management to monitor the performance of the
Company’s retail operations as an indicator of the productivity of owned and leased square footage for these retail operations.
FISCAL 2022 COMPARED TO FISCAL 2021
Sales
We assess our sales performance by evaluating both net sales and comparable sales.
Net Sales. Net sales for fiscal 2022 increased $6.2 billion, or 4.1%, to $157.4 billion. The increase in net sales for
fiscal 2022 primarily reflected the impact of positive comparable sales driven by an increase in comparable average
ticket, partially offset by a decrease in comparable customer transactions. A stronger U.S. dollar negatively
impacted net sales by $339 million in fiscal 2022.
Table of Contents
Fiscal 2022 Form 10-K
27

Online sales, which consist of sales generated online through our websites and mobile applications for products
picked up at our stores or delivered to customer locations, represented 14.2% of net sales and grew by 7.4% during
fiscal 2022 compared to fiscal 2021. The increase in online sales in fiscal 2022 was a result of customers continuing
to leverage our digital platforms and reflects our ongoing investments to enhance these platforms and related
fulfillment capabilities, which support our interconnected retail strategy.
Comparable Sales. Comparable sales is a measure that highlights the performance of our existing locations and
websites by measuring the change in net sales for a period over the comparable prior-period of equivalent length.
Comparable sales includes sales at all locations, physical and online, open greater than 52 weeks (including
remodels and relocations) and excludes closed stores. Retail stores become comparable on the Monday following
their 52
nd
week of operation. Acquisitions are typically included in comparable sales after they have been owned for
more than 52 weeks. Comparable sales is intended only as supplemental information and is not a substitute for net
sales presented in accordance with GAAP.
Total comparable sales increased 3.1% in fiscal 2022, reflecting an 8.8% increase in comparable average ticket,
partially offset by a 5.4% decrease in comparable customer transactions compared to fiscal 2021. The increase in
comparable average ticket was primarily driven by inflation, as well as demand for new and innovative products.
The decrease in comparable customer transactions reflects the impact of macroeconomic factors during fiscal 2022,
including indications of price sensitivity to the broader inflationary environment and a gradual shift in consumer
spending from goods back to services, resulting in transactions trending towards fiscal 2019, pre-COVID-19
pandemic levels.
For fiscal 2022, 10 of our 14 merchandising departments posted positive comparable sales, led by Building
Materials, Plumbing, Millwork, Paint, Hardware, and Kitchen and Bath, which posted comparable sales above the
Company average. Our Indoor Garden, Outdoor Garden, Appliances, and Flooring departments posted negative
comparable sales.
Gross Profit
Gross profit increased $1.9 billion, or 3.8%, to $52.8 billion in fiscal 2022. Gross profit as a percent of net sales, or
gross profit margin, was 33.5% in fiscal 2022 compared to 33.6% in fiscal 2021. The decrease in gross profit margin
was primarily driven by higher product and transportation costs, pressure from shrink during the second half of the
year, and investments in our supply chain network, offset by the benefit from higher retail prices, along with
favorable product mix.
Operating Expenses
Our operating expenses are composed of SG&A and depreciation and amortization.
Selling, General & Administrative. SG&A increased $878 million, or 3.5%, to $26.3 billion in fiscal 2022. As a
percent of net sales, SG&A was 16.7% in fiscal 2022 compared to 16.8% in fiscal 2021, primarily reflecting leverage
from a positive comparable sales environment and lower incentive compensation, partially offset by wage
investments for hourly associates and increased operational costs, including planned investments designed to drive
efficiencies in our stores.
Depreciation and Amortization. Depreciation and amortization increased $69 million, or 2.9%, to $2.5 billion in
fiscal 2022. As a percent of net sales, depreciation and amortization was 1.6% in both fiscal 2022 and fiscal 2021,
reflecting leverage from a positive comparable sales environment, offset by increased depreciation expense from
strategic investments in the business.
Interest and Other, net
Interest and other, net increased $259 million, or 19.9%, to $1.6 billion in fiscal 2022. As a percent of net sales,
interest and other, net, was 1.0% in fiscal 2022 compared to 0.9% in fiscal 2021, primarily reflecting higher interest
expense due to higher debt balances and increased variable rate interest on floating rate debt resulting from interest
rate swaps, partially offset by leverage from a positive comparable sales environment.
Provision for Income Taxes
Our combined effective income tax rate was 23.9% in fiscal 2022 compared to 24.4% in fiscal 2021. The decrease
in our effective income tax rate in fiscal 2022 was driven by certain discrete tax benefits recognized in fiscal 2022.
Table of Contents
Fiscal 2022 Form 10-K
28
Diluted Earnings per Share
Diluted earnings per share were $16.69 in fiscal 2022 compared to $15.53 in fiscal 2021. The increase in diluted
earnings per share for fiscal 2022 was primarily driven by higher net earnings during fiscal 2022, as well as lower
diluted shares due to share repurchases.
NON-GAAP FINANCIAL MEASURES
To provide clarity on our operating performance, we supplement our reporting with certain non-GAAP financial
measures. However, this supplemental information should not be considered in isolation or as a substitute for the
related GAAP measures. Non-GAAP financial measures presented herein may differ from similar measures used by
other companies.
Return on Invested Capital
We believe ROIC is meaningful for investors and management because it measures how effectively we deploy our
capital base. We define ROIC as NOPAT, a non-GAAP financial measure, for the most recent twelve-month period,
divided by average debt and equity. We define average debt and equity as the average of beginning and ending
long-term debt (including current installments) and equity for the most recent twelve-month period.
The following table presents the calculation of ROIC, together with a reconciliation of NOPAT to net earnings (the
most comparable GAAP measure):
Fiscal Fiscal Fiscal
dollars in millions
2022 2021 2020
Net earnings $ 17,105 $ 16,433 $ 12,866
Interest and other, net 1,562 1,303 1,300
Provision for income taxes 5,372 5,304 4,112
Operating income 24,039 23,040 18,278
Income tax adjustment
(1)
(5,745) (5,622) (4,423)
NOPAT $ 18,294 $ 17,418 $ 13,855
Average debt and equity $ 41,055 $ 38,946 $ 33,964
ROIC 44.6 % 44.7 % 40.8 %
—————
(1) Income tax adjustment is defined as operating income multiplied by our effective tax rate for the trailing twelve months.
LIQUIDITY AND CAPITAL RESOURCES
At January 29, 2023, we had $2.8 billion in cash and cash equivalents, of which $825 million was held by our
foreign subsidiaries. We believe that our current cash position, cash flow generated from operations, funds available
from our commercial paper program, and access to the long-term debt capital markets should be sufficient not only
for our operating requirements, any required debt payments, and satisfaction of other contractual obligations, but
also to enable us to invest in the business, fund dividend payments, and fund any share repurchases through the
next several fiscal years. In addition, we believe we have the ability to obtain alternative sources of financing, if
necessary.
Our material cash requirements include contractual and other obligations arising in the normal course of business.
These obligations primarily include long-term debt and related interest payments, operating and finance lease
obligations, and purchase obligations. In addition to our cash requirements, we follow a disciplined approach to
capital allocation. This approach first prioritizes investing in the business, followed by paying dividends, with the
intent of then returning excess cash to shareholders in the form of share repurchases. For fiscal 2023, we plan to
invest approximately $3 billion back into our business in the form of capital expenditures, in line with our expectation
of approximately two percent of net sales on an annual basis. However, we may adjust our capital expenditures to
support the operations of the business, to enhance long-term strategic positioning, or in response to the economic
environment, as necessary or appropriate. Capital expenditures were $3.1 billion in fiscal 2022.
Table of Contents
Fiscal 2022 Form 10-K
29
During fiscal 2022, we paid cash dividends of $7.8 billion to shareholders. In February 2023, we announced a 10%
increase in our quarterly cash dividend from $1.90 to $2.09 per share. We intend to pay a dividend in the future;
however, any future dividend is subject to declaration by the Board of Directors based on our earnings, capital
requirements, financial condition, and other factors considered relevant by our Board of Directors.
In August 2022, our Board of Directors approved a $15.0 billion share repurchase authorization that replaced the
previous authorization of $20.0 billion, which was approved in May 2021. This new authorization does not have a
prescribed expiration date. As of January 29, 2023, approximately $12.5 billion of the $15.0 billion share repurchase
authorization remained available. During fiscal 2022, we had cash payments of $6.7 billion for repurchases of our
common stock through open market purchases.
DEBT
In July 2022, we expanded our commercial paper program from $3.0 billion to $5.0 billion to further enhance our
financial flexibility. All of our short-term borrowings in fiscal 2022 were under our commercial paper program, and
the maximum amount outstanding at any time was $2.7 billion. In connection with our program, we have back-up
credit facilities with a consortium of banks. In July 2022, we also expanded the borrowing capacity under these
back-up facilities from $3.0 billion to $5.0 billion by entering into a five-year $3.5 billion credit facility scheduled to
expire in July 2027 and a 364-day $1.5 billion credit facility scheduled to expire in July 2023. These facilities
replaced our previously existing five-year $2.0 billion credit facility, which was scheduled to expire in December
2023, and our 364-day $1.0 billion credit facility, which was scheduled to expire in December 2022. At January 29,
2023, there were no borrowings outstanding under our commercial paper program, and we were in compliance with
all of the covenants contained in our credit facilities, none of which are expected to impact our liquidity or capital
resources.
We also issue senior notes from time to time as part of our capital management strategy. In March 2022, we issued
$4.0 billion of senior notes. The net proceeds from this issuance were used for general corporate purposes,
including repayment of outstanding indebtedness and repurchases of shares of our common stock. In September
2022, we issued an additional $3.0 billion of senior notes. The net proceeds from this issuance were used for
general corporate purposes, including repurchases of shares of our common stock. During fiscal 2022, we repaid
$2.25 billion of senior notes. At January 29, 2023, we had an aggregate principal amount of senior notes
outstanding of $41.2 billion, with $1.0 billion payable within 12 months. Future interest payments associated with
these senior notes total $24.9 billion, with $1.7 billion payable within 12 months, based on current interest rates,
which include the impact of our active interest rate swap agreements.
The indentures governing our senior notes do not generally limit our ability to incur additional indebtedness or
require us to maintain financial ratios or specified levels of net worth or liquidity. The indentures governing the notes
contain various customary covenants; however, none are expected to impact our liquidity or capital resources. See
Note 4 to our consolidated financial statements for further discussion of our debt arrangements.
LEASES
We use operating and finance leases largely to fund a portion of our real estate, including our stores, distribution
centers, and store support centers. At January 29, 2023, we had aggregate lease obligations of $14.7 billion, with
$1.5 billion payable within 12 months. Aggregate lease obligations include $2.1 billion of obligations related to
leases not yet commenced. See Note 3 to our consolidated financial statements for further discussion of our
operating and finance leases.
PURCHASE OBLIGATIONS AND OTHER
Purchase obligations include all legally binding contracts such as firm commitments for inventory purchases, media
and sponsorship spend, software and license commitments, and legally binding service contracts. We issue
inventory purchase orders in the ordinary course of business, which are typically cancellable by their terms,
therefore we do not consider purchase orders that are cancellable to be firm inventory commitments. At January 29,
2023, we had aggregate purchase obligations of $1.8 billion, with $947 million payable within 12 months.
At January 29, 2023, we had aggregate liabilities for unrecognized tax benefits totaling $643 million, none of which
are expected to be paid in the next 12 months. The timing of payment, if any, associated with our long-term
unrecognized tax benefit liabilities is unknown. See Note 5 to our consolidated financial statements for further
discussion of our unrecognized tax benefits.
We have no material off-balance sheet arrangements.
Table of Contents
Fiscal 2022 Form 10-K
30
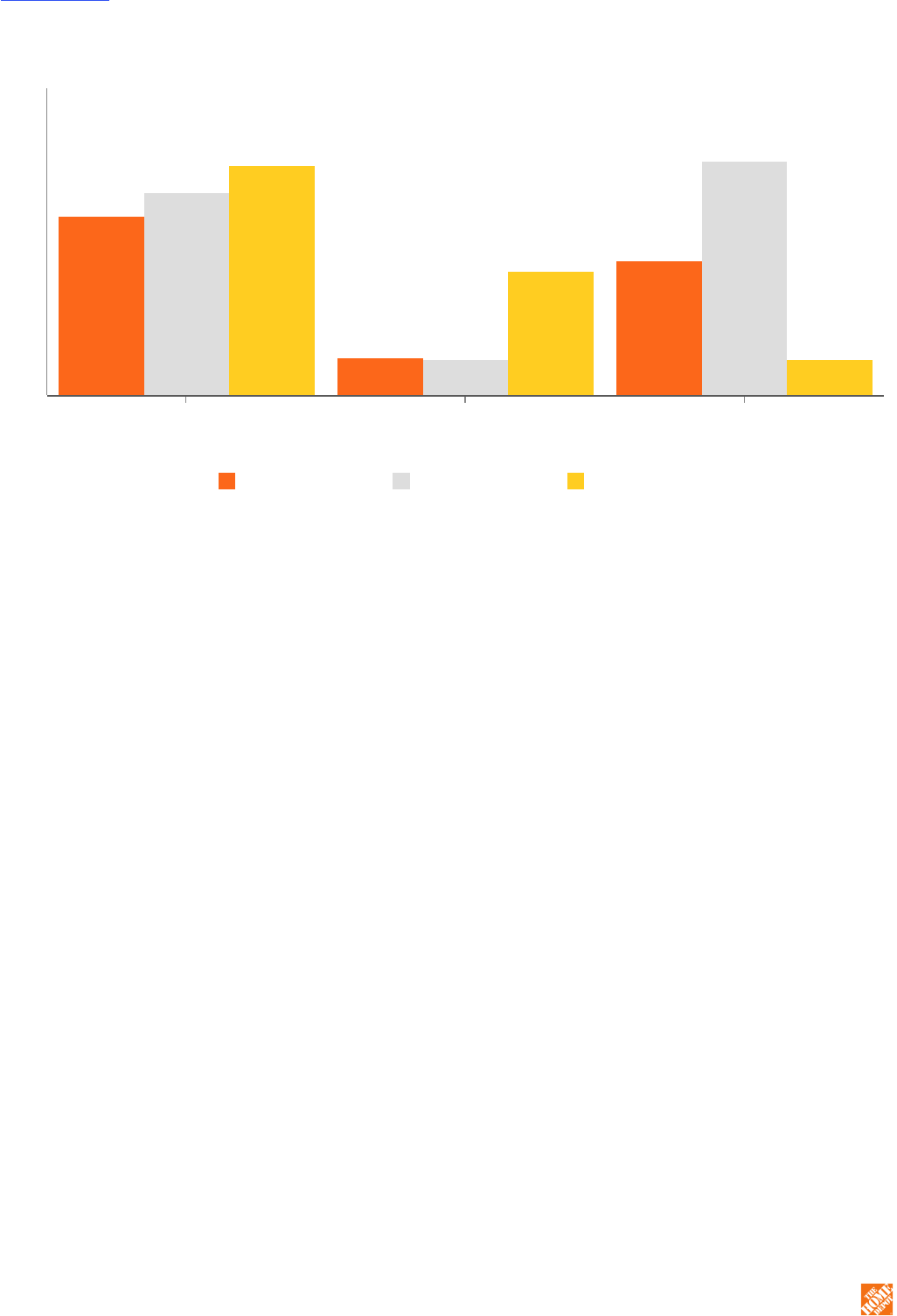
CASH FLOWS SUMMARY
(in billions)
$14.6
$3.1
$11.0
$16.6
$3.0
$19.1
$18.8
$10.2
$3.0
Fiscal 2022 Fiscal 2021 Fiscal 2020
Net cash provided by
operating activities
Net cash used in
investing activities
Net cash used in
financing activities
Operating Activities
Cash flow generated from operations provides us with a significant source of liquidity. Our operating cash flows
result primarily from cash received from our customers, offset by cash payments we make for products and
services, associate compensation, operations, occupancy costs, and income taxes. Cash provided by or used in
operating activities is also subject to changes in working capital. Working capital at any point in time is subject to
many variables, including seasonality, inventory management and category expansion, the timing of cash receipts
and payments, vendor payment terms, and fluctuations in foreign exchange rates.
Net cash provided by operating activities decreased by $2.0 billion in fiscal 2022 compared to fiscal 2021, primarily
driven by changes in working capital, slightly offset by an increase in net earnings. Changes in working capital were
driven by inventory management actions and the related timing of vendor payments. These inventory management
actions, which began in fiscal 2021 and moderated during the second half of fiscal 2022, reflect strategic
investments in inventory to support the demand environment, promote higher in-stock levels, and pull forward
merchandise for seasonal events in response to global supply chain disruption, as well as investments in our new
supply chain facilities.
Investing Activities
Cash used in investing activities increased by $171 million in fiscal 2022 compared to fiscal 2021, primarily resulting
from increased capital expenditures, partially offset by cash paid for an acquired business during fiscal 2021.
Financing Activities
Cash used in financing activities in fiscal 2022 primarily reflected $7.8 billion of cash dividends paid, $6.7 billion of
share repurchases, $2.5 billion of repayments of long-term debt, and $1.0 billion of net repayments of short-term
debt, partially offset by $6.9 billion of net proceeds from long-term debt.
Cash used in financing activities in fiscal 2021 primarily reflected $14.8 billion of share repurchases, $7.0 billion of
cash dividends paid, and $1.5 billion of repayments of long-term debt, partially offset by $3.0 billion of net proceeds
from long-term debt and $1.0 billion of net proceeds from short-term debt. Fiscal 2021 reflected elevated share
repurchase activity following the temporary suspension of repurchases during fiscal 2020 in order to enhance our
liquidity position at the onset of the COVID-19 pandemic.
Table of Contents
Fiscal 2022 Form 10-K
31

CRITICAL ACCOUNTING ESTIMATES
The preparation of our consolidated financial statements in accordance with GAAP requires that we make estimates
and assumptions that affect the reported amounts of assets and liabilities, the disclosure of contingent assets and
liabilities, and the reported amounts of revenues and expenses. Actual results could differ from those estimates.
Our significant accounting policies are disclosed in Note 1 to our consolidated financial statements. The following
discussion addresses our most critical accounting estimates, which are those that are both important to the
representation of our financial condition and results of operations, and that require significant judgment or use of
significant assumptions or complex estimates.
MERCHANDISE INVENTORIES
We value the majority of our inventory under the retail inventory method, using the first-in, first-out method, with the
remainder of our inventories valued under a cost method. Under the retail inventory method, inventories are stated
at cost, which is determined by applying a cost-to-retail ratio to the retail value of inventories.
The retail value of our inventory is adjusted as needed to reflect current market conditions. Because these
adjustments are based on current prevailing market conditions, the value of our inventory approximates the lower of
cost or market. The valuation under the retail inventory method is based on a number of factors such as markups,
markdowns, and inventory losses (or shrink). As such, there exists an inherent uncertainty in the final determination
of inventory cost and gross profit. We determine markups and markdowns based on the consideration of a variety of
factors such as current and anticipated demand, customer preferences and buying trends, age of the merchandise,
and weather conditions.
We calculate shrink based on actual inventory losses identified as a result of physical inventory counts during each
fiscal period and estimated inventory losses between physical inventory counts. The estimate for shrink occurring in
the interim period between physical inventory counts is calculated on a store-specific basis and is primarily based
on recent shrink results. A 10% increase in the shrink rate used to estimate our inventory shrink reserve would have
increased cost of sales by approximately $113 million for fiscal 2022. Historically, the difference between estimated
shrink and actual inventory losses has not been material to our annual financial results.
We do not believe there is a reasonable likelihood for a material change in the estimates or assumptions we use to
value our inventory under the retail inventory method. We believe that the retail inventory method provides an
inventory valuation which approximates cost and results in valuing our inventory at the lower of cost or market.
ADDITIONAL INFORMATION
For information on our accounting policies and on accounting pronouncements that have impacted or are expected
to materially impact our financial condition, results of operations, or cash flows, see Note 1 to our consolidated
financial statements.
Item 7A. Quantitative and Qualitative Disclosures About Market Risk.
INTEREST RATE RISK
We have exposure to interest rate risk in connection with our long-term debt portfolio. We use interest rate swap
agreements to manage our fixed/floating-rate debt portfolio, none of which are for trading or speculative purposes.
At January 29, 2023, after giving consideration to our interest rate swap agreements, floating-rate debt principal was
$5.4 billion, or approximately 13% of our senior notes portfolio. Our interest rate swap agreements were in an
aggregate liability position of $778 million at January 29, 2023. The changes in the fair values of our interest rate
swap agreements offset the changes in the fair value of the hedged long-term debt. Based on our January 29, 2023
floating-rate debt principal, a one percentage point increase in the interest rate of floating-rate debt would increase
our annual interest expense by approximately $54 million.
The United Kingdom’s Financial Conduct Authority announced the phased cessation of publication of LIBOR
beginning after 2021 and continuing through 2023. While the discontinuance of LIBOR tenors that are scheduled to
occur in 2023 will impact our interest rate swaps, we do not anticipate the transition to a new reference rate will
have a material impact on our consolidated financial condition, results of operations, or cash flows.
Table of Contents
Fiscal 2022 Form 10-K
32
FOREIGN CURRENCY EXCHANGE RATE RISK
We are exposed to risks from foreign currency exchange rate fluctuations on the translation of our foreign
operations into U.S. dollars and on the purchase of goods by these foreign operations that are not denominated in
their local currencies. We use derivative instruments to hedge a portion of our foreign currency exchange rate risk,
none of which are for trading or speculative purposes. Our foreign currency related hedging arrangements
outstanding at the end of fiscal 2022 were not material.
COMMODITY PRICE RISK
We experience inflation and deflation related to our purchase of certain commodity products. This price volatility
could potentially have a material impact on our financial condition and/or our results of operations. In order to
mitigate price volatility, we monitor commodity price fluctuations and may adjust our selling prices accordingly;
however, our ability to recover higher costs through increased pricing may be limited by the competitive environment
in which we operate. We currently do not use derivative instruments to manage these risks.
Item 8. Financial Statements and Supplementary Data.
TABLE OF CONTENTS
Report of Independent Registered Public Accounting Firm 34
Consolidated Balance Sheets 36
Consolidated Statements of Earnings 37
Consolidated Statements of Comprehensive Income 38
Consolidated Statements of Stockholders' Equity 39
Consolidated Statements of Cash Flows 40
Notes to Consolidated Financial Statements 41
Note 1. Summary of Significant Accounting Policies 41
Note 2. Segment Reporting and Net Sales 48
Note 3. Property and Leases 49
Note 4. Debt and Derivative Instruments 51
Note 5. Income Taxes 55
Note 6. Stockholders' Equity 57
Note 7. Fair Value Measurements 58
Note 8. Stock-Based Compensation 59
Note 9. Employee Benefit Plans 61
Note 10. Weighted Average Common Shares 62
Note 11. Commitments and Contingencies 62
Note 12. HD Supply Acquisition 62
Table of Contents
Fiscal 2022 Form 10-K
33

REPORT OF INDEPENDENT REGISTERED PUBLIC ACCOUNTING FIRM
To the Stockholders and the Board of Directors
The Home Depot, Inc.:
Opinion on the Consolidated Financial Statements
We have audited the accompanying consolidated balance sheets of The Home Depot, Inc. and subsidiaries (the
Company) as of January 29, 2023 and January 30, 2022, the related consolidated statements of earnings,
comprehensive income, stockholders’ equity, and cash flows for each of the fiscal years in the three-year period
ended January 29, 2023, and the related notes (collectively, the consolidated financial statements). In our opinion,
the consolidated financial statements present fairly, in all material respects, the financial position of the Company as
of January 29, 2023 and January 30, 2022, and the results of its operations and its cash flows for each of the fiscal
years in the three-year period ended January 29, 2023, in conformity with U.S. generally accepted accounting
principles.
We also have audited, in accordance with the standards of the Public Company Accounting Oversight Board (United
States) (PCAOB), the Company’s internal control over financial reporting as of January 29, 2023, based on criteria
established in Internal Control – Integrated Framework (2013) issued by the Committee of Sponsoring
Organizations of the Treadway Commission, and our report dated March 15, 2023 expressed an unqualified opinion
on the effectiveness of the Company’s internal control over financial reporting.
Basis for Opinion
These consolidated financial statements are the responsibility of the Company’s management. Our responsibility is
to express an opinion on these consolidated financial statements based on our audits. We are a public accounting
firm registered with the PCAOB and are required to be independent with respect to the Company in accordance with
the U.S. federal securities laws and the applicable rules and regulations of the Securities and Exchange
Commission and the PCAOB.
We conducted our audits in accordance with the standards of the PCAOB. Those standards require that we plan
and perform the audit to obtain reasonable assurance about whether the consolidated financial statements are free
of material misstatement, whether due to error or fraud. Our audits included performing procedures to assess the
risks of material misstatement of the consolidated financial statements, whether due to error or fraud, and
performing procedures that respond to those risks. Such procedures included examining, on a test basis, evidence
regarding the amounts and disclosures in the consolidated financial statements. Our audits also included evaluating
the accounting principles used and significant estimates made by management, as well as evaluating the overall
presentation of the consolidated financial statements. We believe that our audits provide a reasonable basis for our
opinion.
Critical Audit Matter
The critical audit matter communicated below is a matter arising from the current period audit of the consolidated
financial statements that was communicated or required to be communicated to the audit committee and that: (1)
relates to accounts or disclosures that are material to the consolidated financial statements and (2) involved our
especially challenging, subjective, or complex judgments. The communication of a critical audit matter does not alter
in any way our opinion on the consolidated financial statements, taken as a whole, and we are not, by
communicating the critical audit matter below, providing a separate opinion on the critical audit matter or on the
accounts or disclosures to which it relates.
Estimation of store shrink
As discussed in Note 1 to the consolidated financial statements, the majority of the Company’s U.S. merchandise
inventories are stated at the lower of cost (first-in, first out) or market as determined by the retail inventory
method, which is based on a number of factors such as markups, markdowns, and inventory losses (or shrink).
Shrink is the difference between the recorded amount of inventory and the physical inventory count. The
Company calculates shrink based on actual inventory losses identified as a result of physical inventory counts
during each fiscal period and estimated inventory losses between physical inventory counts. The estimate for
shrink occurring in the interim period between physical inventory counts is calculated on a store-specific basis
and is primarily based on recent shrink results.
We identified the evaluation of the estimation of store shrink occurring in the period between physical inventory
counts and fiscal year-end as a critical audit matter. Evaluating the Company’s estimation of shrink at the end of
the fiscal year using interim inventory loss experience in U.S. retail stores involved auditor judgment.
Table of Contents
Fiscal 2022 Form 10-K
34

The following are the primary procedures we performed to address this critical audit matter. We evaluated the
design and tested the operating effectiveness of certain internal controls related to the process of developing the
estimate of store shrink. We evaluated the appropriateness of the Company using interim physical inventory
counts to estimate inventory losses in U.S. retail stores at the end of the fiscal year by:
• Evaluating the method and certain assumptions used;
• Testing the application of the method and certain assumptions used;
• Performing a current year trend analysis; and
• Performing a sensitivity analysis over the shrink reserve estimate.
/s/ KPMG LLP
We have served as the Company’s auditor since 1979.
Atlanta, Georgia
March 15, 2023
Table of Contents
Fiscal 2022 Form 10-K
35
THE HOME DEPOT, INC.
CONSOLIDATED BALANCE SHEETS
in millions, except per share data
January 29,
2023
January 30,
2022
Assets
Current assets:
Cash and cash equivalents $ 2,757 $ 2,343
Receivables, net 3,317 3,426
Merchandise inventories 24,886 22,068
Other current assets 1,511 1,218
Total current assets 32,471 29,055
Net property and equipment 25,631 25,199
Operating lease right-of-use assets 6,941 5,968
Goodwill 7,444 7,449
Other assets 3,958 4,205
Total assets $ 76,445 $ 71,876
Liabilities and Stockholders’ Equity
Current liabilities:
Short-term debt $ — $ 1,035
Accounts payable 11,443 13,462
Accrued salaries and related expenses 1,991 2,426
Sales taxes payable 528 848
Deferred revenue 3,064 3,596
Income taxes payable 50 158
Current installments of long-term debt 1,231 2,447
Current operating lease liabilities 945 830
Other accrued expenses 3,858 3,891
Total current liabilities 23,110 28,693
Long-term debt, excluding current installments 41,962 36,604
Long-term operating lease liabilities 6,226 5,353
Deferred income taxes 1,019 909
Other long-term liabilities 2,566 2,013
Total liabilities 74,883 73,572
Commitments and contingencies (Note 11)
Common stock, par value $0.05; authorized: 10,000 shares; issued: 1,794 shares
at January 29, 2023 and 1,792 shares at January 30, 2022; outstanding: 1,016
shares at January 29, 2023 and 1,035 shares at January 30, 2022 90 90
Paid-in capital 12,592 12,132
Retained earnings 76,896 67,580
Accumulated other comprehensive loss (718) (704)
Treasury stock, at cost, 778 shares at January 29, 2023 and 757 shares at
January 30, 2022 (87,298) (80,794)
Total stockholders’ equity (deficit) 1,562 (1,696)
Total liabilities and stockholders’ equity $ 76,445 $ 71,876
—————
See accompanying notes to consolidated financial statements.
Table of Contents
Fiscal 2022 Form 10-K
36
THE HOME DEPOT, INC.
CONSOLIDATED STATEMENTS OF EARNINGS
in millions, except per share data
Fiscal Fiscal Fiscal
2022 2021 2020
Net sales $ 157,403 $ 151,157 $ 132,110
Cost of sales 104,625 100,325 87,257
Gross profit 52,778 50,832 44,853
Operating expenses:
Selling, general and administrative 26,284 25,406 24,447
Depreciation and amortization 2,455 2,386 2,128
Total operating expenses 28,739 27,792 26,575
Operating income 24,039 23,040 18,278
Interest and other (income) expense:
Interest income and other, net (55) (44) (47)
Interest expense 1,617 1,347 1,347
Interest and other, net 1,562 1,303 1,300
Earnings before provision for income taxes 22,477 21,737 16,978
Provision for income taxes 5,372 5,304 4,112
Net earnings $ 17,105 $ 16,433 $ 12,866
Basic weighted average common shares 1,022 1,054 1,074
Basic earnings per share $ 16.74 $ 15.59 $ 11.98
Diluted weighted average common shares 1,025 1,058 1,078
Diluted earnings per share $ 16.69 $ 15.53 $ 11.94
—————
See accompanying notes to consolidated financial statements.
Table of Contents
Fiscal 2022 Form 10-K
37
THE HOME DEPOT, INC.
CONSOLIDATED STATEMENTS OF COMPREHENSIVE INCOME
Fiscal Fiscal Fiscal
in millions
2022 2021 2020
Net earnings $ 17,105 $ 16,433 $ 12,866
Other comprehensive (loss) income, net of tax:
Foreign currency translation adjustments (22) (77) 60
Cash flow hedges 9 9 8
Other (1) 35 —
Total other comprehensive (loss) income, net of tax (14) (33) 68
Comprehensive income $ 17,091 $ 16,400 $ 12,934
—————
See accompanying notes to consolidated financial statements.
Table of Contents
Fiscal 2022 Form 10-K
38
THE HOME DEPOT, INC.
CONSOLIDATED STATEMENTS OF STOCKHOLDERS’ EQUITY
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Common Stock:
Balance at beginning of year $ 90 $ 89 $ 89
Shares issued under employee stock plans, net — 1 —
Balance at end of year 90 90 89
Paid-in Capital:
Balance at beginning of year 12,132 11,540 11,001
Shares issued under employee stock plans, net 94 194 229
Stock-based compensation expense 366 398 310
Balance at end of year 12,592 12,132 11,540
Retained Earnings:
Balance at beginning of year 67,580 58,134 51,729
Net earnings 17,105 16,433 12,866
Cash dividends (7,789) (6,985) (6,451)
Other — (2) (10)
Balance at end of year 76,896 67,580 58,134
Accumulated Other Comprehensive Loss:
Balance at beginning of year (704) (671) (739)
Foreign currency translation adjustments, net of tax (22) (77) 60
Cash flow hedges, net of tax 9 9 8
Other, net of tax (1) 35 —
Balance at end of year (718) (704) (671)
Treasury Stock:
Balance at beginning of year (80,794) (65,793) (65,196)
Repurchases of common stock (6,504) (15,001) (597)
Balance at end of year (87,298) (80,794) (65,793)
Total stockholders’ equity (deficit) $ 1,562 $ (1,696) $ 3,299
—————
See accompanying notes to consolidated financial statements.
Table of Contents
Fiscal 2022 Form 10-K
39
THE HOME DEPOT, INC.
CONSOLIDATED STATEMENTS OF CASH FLOWS
Fiscal Fiscal Fiscal
in millions
2022 2021 2020
Cash Flows from Operating Activities:
Net earnings $ 17,105 $ 16,433 $ 12,866
Reconciliation of net earnings to net cash provided by operating
activities:
Depreciation and amortization 2,975 2,862 2,519
Stock-based compensation expense 366 399 310
Changes in receivables, net 111 (435) (465)
Changes in merchandise inventories (2,830) (5,403) (1,657)
Changes in other current assets (311) (330) 43
Changes in accounts payable and accrued expenses (2,577) 2,401 5,118
Changes in deferred revenue (526) 775 702
Changes in income taxes payable (107) (51) (149)
Changes in deferred income taxes 138 (276) (569)
Other operating activities 271 196 121
Net cash provided by operating activities 14,615 16,571 18,839
Cash Flows from Investing Activities:
Capital expenditures (3,119) (2,566) (2,463)
Payments for businesses acquired, net — (421) (7,780)
Other investing activities (21) 18 73
Net cash used in investing activities (3,140) (2,969) (10,170)
Cash Flows from Financing Activities:
(Repayments of) proceeds from short-term debt, net (1,035) 1,035 (974)
Proceeds from long-term debt, net of discounts 6,942 2,979 7,933
Repayments of long-term debt (2,491) (1,532) (2,872)
Repurchases of common stock (6,696) (14,809) (791)
Proceeds from sales of common stock 264 337 326
Cash dividends (7,789) (6,985) (6,451)
Other financing activities (188) (145) (154)
Net cash used in financing activities (10,993) (19,120) (2,983)
Change in cash and cash equivalents 482 (5,518) 5,686
Effect of exchange rate changes on cash and cash equivalents (68) (34) 76
Cash and cash equivalents at beginning of year 2,343 7,895 2,133
Cash and cash equivalents at end of year $ 2,757 $ 2,343 $ 7,895
Supplemental Disclosures:
Cash paid for income taxes $ 5,435 $ 5,504 $ 4,654
Cash paid for interest, net of interest capitalized 1,449 1,269 1,241
Non-cash capital expenditures 351 421 274
—————
See accompanying notes to consolidated financial statements.
Table of Contents
Fiscal 2022 Form 10-K
40
THE HOME DEPOT, INC.
NOTES TO CONSOLIDATED FINANCIAL STATEMENTS
1. SUMMARY OF SIGNIFICANT ACCOUNTING POLICIES
Business
The Home Depot, Inc., together with its subsidiaries (the “Company,” “Home Depot,” “we,” “our” or “us”), is a home
improvement retailer that sells a wide assortment of building materials, home improvement products, lawn and
garden products, décor items, and facilities maintenance, repair and operations products, in stores and online. We
also provide a number of services, including home improvement installation services and tool and equipment rental.
We operate in the U.S. (including the Commonwealth of Puerto Rico and the territories of the U.S. Virgin Islands
and Guam), Canada, and Mexico.
Consolidation and Presentation
Our consolidated financial statements include our accounts and those of our wholly-owned subsidiaries.
Intercompany balances and transactions are eliminated in consolidation. Our fiscal year is a 52- or 53-week period
ending on the Sunday nearest to January 31
st
. All periods presented include 52 weeks.
Use of Estimates
We have made a number of estimates and assumptions relating to the reporting of assets and liabilities, the
disclosure of contingent assets and liabilities, and reported amounts of revenues and expenses in preparing these
financial statements in conformity with GAAP. While we believe these estimates and assumptions are reasonable,
actual results could differ from these estimates.
Cash and Cash Equivalents
Cash and cash equivalents consist of cash on hand and highly liquid investments purchased with original maturities
of three months or less.
Receivables, net
The following table presents components of receivables, net:
in millions
January 29,
2023
January 30,
2022
Card receivables $ 1,003 $ 1,028
Rebate receivables 948 1,170
Customer receivables 871 703
Other receivables 495 525
Receivables, net $ 3,317 $ 3,426
Card receivables consist of payments due from financial institutions for the settlement of credit card and debit card
transactions. Rebate receivables represent amounts due from vendors for volume and co-op advertising rebates.
Customer receivables relate to credit extended directly to certain customers in the ordinary course of business. The
valuation allowance related to these receivables was not material to our consolidated financial statements at the
end of fiscal 2022 or fiscal 2021.
Merchandise Inventories
Inventory cost includes the amount we pay to acquire inventory, including freight and import costs, as well as
operating costs and depreciation associated with our sourcing and distribution network, and is net of certain vendor
allowances. The majority of our merchandise inventories are stated at the lower of cost (first-in, first-out) or market,
as determined by the retail inventory method, which is based on a number of factors such as markups, markdowns,
and inventory losses (or shrink). As the inventory retail value is adjusted regularly to reflect market conditions,
inventory valued using the retail method approximates the lower of cost or market. Certain subsidiaries, including
retail operations in Canada and Mexico, and distribution centers, record merchandise inventories at the lower of
cost or net realizable value, as determined by a cost method. These merchandise inventories represent
approximately 42% of the total merchandise inventories balance. We evaluate the inventory valued using a cost
method at the end of each quarter to ensure that it is carried at the lower of cost or net realizable value, and the
adjustments recorded to merchandise inventories valued under a cost method were not material to our consolidated
financial statements at the end of fiscal 2022 or fiscal 2021.
Table of Contents
Fiscal 2022 Form 10-K
41
Physical inventory counts or cycle counts are taken on a regular basis in each store and distribution center to
ensure that amounts reflected in merchandise inventories are properly stated. Shrink (or in the case of excess
inventory, swell) is the difference between the recorded amount of inventory and the physical inventory count. We
calculate shrink based on actual inventory losses identified as a result of physical inventory counts during each
fiscal period and estimated inventory losses between physical inventory counts. The estimate for shrink occurring in
the interim period between physical inventory counts is calculated on a store-specific basis and is primarily based
on recent shrink results. Historically, the difference between estimated shrink and actual inventory losses has not
been material to our annual financial results.
Property and Equipment
Buildings and related improvements, furniture, fixtures, and equipment are recorded at cost and depreciated using
the straight-line method over their estimated useful lives. Leasehold improvements and assets held under finance
leases are amortized using the straight-line method over the original term of the lease or the useful life of the asset,
whichever is shorter.
The following table presents the estimated useful lives of our property and equipment:
Life
Buildings and improvements 5 – 45 years
Furniture, fixtures and equipment 2 – 20 years
Leasehold improvements 5 – 45 years
We capitalize certain costs, including interest, related to construction in progress and the acquisition and
development of software. Costs associated with the acquisition and development of software are amortized using
the straight-line method over the estimated useful life of the software, which ranges from three to seven years.
Certain development costs not meeting the criteria for capitalization are expensed as incurred.
We evaluate our long-lived assets each quarter for indicators of potential impairment. Indicators of impairment
include current period losses combined with a history of losses, our decision to relocate or close a store or other
location before the end of its previously estimated useful life, or when changes in other circumstances indicate the
carrying amount of an asset may not be recoverable. The evaluation for long-lived assets is performed at the lowest
level of identifiable cash flows, which is generally the individual store level. The assets of a store with indicators of
impairment are evaluated for recoverability by comparing their undiscounted future cash flows with their carrying
value. If the carrying value is greater than the undiscounted future cash flows, we then measure the asset group’s
fair value to determine whether an impairment loss should be recognized. If the resulting fair value is less than the
carrying value, an impairment loss is recognized for the difference between the carrying value and the estimated fair
value. Impairment losses on property and equipment are recorded as a component of SG&A. Impairment charges
for long-lived assets were not material to our consolidated financial statements in fiscal 2022, fiscal 2021, or fiscal
2020.
Leases
We enter into contractual arrangements for the utilization of certain non-owned assets which are evaluated as
finance or operating leases upon commencement, and are accounted for accordingly. Specifically, a contract is or
contains a lease when (1) the contract contains an explicitly or implicitly identified asset and (2) we obtain
substantially all of the economic benefits from the use of that underlying asset and direct how and for what purpose
the asset is used during the term of the contract in exchange for consideration. We assess whether an arrangement
is or contains a lease at inception of the contract.
Our leases include certain retail locations, warehouse and distribution space, office space, equipment, and vehicles.
A substantial majority of our leases have remaining lease terms of one to 20 years. Our real estate leases typically
provide the option to extend the lease for five-year terms, and some of our leases may include the option to
terminate in less than five years. The lease term used to calculate the right-of-use asset and lease liability at
commencement includes the impacts of options to extend or terminate the lease when it is reasonably certain that
we will exercise that option. When determining whether it is reasonably certain that we will exercise an option at
commencement, we consider various existing economic factors, including market conditions, real estate strategies,
the nature, length, and terms of the agreement, as well as the uncertainty of the condition of leased equipment at
the end of the lease term. Based on these determinations, we generally conclude that the exercise of renewal
options would not be reasonably certain in determining the lease term at commencement.
Table of Contents
Fiscal 2022 Form 10-K
42

The discount rate used to calculate the present value of lease payments is the rate implicit in the lease, when
readily determinable. As the rate implicit in the lease is rarely readily determinable, we use a secured incremental
borrowing rate, which is updated on a quarterly basis, as the discount rate for the present value of lease payments.
Real estate taxes, insurance, maintenance, and operating expenses applicable to the leased asset are generally
our obligations under our lease agreements. In instances where these payments are fixed, they are included in the
measurement of our lease liabilities, and when variable, are excluded and recognized in the period in which the
obligation for those payments is incurred. Certain of our lease agreements also include rental payments based on
an index or rate and others include rental payments based on a percentage of sales. For variable payments
dependent upon an index or rate, we apply the active index or rate as of the lease commencement date. Variable
lease payments not based on an index or rate are not included in the measurement of our lease liabilities as they
cannot be reasonably estimated, and are recognized in the period in which the obligation for those payments is
incurred.
Leases that have a term of twelve months or less upon commencement are considered short-term in nature. Short-
term leases are not included on the consolidated balance sheets and are expensed on a straight-line basis over the
lease term. We have also elected to not separate lease and non-lease components for certain classes of assets
including real estate and certain equipment.
Our lease agreements do not contain any material residual value guarantees or material restrictive covenants.
Business Combinations
The assets and liabilities of acquired businesses are recorded at their fair values at the date of acquisition. The
excess of the purchase price over the fair values of the identifiable assets acquired and liabilities assumed is
recorded as goodwill. During the measurement period, which is up to one year from the acquisition date, we may
record adjustments to the assets acquired and liabilities assumed with the corresponding offset to goodwill. Upon
conclusion of the measurement period, any subsequent adjustments are recorded to earnings.
Goodwill
Goodwill represents the excess of purchase price over the fair value of net assets acquired. We do not amortize
goodwill, but assess the recoverability of goodwill in the third quarter of each fiscal year, or more often if indicators
warrant, by determining whether the fair value of each reporting unit supports its carrying value. Each fiscal year, we
may assess qualitative factors to determine whether it is more likely than not that the fair value of each reporting
unit is less than its carrying amount as a basis for determining whether it is necessary to complete quantitative
impairment assessments, with a quantitative assessment completed as facts and circumstances warrant. We
completed our last quantitative assessment in fiscal 2019 and concluded that the fair value of our reporting units
substantially exceeded their respective carrying values, including goodwill.
During the third quarter of fiscal 2022, we completed our annual assessment of the recoverability of goodwill for our
U.S., Canada, and Mexico reporting units based on qualitative factors. We performed a qualitative assessment to
determine if there were any indicators of impairment and concluded that while there have been events and
circumstances in the macro-environment that have impacted us, we have not experienced any entity-specific
indicators that would indicate that it is more likely than not that the fair value of any of our reporting units were less
than their carrying amounts. There were no impairment charges related to goodwill for fiscal 2022, fiscal 2021, or
fiscal 2020.
The following table presents the changes in the carrying amount of our goodwill:
in millions
Fiscal Fiscal
2022 2021
Goodwill, balance at beginning of year $ 7,449 $ 7,126
Acquisitions
(1)
— 323
Other
(2)
(5) —
Goodwill, balance at end of year $ 7,444 $ 7,449
—————
(1) Represents goodwill from a small acquisition completed during the second quarter of Fiscal 2021.
(2) Reflects the net impact of foreign currency translation.
Table of Contents
Fiscal 2022 Form 10-K
43
Other Intangible Assets
Intangible assets other than goodwill are included in other assets on the consolidated balance sheets. We amortize
the cost of definite-lived intangible assets on a straight-line basis over their estimated useful lives, which range up to
20 years, as this approximates the pattern of expected economic benefit. Intangible assets with indefinite lives are
tested in the third quarter of each fiscal year for impairment, or more often if indicators warrant. During the third
quarter of fiscal 2022, we completed our annual assessment of the recoverability of our indefinite-lived intangible
assets based on quantitative factors and concluded no impairment losses should be recognized. There were no
impairment losses related to intangible assets for fiscal 2022, fiscal 2021, and fiscal 2020.
The following table presents information regarding our intangible assets:
January 29, 2023 January 30, 2022
in millions
Gross
Carrying
Amount
Accumulated
Amortization
Net Carrying
Amount
Gross
Carrying
Amount
Accumulated
Amortization
Net Carrying
Amount
Definite-Lived Intangible Assets:
Customer relationships
$ 3,034 $ (495) $ 2,539 $ 3,034 $ (326) $ 2,708
Trade names 151 (16) 135 151 (8) 143
Other 12 (12) — 12 (9) 3
Indefinite-Lived Intangible Assets:
Trade names 649 649 649 649
Total Intangible Assets $ 3,846 $ (523) $ 3,323 $ 3,846 $ (343) $ 3,503
Our intangible asset amortization expense was immaterial for fiscal 2022, fiscal 2021, and fiscal 2020.
The following table presents the estimated future amortization expense related to definite-lived intangible assets as
of January 29, 2023:
in millions
Amortization
Expense
Fiscal 2023 $ 178
Fiscal 2024 178
Fiscal 2025 178
Fiscal 2026 178
Fiscal 2027 167
Thereafter 1,795
Total $ 2,674
Debt
We record any premiums or discounts associated with an issuance of long-term debt as a direct addition or
deduction to the carrying value of the related senior notes. We also record debt issuance costs associated with an
issuance of long-term debt as a direct deduction to the carrying value of the related senior notes. Premium,
discount, and debt issuance costs are amortized over the term of the respective notes using the effective interest
rate method.
Derivative Instruments and Hedging Activities
We use derivative instruments in the management of our interest rate exposure on long-term debt and our exposure
to foreign currency fluctuations. We enter into derivative instruments for risk management purposes only; we do not
enter into derivative instruments for trading or speculative purposes. All derivative instruments are recognized at
their fair values in either assets or liabilities at the balance sheet date and are classified as either current or non-
current based on each contract’s respective maturity. While we enter into master netting arrangements, our policy is
to present the fair value of derivative instruments on a gross basis in our consolidated balance sheets.
Changes in the fair values for derivative instruments designated as cash flow or net investment hedges are
recognized in accumulated other comprehensive income (loss) until the hedged item is recognized in earnings,
which for net investment hedges is upon sale or substantial liquidation of the underlying net investment. Changes in
fair value of outstanding fair value hedges and the offsetting changes in fair values of the hedged item are
Table of Contents
Fiscal 2022 Form 10-K
44

recognized in earnings. We record realized gains and losses from derivative instruments in the same financial
statement line item as the hedged item.
Derivative instruments that are not designated as hedges, if any, are recorded at fair value with unrealized gains or
losses reported in earnings each period in the same financial statement line item as the hedged item. Cash flows
from the settlement of derivative instruments appear in the consolidated statements of cash flows in the same
categories as the cash flows of the hedged item.
Self-Insurance Reserves
We are self-insured for certain losses related to general liability (including product liability), workers’ compensation,
employee group medical, and automobile claims. We recognize the expected ultimate cost for claims incurred
(undiscounted) at the balance sheet date as a liability. The expected ultimate cost for claims incurred is estimated
based upon analysis of historical data and actuarial estimates. Our self-insurance liabilities, which are included in
accrued salaries and related expenses, other accrued expenses and other long-term liabilities in the consolidated
balance sheets, were $1.3 billion at both January 29, 2023 and January 30, 2022.
We also maintain network security and privacy liability insurance coverage to limit our exposure to losses such as
those that may be caused by a significant compromise or breach of our data security.
Treasury Stock
Treasury stock is reflected as a reduction of stockholders’ equity at cost. We use the weighted average purchase
cost to determine the cost of treasury stock that is reissued, if any.
Net Sales
We recognize revenue, net of expected returns and sales tax, at the time the customer takes possession of
merchandise or when a service is performed. Our liability for sales returns is estimated based on historical return
levels and our expectation of future returns. We also recognize a return asset, and corresponding adjustment to
cost of sales, for our right to recover the goods returned by the customer, measured at the former carrying amount
of the goods, less any expected recovery cost. At each financial reporting date, we assess our estimates of
expected returns, refund liabilities, and return assets. Adjustments related to changes in return estimates were
immaterial in fiscal 2022, fiscal 2021, and fiscal 2020.
Services revenue is generated through a variety of installation, home maintenance, and professional service
programs. In these programs, the customer selects and purchases material for a project, and we provide or arrange
for professional installation. These programs are offered through our stores, online, and in-home sales programs.
Under certain programs, when we provide or arrange for the installation of a project and the subcontractor provides
material as part of the installation, both the material and labor are included in services revenue. We recognize
services revenue when the service for the customer is complete, which is not materially different from recognizing
the revenue over the service period as the substantial majority of our services are completed within one week.
For products and services sold in stores or online, payment is typically due at the point of sale. When we receive
payment from customers before the customer has taken possession of the merchandise or the service has been
performed, the amount received is recorded as deferred revenue until the sale or service is complete. Such
performance obligations are part of contracts with expected original durations of typically three months or less. As of
January 29, 2023 and January 30, 2022, deferred revenue for products and services was $2.0 billion and $2.6
billion, respectively.
We further record deferred revenue for the sale of gift cards and recognize the associated revenue upon the
redemption of those gift cards, which generally occurs within six months of gift card issuance. As of January 29,
2023 and January 30, 2022, our performance obligations for unredeemed gift cards were $1.1 billion and $1.0
billion, respectively. Gift card breakage income, which is our estimate of the portion of our gift card balance not
expected to be redeemed, is recognized in net sales and was immaterial in fiscal 2022, fiscal 2021, and fiscal 2020.
We also have agreements with third-party service providers who directly extend credit to customers, manage our
PLCC program, and own the related receivables. We have evaluated the third-party entities holding the receivables
under the program and concluded that they should not be consolidated. The agreement with the primary third-party
service provider for our PLCC program expires in 2028, with us having the option, but no obligation, to purchase the
existing receivables at the end of the agreement. Deferred interest charges incurred for our deferred financing
programs offered to these customers, interchange fees charged to us for their use of the cards, and any profit
sharing with the third-party service providers are included in net sales.
Table of Contents
Fiscal 2022 Form 10-K
45
Cost of Sales
Cost of sales includes the actual cost of merchandise sold and services performed; the cost of transportation of
merchandise from vendors to our distribution network, stores, or customers; shipping and handling costs from our
stores or distribution network to customers; and the operating cost and depreciation of our sourcing and distribution
network. Vendor allowances that are not reimbursements of specific, incremental, and identifiable costs are also
included within cost of sales.
Vendor Allowances
Vendor allowances primarily consist of volume rebates that are earned as a result of attaining certain purchase
levels and co-op advertising allowances for the promotion of vendors’ products that are typically based on
guaranteed minimum amounts with additional amounts being earned for attaining certain purchase levels. These
vendor allowances are accrued as earned, with those allowances received as a result of attaining certain purchase
levels accrued over the incentive period based on estimates of purchases. Volume rebates and certain co-op
advertising allowances reduce the carrying cost of inventory and are recognized in cost of sales when the related
inventory is sold.
Selling, General and Administrative
Selling, general and administrative expenses include compensation and benefits for retail and store support center
associates, occupancy and operating costs of retail locations and store support centers, insurance-related
expenses, advertising costs, credit and debit card processing fees, and other administrative costs.
Advertising Expense
Advertising costs, including digital, television, radio and print, are expensed when the advertisement first appears.
Certain co-op advertising allowances that are reimbursements of specific, incremental, and identifiable costs
incurred to promote vendors’ products are recorded as an offset against advertising expense.
The following table presents net advertising expense included in SG&A:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Net advertising expense $ 1,085 $ 1,044 $ 909
Stock-Based Compensation
We are currently authorized to issue incentive and nonqualified stock options, stock appreciation rights, restricted
stock, restricted stock units, performance shares, performance units, and deferred shares to certain of our
associates and non-employee directors under certain stock incentive plans. We measure and recognize
compensation expense for all stock-based payment awards made to associates and non-employee directors based
on estimated fair values. The value of the portion of the award that is ultimately expected to vest is recognized as
stock-based compensation expense, on a straight-line basis, over the requisite service period or as restrictions
lapse. We include estimated forfeitures expected to occur when calculating stock-based compensation expense.
Additional information on our stock-based payment awards is included in Note 8.
Income Taxes
Income taxes are accounted for under the asset and liability method. We provide for federal, state, and foreign
income taxes currently payable, as well as for those deferred due to timing differences between reporting income
and expenses for financial statement purposes versus tax purposes. Deferred tax assets and liabilities are
recognized for the future tax consequences attributable to temporary differences between the financial statement
carrying amounts of existing assets and liabilities and their respective tax bases. Deferred tax assets and liabilities
are measured using enacted income tax rates expected to apply to taxable income in the years in which those
temporary differences are expected to be recovered or settled. The effect of a change in income tax rates is
recognized as income or expense in the period that includes the enactment date. We routinely evaluate the
likelihood of realizing the benefit of our deferred tax assets and may record a valuation allowance if, based on all
available evidence, we determine that it is more likely than not that some portion of the tax benefit will not be
realized.
We recognize the effect of income tax positions only if those positions are more likely than not of being sustained.
Recognized income tax positions are measured at the largest amount that is greater than 50% likely of being
realized. Changes in recognition or measurement are reflected in the period in which the change in judgment
occurs.
Table of Contents
Fiscal 2022 Form 10-K
46

We file a consolidated U.S. federal income tax return which includes certain eligible subsidiaries. Non-U.S.
subsidiaries and certain U.S. subsidiaries, which are consolidated for financial reporting purposes, are not eligible to
be included in our consolidated U.S. federal income tax return. Separate provisions for income taxes have been
determined for these entities. For unremitted earnings of our non-U.S. subsidiaries, we are required to make an
assertion regarding reinvestment or repatriation for tax purposes. For any earnings that we do not make a
permanent reinvestment assertion, we recognize a provision for deferred income taxes. For earnings where we
have made a permanent reinvestment assertion, no provision is recognized. See Note 5 for further discussion.
We recognize interest and penalties related to income tax matters in interest expense and SG&A, respectively, on
our consolidated statements of earnings. Accrued interest and penalties related to income tax matters are
recognized in other accrued expenses and other long-term liabilities on our consolidated balance sheets.
We are subject to global intangible low-taxed income (“GILTI”) tax, an incremental tax on foreign income. We have
made an accounting election to record this tax in the period the tax arises.
Comprehensive Income
Comprehensive income includes net earnings adjusted for certain gains and losses that are excluded from net
earnings and recognized within accumulated other comprehensive loss as a component of equity, which consist
primarily of foreign currency translation adjustments. Accumulated other comprehensive loss also includes net
losses on cash flow hedges that were immaterial as of January 29, 2023 and January 30, 2022. Reclassifications
from accumulated other comprehensive loss into earnings were immaterial in fiscal 2022, fiscal 2021, and fiscal
2020.
Foreign Currency Translation
Assets and liabilities denominated in a foreign currency are translated into U.S. dollars at the current rate of
exchange on the last day of the reporting period. Revenues and expenses are translated using average exchange
rates for the period and equity transactions are translated using the actual rate on the day of the transaction.
Cumulative foreign currency translation adjustments recorded in accumulated other comprehensive loss as of
January 29, 2023 and January 30, 2022 were losses of $597 million and $575 million, respectively.
Recently Adopted Accounting Pronouncements
ASU No. 2021-10. In November 2021, the FASB issued ASU No. 2021-10, “Government Assistance (Topic 832),” to
improve the transparency of government assistance received by business entities that are accounted for by
applying either the International Accounting Standards 20 grant model or Accounting Standards Codification
958-605 contribution model by analogy. Topic 832 requires disclosure of the nature of the transactions and the
related accounting policy used, the line items on the balance sheet and income statement that are affected and the
amounts applicable to each financial statement line item, and significant terms of the transactions. On January 31,
2022, we adopted ASU No. 2021-10 with no impact to our financial statements or related disclosures as the
transactions in scope of this guidance were immaterial.
Recently Issued Accounting Pronouncements
ASU No. 2022-04. In September 2022, the FASB issued ASU No. 2022-04, “Liabilities—Supplier Finance Programs
(Topic 405-50) - Disclosure of Supplier Finance Program Obligations,” to enhance the transparency of supplier
finance programs used by an entity in connection with the purchase of goods and services. The standard requires
entities that use supplier finance programs to disclose the key terms, including a description of payment terms, the
confirmed amount outstanding under the program at the end of each reporting period, a description of where those
obligations are presented on the balance sheet, and an annual rollforward, including the amount of obligations
confirmed and the amount paid during the period. The guidance does not affect the recognition, measurement, or
financial statement presentation of obligations covered by supplier finance programs. ASU No. 2022-04 is effective
for fiscal years beginning after December 15, 2022, including interim periods within those fiscal years, except for the
requirement on rollforward information, which is effective for fiscal years beginning after December 15, 2023. Early
adoption is permitted. We are currently evaluating the impact of the standard on our consolidated financial
statement disclosures.
ASU No. 2020-04. In March 2020, the FASB issued ASU No. 2020-04, “Reference Rate Reform (Topic 848):
Facilitation of the Effects of Reference Rate Reform on Financial Reporting,” which provides practical expedients
and exceptions for applying GAAP to contracts, hedging relationships, and other transactions affected by reference
rate reform if certain criteria are met. The expedients and exceptions provided by the amendments in this update
apply only to contracts, hedging relationships, and other transactions that reference LIBOR or another reference
rate expected to be discontinued as a result of reference rate reform. ASU No. 2020-04 is effective as of March 12,
Table of Contents
Fiscal 2022 Form 10-K
47
2020 and may be applied to contract modifications and hedging relationships from the beginning of an interim
period that includes or is subsequent to March 12, 2020. This guidance was subsequently amended by ASU No.
2022-06, “Reference Rate Reform (Topic 848): Deferral of the Sunset Date of Topic 848,” which was effective upon
issuance in December 2022 and extended the temporary relief provided by Topic 848 through December 31, 2024.
While the discontinuance of LIBOR will impact our interest rate swap agreements, we do not anticipate the transition
to a new reference rate and adoption of this standard will have a material impact on our consolidated financial
condition, results of operations, or cash flows.
Recent accounting pronouncements adopted or pending adoption not discussed above are either not applicable or
are not expected to have a material impact on our consolidated financial condition, results of operations, or cash
flows.
2. SEGMENT REPORTING AND NET SALES
We currently conduct our retail operations in the U.S., Canada, and Mexico, each of which represents one of our
three operating segments. Our operating segments reflect the way in which internally-reported financial information
is regularly reviewed by our chief operating decision maker to analyze performance, make decisions and allocate
resources. For disclosure purposes, we aggregate these three operating segments into one reportable segment due
to the similar nature of their operations and economic characteristics.
The following table presents net property and equipment, classified by geography:
in millions
January 29,
2023
January 30,
2022
January 31,
2021
Net property and equipment – in the U.S. $ 23,057 $ 22,696 $ 22,205
Net property and equipment – outside the U.S. 2,574 2,503
2,500
Net property and equipment $ 25,631 $ 25,199 $ 24,705
No sales to an individual customer accounted for more than 10% of revenue during any of the last three fiscal years.
The following table presents net sales, classified by geography:
Fiscal Fiscal Fiscal
in millions 2022 2021 2020
Net sales – in the U.S. $ 144,840 $ 138,920 $ 122,158
Net sales – outside the U.S. 12,563 12,237 9,952
Net sales $ 157,403 $ 151,157 $ 132,110
The following table presents net sales by products and services:
Fiscal Fiscal Fiscal
in millions 2022 2021 2020
Net sales – products $ 151,804 $ 145,745 $ 127,671
Net sales – services 5,599 5,412 4,439
Net sales $ 157,403 $ 151,157 $ 132,110
The following table presents major product lines and the related merchandising departments (and related services):
Major Product Line Merchandising Departments
Building Materials Building Materials, Electrical/Lighting, Lumber, Millwork, and Plumbing
Décor Appliances, Décor/Storage, Flooring, Kitchen and Bath, and Paint
Hardlines Hardware, Indoor Garden, Outdoor Garden, and Tools
Table of Contents
Fiscal 2022 Form 10-K
48
The following table presents net sales by major product line (and related services):
Fiscal Fiscal Fiscal
in millions
2022 2021 2020
Building Materials $ 59,533 $ 54,990 $ 46,521
Décor 52,322 50,437 43,415
Hardlines 45,548 45,730 42,174
Net sales $ 157,403 $ 151,157 $ 132,110
The following table presents net sales by merchandising department (and related services):
Fiscal Fiscal Fiscal
2022 2021 2020
dollars in millions
Net
Sales
% of
Net Sales
Net
Sales
% of
Net Sales
Net
Sales
% of
Net Sales
Appliances $ 14,461 9.2 % $ 14,232 9.4 % $ 11,865 9.0 %
Building Materials 11,298 7.2 9,823 6.5 8,656 6.6
Décor/Storage 6,357 4.0 6,095 4.0 4,959 3.8
Electrical/Lighting 13,746 8.7 13,473 8.9 11,178 8.5
Flooring 9,222 5.9 9,225 6.1 8,156 6.2
Hardware 8,104 5.1 7,873 5.2 7,312 5.5
Indoor Garden 14,990 9.5 15,546 10.3 14,649 11.1
Kitchen and Bath 11,102 7.1 10,432 6.9 8,383 6.3
Lumber 13,460 8.6 13,344 8.8 11,309 8.6
Millwork 8,423 5.4 7,412 4.9 6,460 4.9
Outdoor Garden 10,078 6.4 10,317 6.8 9,602 7.3
Paint 11,180 7.1 10,453 6.9 10,052 7.6
Plumbing 12,606 8.0 10,938 7.2 8,918 6.8
Tools 12,376 7.9 11,994 7.9 10,611 8.0
Total $ 157,403 100.0 % $ 151,157 100.0 % $ 132,110 100.0 %
—————
Note: Certain percentages may not sum to totals due to rounding.
3. PROPERTY AND LEASES
Net Property and Equipment
The following table presents components of net property and equipment:
in millions
January 29,
2023
January 30,
2022
Land $ 8,719 $ 8,617
Buildings and improvements 19,430 19,173
Furniture, fixtures, and equipment 16,564 16,441
Leasehold improvements 2,130 2,016
Construction in progress 1,297 1,139
Finance leases 4,135 3,943
Property and equipment, at cost 52,275 51,329
Less accumulated depreciation and finance lease amortization 26,644 26,130
Net property and equipment $ 25,631 $ 25,199
Table of Contents
Fiscal 2022 Form 10-K
49
The following table presents depreciation and finance lease amortization expense, including depreciation and
finance lease amortization expense included in cost of sales:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Depreciation and finance lease amortization expense $ 2,756 $ 2,650 $ 2,425
Leases
The following table presents the consolidated balance sheet location of assets and liabilities related to operating
and finance leases:
in millions Consolidated Balance Sheet Classification
January 29,
2023
January 30,
2022
Assets:
Operating lease assets Operating lease right-of-use assets $ 6,941 $ 5,968
Finance lease assets
(1)
Net property and equipment 2,899 2,896
Total lease assets $ 9,840 $ 8,864
Liabilities:
Current:
Operating lease liabilities Current operating lease liabilities $ 945 $ 830
Finance lease liabilities Current installments of long-term debt 231 198
Long-term:
Operating lease liabilities Long-term operating lease liabilities 6,226 5,353
Finance lease liabilities Long-term debt, excluding current installments 3,054 3,038
Total lease liabilities $ 10,456 $ 9,419
—————
(1) Finance lease assets are recorded net of accumulated amortization of $1.2 billion as of January 29, 2023 and $1.0 billion as of January 30,
2022.
The following table presents components of lease cost, excluding short-term lease cost and sublease income which
are immaterial:
Consolidated Statement of Earnings
Classification
(1)
Fiscal Fiscal Fiscal
in millions
2022 2021 2020
Operating lease cost Selling, general and administrative $ 1,169 $ 1,084 $ 782
Finance lease cost:
Amortization of leased assets Depreciation and amortization 282 250 167
Interest on lease liabilities Interest expense 125 127 112
Variable lease cost Selling, general and administrative 470 425 277
Total lease cost $ 2,046 $ 1,886 $ 1,338
—————
(1) Costs associated with our sourcing and distribution network are recorded in cost of sales, with the exception of interest on finance lease
liabilities.
The following table presents weighted average remaining lease terms and discount rates:
January 29,
2023
January 30,
2022
Weighted Average Remaining Lease Term (Years):
Operating leases 9 9
Finance leases 14 15
Weighted Average Discount Rate:
Operating leases 3.2 % 2.7 %
Finance leases 4.3 % 4.7 %
Table of Contents
Fiscal 2022 Form 10-K
50
The following table presents approximate future minimum payments under operating and finance leases at
January 29, 2023:
in millions
Operating
Leases
Finance
Leases
Fiscal 2023 $ 1,152 $ 347
Fiscal 2024 1,186 364
Fiscal 2025 1,032 406
Fiscal 2026 900 297
Fiscal 2027 769 278
Thereafter 3,446 2,449
Total lease payments 8,485 4,141
Less: imputed interest 1,314 856
Present value of lease liabilities $ 7,171 $ 3,285
—————
Note: We have excluded approximately $2.1 billion of leases (undiscounted basis) that have not yet commenced. These leases are expected to
commence primarily in fiscal 2023 with lease terms of up to 30 years.
The following table presents supplemental cash flow information related to leases:
Fiscal Fiscal Fiscal
in millions
2022 2021 2020
Cash paid for amounts included in the measurement of lease liabilities:
Operating cash flows – operating leases $ 1,157 $ 1,090 $ 1,022
Operating cash flows – finance leases 125 127 112
Financing cash flows – finance leases 241 182 122
Supplemental non-cash information:
Lease assets obtained in exchange for new operating lease liabilities 1,991 964 969
Lease assets obtained in exchange for new finance lease liabilities 322 672 1,730
4. DEBT AND DERIVATIVE INSTRUMENTS
Short-Term Debt
In July 2022, we expanded our commercial paper program from $3.0 billion to $5.0 billion to further enhance our
financial flexibility. All of our short-term borrowings in fiscal 2022 and fiscal 2021 were under our commercial paper
program. In connection with our program, we had back-up credit facilities with a consortium of banks for borrowings
up to $5.0 billion at January 29, 2023, which consisted of a five-year $3.5 billion credit facility scheduled to expire in
July 2027 and a 364-day $1.5 billion credit facility scheduled to expire in July 2023. These facilities replaced our
previously existing five-year $2.0 billion credit facility, which was scheduled to expire in December 2023, and our
364-day $1.0 billion credit facility, which was scheduled to expire in December 2022.
At January 29, 2023, we had no borrowings outstanding under our commercial paper program, and at January 30,
2022, we had $1.0 billion of borrowings outstanding under our commercial paper program with a weighted-average
interest rate of 0.1%.
The following table presents additional information on borrowings under our commercial paper program during fiscal
2022 and fiscal 2021:
Fiscal Fiscal
in millions
2022 2021
Maximum amount outstanding during the period $ 2,745 $ 1,368
Average daily short-term borrowings 269 45
Table of Contents
Fiscal 2022 Form 10-K
51

Long-Term Debt
The following table presents details of the components of our long-term debt:
Carrying Amount
(1)
in millions
Interest
Payable
Principal
Amount
January 29,
2023
January 30,
2022
Floating rate senior notes due March 2022 Quarterly $ — $ — $ 300
3.25% Senior notes due March 2022 Semi-annually — — 700
2.625% Senior notes due June 2022 Semi-annually — — 1,249
2.70% Senior notes due April 2023 Semi-annually 1,000 1,000 999
3.75% Senior notes due February 2024 Semi-annually 1,100 1,099 1,098
2.70% Senior notes due April 2025 Semi-annually 500 498 —
3.35% Senior notes due September 2025 Semi-annually 1,000 998 998
4.00% Senior notes due September 2025 Semi-annually 750 748 —
3.00% Senior notes due April 2026 Semi-annually 1,300 1,295 1,293
2.125% Senior notes due September 2026 Semi-annually 1,000 994 992
2.875% Senior notes due April 2027 Semi-annually 750 744 —
2.50% Senior notes due April 2027 Semi-annually 750 745 744
2.80% Senior notes due September 2027 Semi-annually 1,000 979 1,001
0.90% Senior notes due March 2028 Semi-annually 500 496 495
1.50% Senior notes due September 2028 Semi-annually 1,000 993 992
3.90% Senior notes due December 2028 Semi-annually 1,000 977 1,035
2.95% Senior notes due June 2029 Semi-annually 1,750 1,675 1,768
2.70% Senior notes due April 2030 Semi-annually 1,500 1,347 1,422
1.375% Senior notes due March 2031 Semi-annually 1,250 1,170 1,210
1.875% Senior notes due September 2031 Semi-annually 1,000 942 981
3.25% Senior notes due April 2032 Semi-annually 1,250 1,237 —
4.50% Senior notes due September 2032 Semi-annually 1,250 1,242 —
5.875% Senior notes due December 2036 Semi-annually 3,000 2,874 2,916
3.30% Senior notes due April 2040 Semi-annually 1,250 1,075 1,164
5.40% Senior notes due September 2040 Semi-annually 500 496 496
5.95% Senior notes due April 2041 Semi-annually 1,000 990 990
4.20% Senior notes due April 2043 Semi-annually 1,000 939 977
4.875% Senior notes due February 2044 Semi-annually 1,000 981 981
4.40% Senior notes due March 2045 Semi-annually 1,000 980 979
4.25% Senior notes due April 2046 Semi-annually 1,600 1,586 1,586
3.90% Senior notes due June 2047 Semi-annually 1,150 1,144 1,144
4.50% Senior notes due December 2048 Semi-annually 1,500 1,464 1,464
3.125% Senior notes due December 2049 Semi-annually 1,250 1,178 1,214
3.35% Senior notes due April 2050 Semi-annually 1,500 1,472 1,471
2.375% Senior notes due March 2051 Semi-annually 1,250 1,156 1,201
2.75% Senior notes due September 2051 Semi-annually 1,000 983 982
3.625% Senior notes due April 2052 Semi-annually 1,500 1,458 —
4.95% Senior notes due September 2052 Semi-annually 1,000 980 —
3.50% Senior notes due September 2056 Semi-annually 1,000 973 973
Total senior notes $ 41,150 $ 39,908 $ 35,815
Finance lease obligations; payable in varying
installments through April 30, 2076
$ 3,285 $ 3,236
Total long-term debt 43,193 39,051
Less current installments of long-term debt 1,231 2,447
Long-term debt, excluding current installments $ 41,962 $ 36,604
—————
(1) Includes unamortized discounts, premiums, debt issuance costs, and the effects of fair value hedges.
Table of Contents
Fiscal 2022 Form 10-K
52

September 2022 Issuance. In September 2022, we issued three tranches of senior notes.
• The first tranche consisted of $750 million of 4.00% senior notes due September 15, 2025 at a discount of
$0.3 million. Interest on these notes is due semi-annually on March 15 and September 15 of each year,
beginning March 15, 2023.
• The second tranche consisted of $1.25 billion of 4.50% senior notes due September 15, 2032 at a discount
of $1 million. Interest on these notes is due semi-annually on March 15 and September 15 of each year,
beginning March 15, 2023.
• The third tranche consisted of $1.0 billion of 4.95% senior notes due September 15, 2052 at a discount of
$14 million. Interest on these notes is due semi-annually on March 15 and September 15 of each year,
beginning March 15, 2023.
• Issuance costs totaled $15 million.
March 2022 Issuance. In March 2022, we issued four tranches of senior notes.
• The first tranche consisted of $500 million of 2.70% senior notes due April 15, 2025 at a discount of
$1 million. Interest on these notes is due semi-annually on April 15 and October 15 of each year, beginning
October 15, 2022.
• The second tranche consisted of $750 million of 2.875% senior notes due April 15, 2027 at a discount of
$4 million. Interest on these notes is due semi-annually on April 15 and October 15 of each year, beginning
October 15, 2022.
• The third tranche consisted of $1.25 billion of 3.25% senior notes due April 15, 2032 at a discount of
$6 million. Interest on these notes is due semi-annually on April 15 and October 15 of each year, beginning
October 15, 2022.
• The fourth tranche consisted of $1.5 billion of 3.625% senior notes due April 15, 2052 at a discount of
$32 million. Interest on these notes is due semi-annually on April 15 and October 15 of each year, beginning
October 15, 2022.
• Issuance costs totaled $22 million.
Repayments. In March 2022, we repaid our $700 million 3.25% senior notes and $300 million floating rate senior
notes at maturity. In May 2022, we repaid our $1.25 billion 2.625% senior notes, which had a maturity date of June
2022, at the Par Call Date for the notes.
Redemption. All of our senior notes may be redeemed by us at any time, in whole or in part, at the redemption
price plus accrued interest up to the redemption date. With respect to the 5.875% 2036 notes, the redemption price
is equal to the greater of (1) 100% of the principal amount of the notes to be redeemed, or (2) the sum of the
present values of the remaining scheduled payments of principal and interest on the notes to be redeemed that
would be due after the related redemption date. With respect to all other notes, prior to the Par Call Date, as defined
in the respective notes, the redemption price is equal to the greater of (1) 100% of the principal amount of the notes
to be redeemed or (2) the sum of the present values of the remaining scheduled payments of principal and interest
to the Par Call Date. On or after the Par Call Date, the redemption price is equal to 100% of the principal amount of
the notes. Additionally, if a Change in Control Triggering Event occurs, as defined in the notes, holders of all such
notes have the right to require us to redeem those notes at 101% of the aggregate principal amount of the notes
plus accrued interest up to the redemption date.
The indentures governing the notes do not generally limit our ability to incur additional indebtedness or require us to
maintain financial ratios or specified levels of net worth or liquidity. The indentures governing the notes contain
various customary covenants; however, none are expected to impact our liquidity or capital resources.
Table of Contents
Fiscal 2022 Form 10-K
53
Maturities of Long-Term Debt. The following table presents our long-term debt maturities, excluding finance
leases, as of January 29, 2023:
in millions Principal
Fiscal 2023 $ 1,000
Fiscal 2024 1,100
Fiscal 2025 2,250
Fiscal 2026 2,300
Fiscal 2027 2,500
Thereafter 32,000
Total $ 41,150
Derivative Instruments and Hedging Activities
We use derivative instruments as part of our normal business operations in the management of our exposure to
fluctuations in foreign currency exchange rates and interest rates on certain debt. Our objective in managing these
exposures is to decrease the volatility of cash flows affected by changes in the underlying rates and minimize the
risk of changes in the fair value of our senior notes.
Fair Value Hedges. We had outstanding interest rate swap agreements with combined notional amounts of $5.4
billion at January 29, 2023 and January 30, 2022. These agreements were accounted for as fair value hedges that
swap fixed for variable rate interest to hedge changes in the fair values of certain senior notes. At January 29, 2023,
the fair values of these agreements totaled $778 million, all of which is recognized in other long-term liabilities on
the consolidated balance sheet. At January 30, 2022, the fair values of these agreements totaled $191 million, with
$58 million recognized in other assets and $249 million recognized in other long-term liabilities on the consolidated
balance sheet. All of our interest rate swap agreements designated as fair value hedges meet the shortcut method
requirements under GAAP. Accordingly, the changes in the fair values of these agreements offset the changes in the
fair value of the hedged long-term debt.
Cash Flow Hedges. At January 29, 2023 and January 30, 2022, we had outstanding foreign currency forward
contracts accounted for as cash flow hedges, which hedge the variability of forecasted cash flows associated with
certain payments made in our foreign operations. At January 29, 2023 and January 30, 2022, the notional amounts
and the fair values of these contracts were not material. Additionally, the realized and unrealized gains and losses
on these instruments were not material during fiscal 2022, fiscal 2021, and fiscal 2020.
We also settled forward-starting interest rate swap agreements in prior years, which were used to hedge the
variability in future interest payments attributable to changing interest rates on forecasted debt issuances.
Unamortized losses on these forward-starting swaps, which were designated as cash flow hedges, are being
amortized to interest expense over the life of the respective notes. Unamortized losses recognized on these swaps
remaining in accumulated other comprehensive loss were immaterial as of January 29, 2023 and January 30, 2022,
as were the losses recognized within interest expense for fiscal 2022, fiscal 2021, and fiscal 2020.
We expect an immaterial amount recorded in accumulated other comprehensive loss as of January 29, 2023 to be
reclassified into earnings within the next 12 months.
Net Investment Hedges. During fiscal 2022, we issued foreign currency forward contracts accounted for as net
investment hedges, which hedged against foreign currency exposure on our net investment in certain subsidiaries.
These foreign currency forward contracts were immaterial and were settled in fiscal 2022. The related foreign
currency translation adjustment amounts recorded in accumulated other comprehensive loss upon settlement were
also immaterial. There were no arrangements accounted for as net investment hedges outstanding as of
January 29, 2023 or January 30, 2022.
Collateral. We generally enter into master netting arrangements, which are designed to reduce credit risk by
permitting net settlement of transactions with the same counterparty. To further limit our credit risk, we enter into
collateral security arrangements that provide for collateral to be received or posted when the net fair value of certain
derivative instruments exceeds or falls below contractually established thresholds. The cash collateral posted by the
Company related to derivative instruments under our collateral security arrangements was $634 million as of
January 29, 2023, which was recorded in other current assets on the consolidated balance sheet. We did not hold
any cash collateral as of January 29, 2023, and cash collateral both held and posted was immaterial as of
January 30, 2022.
Table of Contents
Fiscal 2022 Form 10-K
54
5. INCOME TAXES
Provision for Income Taxes
The following table presents our earnings before the provision for income taxes:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
United States $ 20,990 $ 20,320 $ 16,013
Foreign 1,487 1,417 965
Total $ 22,477 $ 21,737 $ 16,978
The following table presents our provision for income taxes:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Current:
Federal $ 3,918 $ 4,066 $ 3,462
State 880 981 928
Foreign 436 511 329
Total current 5,234 5,558 4,719
Deferred:
Federal 102 (155) (404)
State 61 (11) (209)
Foreign (25) (88) 6
Total deferred 138 (254) (607)
Provision for income taxes $ 5,372 $ 5,304 $ 4,112
The following table presents our combined federal, state, and foreign effective tax rates:
Fiscal Fiscal Fiscal
2022 2021 2020
Combined federal, state, and foreign effective tax rates 23.9 % 24.4 % 24.2 %
The following table presents the reconciliation of our provision for income taxes at the federal statutory rate of 21%
to the actual tax expense:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Income taxes at federal statutory rate $ 4,720 $ 4,565 $ 3,565
State income taxes, net of federal income tax benefit 743 766 568
Other, net (91) (27) (21)
Total $ 5,372 $ 5,304 $ 4,112
On August 16, 2022, the Inflation Reduction Act of 2022 (“2022 Tax Act”) was enacted into law. The key tax
provisions include a 15% minimum tax on adjusted financial statement income. We do not expect any impact to the
Company’s effective tax rate as a result of the new 15% minimum tax under the 2022 Tax Act.
Table of Contents
Fiscal 2022 Form 10-K
55
Deferred Taxes
The following table presents the tax effects of temporary differences that give rise to significant portions of our
deferred tax assets and deferred tax liabilities:
in millions
January 29,
2023
January 30,
2022
Assets:
Deferred compensation $ 236 $ 471
Accrued self-insurance liabilities 276 272
State income taxes 149 138
Merchandise inventories 30 —
Non-deductible reserves 318 250
Net operating losses 115 150
Lease liabilities 1,879 1,528
Deferred revenue 148 121
Other 56 67
Total deferred tax assets 3,207 2,997
Valuation allowance (5) (10)
Total deferred tax assets, net of valuation allowance 3,202 2,987
Liabilities:
Merchandise inventories — (14)
Property and equipment (992) (902)
Goodwill and other intangibles (953) (985)
Lease right-of-use assets (1,799) (1,473)
Tax on unremitted earnings (63) (74)
Other (95) (104)
Total deferred tax liabilities (3,902) (3,552)
Net deferred tax liabilities $ (700) $ (565)
The following table presents our noncurrent deferred tax assets and noncurrent deferred tax liabilities, netted by tax
jurisdiction, as presented on the consolidated balance sheets:
in millions Consolidated Balance Sheet Classification
January 29,
2023
January 30,
2022
Deferred tax assets Other assets $ 319 $ 344
Deferred tax liabilities Deferred income taxes (1,019) (909)
Net deferred tax liabilities $ (700) $ (565)
As of January 29, 2023, we recorded deferred tax assets of $115 million for net operating losses, primarily related to
state jurisdictions. These losses expire at various dates beginning in 2023. We have concluded that it is more likely
than not that tax benefits related to substantially all net operating losses will be realized based upon the expectation
that we will generate the necessary taxable income in future periods.
Reinvestment of Unremitted Earnings
Substantially all of our current year foreign cash earnings in excess of working capital and cash needed for strategic
investments are not intended to be indefinitely reinvested offshore. Therefore, the tax effects of repatriation for
applicable state taxes and foreign withholding taxes of such cash earnings have been provided for in the
accompanying consolidated statements of earnings. We have the intent and ability to reinvest substantially all of the
$4.1 billion of non-cash unremitted earnings of our non-U.S. subsidiaries indefinitely. Accordingly, no provision for
state taxes or foreign withholding taxes was recorded on these unremitted earnings in the accompanying
consolidated statements of earnings. It is impracticable for us to determine the amount of unrecognized deferred tax
liabilities on these indefinitely reinvested earnings due to the complexities associated with the hypothetical
calculation.
Table of Contents
Fiscal 2022 Form 10-K
56
Tax Return Examination Status
Our income tax returns are routinely examined by U.S. federal, state and local, and foreign tax authorities. As of
January 29, 2023, the Company is no longer subject to U.S. federal examinations by tax authorities for years before
fiscal 2010. Our U.S. federal tax returns for fiscal years 2010 through 2021, with the exception of 2015, are currently
under examination by the IRS. With respect to the fiscal years 2010 to 2014, the IRS has issued a proposed
adjustment relating to transfer pricing between our entities in the U.S. and China. We are defending our position
using all available remedies. There are also ongoing U.S. state and local audits and other foreign audits covering
fiscal years 2013 through 2020. We do not expect the results from any ongoing income tax audit to have a material
impact on our consolidated financial condition, results of operations, or cash flows.
Over the next twelve months, it is reasonably possible that the resolution of federal and state tax examinations, as
well as the expiration of statutes of limitations, could reduce our unrecognized tax benefits by an immaterial amount.
We do not anticipate the resolution of these matters will result in a material change to our consolidated financial
condition or results of operations.
Unrecognized Tax Benefits
The following table reconciles the beginning and ending amount of our gross unrecognized tax benefits:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Unrecognized tax benefits balance at beginning of fiscal year $ 570 $ 540 $ 473
Additions based on tax positions related to the current year 75 80 75
Additions for tax positions of prior years 22 24 72
Reductions for tax positions of prior years (7) (40) (53)
Reductions due to settlements (1) (29) (22)
Reductions due to lapse of statute of limitations (16) (5) (5)
Unrecognized tax benefits balance at end of fiscal year $ 643 $ 570 $ 540
Unrecognized tax benefits that if recognized would affect our annual effective income tax rate on net earnings were
$537 million, $479 million, and $458 million at January 29, 2023, January 30, 2022, and January 31, 2021,
respectively.
Interest and Penalties
Net adjustments to accruals for interest and penalties associated with uncertain tax positions were immaterial in
fiscal 2022, fiscal 2021, and fiscal 2020. Our total accrued interest and penalties associated with uncertain tax
positions were immaterial as of January 29, 2023 and January 30, 2022.
6. STOCKHOLDERS’ EQUITY
Stock Rollforward
The following table presents a reconciliation of the number of shares of our common stock outstanding and cash
dividends per share:
shares in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Common stock:
Balance at beginning of year 1,792 1,789 1,786
Shares issued under employee stock plans, net 2 3 3
Balance at end of year 1,794 1,792 1,789
Treasury stock:
Balance at beginning of year (757) (712) (709)
Repurchases of common stock (21) (45) (3)
Balance at end of year (778) (757) (712)
Shares outstanding at end of year 1,016 1,035 1,077
Cash dividends per share $ 7.60 $ 6.60 $ 6.00
Table of Contents
Fiscal 2022 Form 10-K
57
Share Repurchases
In August 2022, our Board of Directors approved a $15.0 billion share repurchase authorization that replaced the
previous authorization of $20.0 billion, which was approved in May 2021. This new authorization does not have a
prescribed expiration date. As of January 29, 2023, approximately $12.5 billion of the $15.0 billion share repurchase
authorization remained available.
In March 2020, we suspended our share repurchases to enhance our liquidity position as a result of the COVID-19
pandemic. We resumed share repurchases in the first quarter of fiscal 2021.
The following table presents information about our repurchases of common stock, all of which were completed
through open market purchases:
Fiscal Fiscal Fiscal
in millions
2022 2021 2020
Total number of shares repurchased 21 45 3
Total cost of shares repurchased $ 6,504 $ 15,001 $ 597
These amounts may differ from the repurchases of common stock amounts in the consolidated statements of cash
flows due to unsettled share repurchases at the end of a period.
7. FAIR VALUE MEASUREMENTS
The fair value of an asset is considered to be the price at which the asset could be sold in an orderly transaction
between unrelated knowledgeable and willing parties. A liability’s fair value is defined as the amount that would be
paid to transfer the liability to a new obligor, rather than the amount that would be paid to settle the liability with the
creditor. Assets and liabilities recorded at fair value are measured using a three-tier fair value hierarchy, which
prioritizes the inputs used in measuring fair value. The levels of the fair value hierarchy are:
• Level 1: observable inputs such as quoted prices in active markets for identical assets or liabilities;
• Level 2: inputs other than quoted prices in active markets in Level 1 that are either directly or indirectly
observable; and
• Level 3: unobservable inputs for which little or no market data exists, therefore requiring management
judgment to develop the Company’s own models with estimates and assumptions.
Assets and Liabilities Measured at Fair Value on a Recurring Basis
The following table presents the assets and liabilities that are measured at fair value on a recurring basis:
January 29, 2023 January 30, 2022
in millions Level 1 Level 2 Level 3 Level 1 Level 2 Level 3
Derivative agreements – assets $ — $ — $ — $ — $ 58 $ —
Derivative agreements – liabilities — (778) — — (249) —
Total $ — $ (778) $ — $ — $ (191) $ —
The fair values of our derivative instruments are determined using an income approach and Level 2 inputs, which
include the respective interest rate or foreign currency forward curves and discount rates. Our derivative
instruments are discussed further in Note 4.
Assets and Liabilities Measured at Fair Value on a Nonrecurring Basis
Long-lived assets, goodwill, and other intangible assets are subject to nonrecurring fair value measurement for the
assessment of impairment. We did not have any material assets or liabilities that were measured at fair value on a
nonrecurring basis during fiscal 2022, fiscal 2021, or fiscal 2020.
Other Fair Value Disclosures
The carrying amounts of cash and cash equivalents, receivables, short-term debt, and accounts payable
approximate fair value due to their short-term nature.
Table of Contents
Fiscal 2022 Form 10-K
58
The following table presents the aggregate fair values and carrying values of our senior notes:
January 29, 2023 January 30, 2022
in millions
Fair Value
(Level 1)
Carrying
Value
Fair Value
(Level 1)
Carrying
Value
Senior notes $ 38,537 $ 39,908 $ 39,397 $ 35,815
8. STOCK-BASED COMPENSATION
Omnibus Stock Incentive Plans
The Home Depot, Inc. Omnibus Stock Incentive Plan, as Amended and Restated May 19, 2022 (the “Omnibus
Plan”) and The Home Depot, Inc. 1997 Omnibus Stock Incentive Plan (the “1997 Plan” and collectively with the
Omnibus Plan, the “Plans”) provide that incentive and nonqualified stock options, stock appreciation rights,
restricted stock, restricted stock units, performance shares, performance units, deferred shares, and other stock-
based awards may be issued to certain of our associates and non-employee directors. Under the Omnibus Plan, the
maximum number of shares of our common stock authorized for issuance is 80 million shares plus a number of
shares (not to exceed 10 million) related to underlying awards outstanding as of May 19, 2022, which can be
returned to the share pool if those awards are subsequently terminated or expire unexercised, or are cancelled,
forfeited or lapse for any reason, with any award other than a stock option or stock appreciation right reducing the
number of shares available for issuance by 2.11 shares. At January 29, 2023, there were approximately 80 million
shares available for future grants under the Omnibus Plan. No additional equity awards could be issued from the
1997 Plan after May 26, 2005.
The following table presents total stock-based compensation expense, net of estimated forfeitures, including
expense related to our ESPPs, and related income tax benefit:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Pre-tax stock-based compensation expense $ 367 $ 403 $ 310
Income tax benefit (73) (86) (58)
After-tax stock-based compensation expense $ 294 $ 317 $ 252
At January 29, 2023, there was $424 million of unrecognized stock-based compensation expense, which is
expected to be recognized over a weighted average period of two years.
The award types issued under the Plans are as follows:
Stock Options. Under the terms of the Plans, incentive stock options and nonqualified stock options must have an
exercise price at or above the fair market value of our stock on the date of the grant. Typically, nonqualified stock
options vest at the rate of 25% per year commencing on the second anniversary date of the grant and expire on the
tenth anniversary date of the grant. Additionally, a majority of our stock options may become non-forfeitable upon
the associate reaching age 60, provided the associate has had five years of continuous service. No incentive stock
options have been issued under the Omnibus Plan.
We estimate the fair value of stock option awards on the date of grant using the Black-Scholes option-pricing model.
Our determination of fair value of stock option awards on the date of grant using the Black-Scholes option-pricing
model is affected by our stock price as well as assumptions regarding a number of variables.
The following table presents the per share weighted average fair value of stock options granted and the
assumptions used in determining fair value at the date of grant using the Black-Scholes option-pricing model:
Fiscal Fiscal Fiscal
2022 2021 2020
Per share weighted average fair value $ 70.21 $ 57.71 $ 36.77
Risk-free interest rate 2.5 % 1.0 % 0.6 %
Assumed volatility 27.0 % 26.5 % 29.9 %
Assumed dividend yield 2.4 % 2.2 % 3.1 %
Assumed lives of options 6 years 6 years 6 years
Table of Contents
Fiscal 2022 Form 10-K
59

The following table presents a summary of stock option activity by number of shares and weighted average exercise
price during fiscal 2022:
shares in thousands
Number of
Shares
Weighted Average
Exercise Price
Outstanding at beginning of year 3,641 $ 150.30
Granted 302 316.09
Exercised (292) 98.66
Forfeited (25) 238.56
Outstanding at end of year 3,626 167.66
The following table presents the total intrinsic value of stock options exercised:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Total intrinsic value of stock options exercised $ 61 $ 237 $ 217
The following table presents details regarding outstanding and exercisable stock options at January 29, 2023:
shares in thousands, dollars in millions, except for per share
amounts
Number of
Shares
Intrinsic
Value
Weighted
Average
Remaining Life
Weighted
Average
Exercise Price
Outstanding 3,626 $ 541 4.6 years $ 167.66
Exercisable 2,448 457 3.2 years 130.00
Shares of common stock issued from stock option exercises may be issued from authorized and unissued common
stock or treasury stock.
Restricted Stock and Performance Share Awards. Restrictions on the restricted stock issued under the Plans
generally lapse over various periods up to five years. At the grant date of the award, recipients of restricted stock
are granted voting rights and generally receive dividends on unvested shares, paid in the form of cash on each
dividend payment date. Dividends paid on unvested shares were immaterial for fiscal 2022, fiscal 2021, and fiscal
2020. Additionally, the majority of our restricted stock awards may become non-forfeitable upon the associate’s
attainment of age 60, provided the associate has had five years of continuous service.
We have also granted performance share awards under the Plans. These awards provide for the issuance of shares
of our common stock at the end of the three-year performance cycle based upon our performance against target
average ROIC and operating profit over that performance cycle. Additionally, the awards become non-forfeitable
upon the associate’s attainment of age 60, provided the associate has had five years of continuous service and
minimum performance targets are achieved. Recipients of performance share awards have no voting rights until the
shares are issued following completion of the performance period. Dividend equivalents accrue on the performance
shares (as reinvested shares) and are paid upon the payout of the award based upon the actual number of shares
earned. The fair value of the restricted stock and performance shares is based on the closing stock price on the
date of grant and is expensed over the period during which the restrictions lapse.
Restricted Stock Units. Each restricted stock unit entitles the associate to one share of common stock to be
received upon vesting up to five years after the grant date. Additionally, the majority of these awards may become
non-forfeitable upon the associate reaching age 60, provided the associate has had five years of continuous
service. Recipients of restricted stock units have no voting rights until the vesting of the award. Recipients receive
dividend equivalents that accrue on unvested units and are paid out in the form of additional shares of stock on the
vesting date. The fair value of the restricted stock units is based on the closing stock price on the date of grant and
is expensed over the period during which the units vest.
Table of Contents
Fiscal 2022 Form 10-K
60
The following table presents a summary of restricted stock, performance shares, and restricted stock unit activity
during fiscal 2022:
shares in thousands
Number of
Shares
Weighted Average
Grant Date Fair Value
Nonvested at beginning of year 3,709 $ 218.60
Granted 1,441 304.57
Vested (1,516) 191.82
Forfeited (275) 260.13
Nonvested at end of year 3,359 261.66
The following table presents the total fair value of restricted stock, performance shares, and restricted stock units
vested:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Total fair value vested $ 479 $ 405 $ 271
Deferred Shares. We grant awards of deferred shares to non-employee directors under the Plans. Each deferred
share entitles the non-employee director to one share of common stock to be received following termination of
Board service. Recipients of deferred shares have no voting rights and receive dividend equivalents that accrue and
are paid out in the form of additional shares of stock upon payout of the underlying shares following termination of
service. The fair value of the deferred shares is based on the closing stock price on the date of grant and is
expensed immediately upon grant.
The following table presents deferred shares granted to non-employee directors:
Fiscal Fiscal Fiscal
2022 2021 2020
Deferred shares granted to non-employee directors 19,000 15,000 18,000
Employee Stock Purchase Plans
We maintain two ESPPs: a U.S. and a non-U.S. plan. The plan for U.S. associates is a tax-qualified plan under
Section 423 of the Internal Revenue Code. The non-U.S. plan is not a Section 423 plan. At January 29, 2023, there
were approximately 16 million shares available under the U.S. plan and approximately 18 million shares available
under the non-U.S. plan. The purchase price of shares under the ESPPs is equal to 85% of the stock’s fair market
value on the last day of the purchase period, which is a six-month period ending on December 31 and June 30 of
each year. During fiscal 2022, there were approximately 1 million shares purchased under the ESPPs at an average
price of $247.86. Under the outstanding ESPPs at January 29, 2023, associates have contributed $22 million to
purchase shares at 85% of the stock’s fair market value on the last day of the current purchase period, June 30,
2023.
9. EMPLOYEE BENEFIT PLANS
We maintain active defined contribution retirement plans for our associates (the “Benefit Plans”). All associates
satisfying certain service requirements are eligible to participate in the Benefit Plans. We make cash contributions
each payroll period up to specified percentages of associates’ contributions as approved by our Board of Directors.
We also maintain the Restoration Plans to provide certain associates deferred compensation that they would have
received under the Benefit Plans as a matching contribution if not for the maximum compensation limits under the
Internal Revenue Code. We fund the Restoration Plans through contributions made to grantor trusts, which are then
used to purchase shares of our common stock in the open market.
The following table presents our contributions to the Benefit Plans and the Restoration Plans:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Contributions to the Benefit Plans and the Restoration Plans $ 280 $ 278 $ 267
At January 29, 2023, the Benefit Plans and the Restoration Plans held a total of 5.3 million shares of our common
stock in trusts for plan participants.
Table of Contents
Fiscal 2022 Form 10-K
61
10. WEIGHTED AVERAGE COMMON SHARES
The following table presents the reconciliation of our basic to diluted weighted average common shares:
in millions
Fiscal Fiscal Fiscal
2022 2021 2020
Basic weighted average common shares 1,022 1,054 1,074
Effect of potentially dilutive securities
(1)
3 4 4
Diluted weighted average common shares 1,025 1,058 1,078
Anti-dilutive securities excluded from diluted weighted average
common shares 1 — —
—————
(1) Represents the dilutive impact of stock-based awards.
11. COMMITMENTS AND CONTINGENCIES
At January 29, 2023, we had outstanding letters of credit totaling $486 million, primarily related to certain business
transactions, including insurance programs, trade contracts, and construction contracts.
We are involved in litigation arising in the normal course of business. In management’s opinion, any such litigation is
not expected to have a material adverse effect on our consolidated financial condition, results of operations, or cash
flows.
12. HD SUPPLY ACQUISITION
On November 16, 2020, we announced that we entered into a definitive agreement to acquire HD Supply, a leading
national distributor of MRO products to multifamily, hospitality, healthcare, and government housing facilities, among
others. Under the terms of the merger agreement, a subsidiary of Home Depot made a cash tender offer to
purchase all outstanding shares of the common stock of HD Supply Holdings, Inc., the ultimate parent entity of HD
Supply, for $56 per share, and the acquisition was completed on December 24, 2020. The acquisition was funded
through cash on hand, a portion of which was replaced with the proceeds from our issuance of $3.0 billion of senior
notes in January 2021.
The following table summarizes total purchase consideration:
in millions
Total cash consideration for outstanding shares $ 8,637
Value of stock-based awards attributed to services already rendered
(1)
55
Total purchase consideration $ 8,692
—————
(1) In connection with the completion of the acquisition, all HD Supply stock-based awards were cash settled for an aggregate value of
$111 million. As the settlement of the awards was at the discretion of the Company, the portion of the fair value of the awards attributed to
services previously provided of $55 million was included as part of purchase consideration, with the remaining $56 million recognized as
post-combination expense within SG&A in our consolidated statement of earnings for fiscal 2020.
The total purchase consideration of $8.7 billion, less cash acquired of $912 million, resulted in a net cash outflow of
$7.8 billion on the consolidated statement of cash flows in fiscal 2020.
Net sales and net earnings for fiscal 2020 attributable to HD Supply after the completion of the acquisition were
immaterial. Pro forma results of operations would not be materially different as a result of the acquisition and
therefore are not presented.
Item 9. Changes in and Disagreements With Accountants on Accounting and Financial
Disclosure.
Not applicable.
Table of Contents
Fiscal 2022 Form 10-K
62

Item 9A. Controls and Procedures.
DISCLOSURE CONTROLS AND PROCEDURES
We maintain disclosure controls and procedures as defined in Rule 13a-15(e) under the Exchange Act that are
designed to ensure that information required to be disclosed in our Exchange Act reports is recorded, processed,
summarized, and reported within the time periods specified in the SEC’s rules and forms, and that such information
is accumulated and communicated to our management, including our Chief Executive Officer and Chief Financial
Officer, as appropriate, to allow timely decisions regarding required disclosure.
Management, with the participation of our Chief Executive Officer and Chief Financial Officer, has evaluated the
effectiveness of our disclosure controls and procedures as of the end of the period covered by this report. Based on
that evaluation, our Chief Executive Officer and Chief Financial Officer have concluded that, as of the end of the
period covered by this report, our disclosure controls and procedures were effective.
MANAGEMENT’S REPORT ON INTERNAL CONTROL OVER FINANCIAL REPORTING
Our management is responsible for establishing and maintaining adequate internal control over financial reporting,
as such term is defined in Rule 13a-15(f) promulgated under the Exchange Act. Under the supervision and with the
participation of our management, including our Chief Executive Officer and Chief Financial Officer, we conducted an
evaluation of the effectiveness of our internal control over financial reporting as of January 29, 2023 based on the
framework in Internal Control – Integrated Framework (2013) issued by the Committee of Sponsoring Organizations
of the Treadway Commission. Based on our evaluation, our management concluded that our internal control over
financial reporting was effective as of January 29, 2023 in providing reasonable assurance regarding the reliability
of financial reporting and the preparation of financial statements for external purposes in accordance with GAAP.
The effectiveness of our internal control over financial reporting as of January 29, 2023 has been audited by KPMG
LLP, an independent registered public accounting firm, as stated in their report which is included herein.
CHANGES IN INTERNAL CONTROL OVER FINANCIAL REPORTING
We are in the process of an ongoing business transformation initiative, which includes upgrading and migrating
certain accounting and finance systems. We plan to continue to migrate additional business processes over the
course of the next few years and have modified and will continue to modify the design and implementation of certain
internal control processes as the transformation continues.
Except as described above, there were no other changes in our internal control over financial reporting during the
fiscal quarter ended January 29, 2023 that have materially affected, or are reasonably likely to materially affect, our
internal control over financial reporting.
Table of Contents
Fiscal 2022 Form 10-K
63

REPORT OF INDEPENDENT REGISTERED PUBLIC ACCOUNTING FIRM
To the Stockholders and the Board of Directors
The Home Depot, Inc.:
Opinion on Internal Control Over Financial Reporting
We have audited The Home Depot, Inc. and subsidiaries' (the Company) internal control over financial reporting as
of January 29, 2023, based on criteria established in Internal Control – Integrated Framework (2013) issued by the
Committee of Sponsoring Organizations of the Treadway Commission. In our opinion, the Company maintained, in
all material respects, effective internal control over financial reporting as of January 29, 2023, based on criteria
established in Internal Control – Integrated Framework (2013) issued by the Committee of Sponsoring
Organizations of the Treadway Commission.
We also have audited, in accordance with the standards of the Public Company Accounting Oversight Board (United
States) (PCAOB), the consolidated balance sheets of the Company as of January 29, 2023 and January 30, 2022,
the related consolidated statements of earnings, comprehensive income, stockholders’ equity, and cash flows for
each of the fiscal years in the three-year period ended January 29, 2023, and the related notes (collectively, the
consolidated financial statements), and our report dated March 15, 2023 expressed an unqualified opinion on those
consolidated financial statements.
Basis for Opinion
The Company’s management is responsible for maintaining effective internal control over financial reporting and for
its assessment of the effectiveness of internal control over financial reporting, included in the accompanying
Management’s Report on Internal Control Over Financial Reporting. Our responsibility is to express an opinion on
the Company’s internal control over financial reporting based on our audit. We are a public accounting firm
registered with the PCAOB and are required to be independent with respect to the Company in accordance with the
U.S. federal securities laws and the applicable rules and regulations of the Securities and Exchange Commission
and the PCAOB.
We conducted our audit in accordance with the standards of the PCAOB. Those standards require that we plan and
perform the audit to obtain reasonable assurance about whether effective internal control over financial reporting
was maintained in all material respects. Our audit of internal control over financial reporting included obtaining an
understanding of internal control over financial reporting, assessing the risk that a material weakness exists, and
testing and evaluating the design and operating effectiveness of internal control based on the assessed risk. Our
audit also included performing such other procedures as we considered necessary in the circumstances. We
believe that our audit provides a reasonable basis for our opinion.
Definition and Limitations of Internal Control Over Financial Reporting
A company’s internal control over financial reporting is a process designed to provide reasonable assurance
regarding the reliability of financial reporting and the preparation of financial statements for external purposes in
accordance with generally accepted accounting principles. A company’s internal control over financial reporting
includes those policies and procedures that (1) pertain to the maintenance of records that, in reasonable detail,
accurately and fairly reflect the transactions and dispositions of the assets of the company; (2) provide reasonable
assurance that transactions are recorded as necessary to permit preparation of financial statements in accordance
with generally accepted accounting principles, and that receipts and expenditures of the company are being made
only in accordance with authorizations of management and directors of the company; and (3) provide reasonable
assurance regarding prevention or timely detection of unauthorized acquisition, use, or disposition of the company’s
assets that could have a material effect on the financial statements.
Because of its inherent limitations, internal control over financial reporting may not prevent or detect misstatements.
Also, projections of any evaluation of effectiveness to future periods are subject to the risk that controls may
become inadequate because of changes in conditions, or that the degree of compliance with the policies or
procedures may deteriorate.
/s/ KPMG LLP
Atlanta, Georgia
March 15, 2023
Table of Contents
Fiscal 2022 Form 10-K
64

Item 9B. Other Information.
Not applicable.
Item 9C. Disclosure Regarding Foreign Jurisdictions that Prevent Inspections.
Not applicable.
PART III
Item 10. Directors, Executive Officers and Corporate Governance.
Information required by this item, other than the information regarding the executive officers set forth below, is
incorporated by reference to the sections entitled “Election of Directors,” “Corporate Governance,” “General,” and
“Audit Committee Report” in our Proxy Statement for the 2023 Annual Meeting of Shareholders (“Proxy Statement”).
Executive officers are appointed by, and serve at the pleasure of, the Board of Directors. Our executive officers are
as follows:
WILLIAM D. BASTEK, age 56, has been Executive Vice President – Merchandising, since March 2023. From
January 2019 to March 2023, Mr. Bastek served as Senior Vice President of Merchandising, Hardlines for the
Company, responsible for merchandising and marketing strategies for hardware and garden. Prior to that role, he
was Merchandising Vice President of hardware and tools from December 2013 to January 2019. Mr. Bastek began
his career in 1989 at HD Supply, formerly known as Maintenance Warehouse, which was originally acquired by the
Company in 1997. Mr. Bastek has served in various roles of increasing responsibility, including Global Product
Merchant, Senior Merchant, Divisional Merchandise Manager and Merchandising Vice President for building
materials.
ANN-MARIE CAMPBELL, age 57, has been Executive Vice President – U.S. Stores and International Operations
since October 2020. From February 2016 to October 2020, she served as Executive Vice President – U.S. Stores,
from January 2009 to February 2016, she served as Division President of the Southern Division, and from
December 2005 to January 2009, she served as Vice President – Vendor Services. Ms. Campbell began her career
with The Home Depot in 1985 as a cashier and has held roles of increasing responsibility since she joined the
Company, including vice president roles in the Company’s operations, merchandising, and marketing departments.
She serves as a director of Workday, Inc., a financial and human capital management software vendor.
MATTHEW A. CAREY, age 58, has been Executive Vice President – Customer Experience since April 2022. He
served as Executive Vice President and Chief Information Officer from September 2008 to April 2022. From January
2006 through August 2008, he served as Senior Vice President and Chief Technology Officer at eBay Inc., an online
commerce platform. Mr. Carey was previously with Wal-Mart Stores, Inc., a general merchandise retailer, from June
1985 to December 2005. His final position with Wal-Mart was Senior Vice President and Chief Technology Officer.
He serves as a director of Chipotle Mexican Grill, Inc., which owns and operates restaurants in the U.S. and
internationally.
JOHN DEATON, age 49, has been Executive Vice President – Supply Chain & Product Development since
November 2021. From April 2021 to October 2021, he served as Senior Vice President – Operations, from May
2017 to April 2021, he served as Senior Vice President – Supply Chain, from July 2011 to April 2017 he served as
Senior Vice President – Brand and Product Development, and from April 2007 to June 2011 he served as Vice
President – Supply Chain.
EDWARD P. DECKER, age 60, has served as our Chair since October 2022, and as our President and Chief
Executive Officer since March 2022. He served as our President and Chief Operating Officer from October 2020
through February 2022. From August 2014 to October 2020, he served as Executive Vice President –
Merchandising, and from October 2006 through July 2014, he served as Senior Vice President – Retail Finance,
Pricing Analytics, and Assortment Planning. Mr. Decker joined The Home Depot in 2000 and held various strategic
planning roles, including serving as Vice President – Strategic Business Development from November 2002 to April
2006 and Senior Vice President – Strategic Business and Asset Development from April 2006 to September 2006.
Prior to joining the Company, Mr. Decker held various positions in strategic planning, business development,
finance, and treasury at Kimberly-Clark Corp. and Scott Paper Co., both of which are consumer products
companies.
Table of Contents
Fiscal 2022 Form 10-K
65

TIMOTHY A. HOURIGAN, age 66, has been Executive Vice President – Human Resources since June 2017. From
February 2016 through June 2017, he served as Division President of the Southern Division. Prior to his role as
Division President, Mr. Hourigan served in various human resources roles with the Company, including Vice
President – Human Resources, U.S. Stores and Operations from September 2013 to February 2016; Vice President
– Compensation and Benefits from February 2007 to September 2013; and Vice President – Human Resources
from July 2002 to February 2007.
RICHARD V. McPHAIL, age 52, has been Executive Vice President and Chief Financial Officer since September
2019. From August 2017 through August 2019, he served as Senior Vice President, Finance Control and
Administration of the Company, and was responsible for enterprise financial reporting and operations, financial
planning and analysis, treasury, payments, tax, and international financial operations. From August 2014 to
September 2017, he served as Senior Vice President, Finance, with responsibility for U.S. Retail finance, strategic
and financial planning, and business development activity. Mr. McPhail served as Senior Vice President, Global
FP&A, Strategy, and New Business Development, from March 2013 to August 2014; Vice President, Strategic
Business Development, from January 2007 to March 2013; and director of Strategic Business Development from
May 2005 to January 2007. Prior to joining the Company in 2005, Mr. McPhail served as executive vice president of
corporate finance for Marconi Corporation plc in London, England. Prior to Marconi, Mr. McPhail held positions with
Wachovia Securities and Arthur Andersen.
HECTOR PADILLA, age 48, has been Executive Vice President – Outside Sales & Service since May 2021. He
previously served as Division President of the Southern Division from June 2017 to May 2021, and Senior Vice
President – Operations from November 2014 to June 2017. Mr. Padilla began his career with The Home Depot in
1994 as a store associate and has held roles of increasing responsibility since he joined the Company, serving in
various management roles with oversight of field operations and services.
TERESA WYNN ROSEBOROUGH, age 64, has been Executive Vice President, General Counsel and Corporate
Secretary since November 2011. From April 2006 through November 2011, Ms. Roseborough served in several
legal positions with MetLife, Inc., a provider of insurance and other financial services, including Senior Chief
Counsel – Compliance & Litigation and most recently as Deputy General Counsel. Prior to joining MetLife, Ms.
Roseborough was a partner with the law firm Sutherland Asbill & Brennan LLP from February 1996 through March
2006 and a Deputy Assistant Attorney General in the Office of Legal Counsel of the United States Department of
Justice from January 1994 through February 1996. Ms. Roseborough serves as a director of The Hartford Financial
Services Group, Inc., an investment and insurance company.
FAHIM SIDDIQUI, age 56, has been Executive Vice President and Chief Information Officer since April 2022. He
previously served as Senior Vice President of Information Technology from December 2018 to April 2022. Before
joining The Home Depot, Mr. Siddiqui served as Senior Vice President and Chief Information Officer – eCommerce
and Digital at Staples Inc. from May 2017 through November 2018. Prior to that role, he served in various
technology, product and engineering leadership roles in the retail, energy and telecom sectors.
Item 11. Executive Compensation.
The information required by this item is incorporated by reference to the sections entitled “Executive
Compensation,” “Director Compensation,” and “Leadership Development and Compensation Committee Report” in
our Proxy Statement; provided that the section entitled “Executive Compensation – Pay Versus Performance” in our
Proxy Statement is not incorporated herein by reference.
Item 12. Security Ownership of Certain Beneficial Owners and Management and Related
Stockholder Matters.
The information required by this item is incorporated by reference to the sections entitled “Beneficial Ownership of
Common Stock” and “Executive Compensation – Equity Compensation Plan Information” in our Proxy Statement.
Item 13. Certain Relationships and Related Transactions, and Director Independence.
The information required by this item is incorporated by reference to the section entitled “Corporate Governance” in
our Proxy Statement.
Item 14. Principal Accountant Fees and Services.
The information required by this item is incorporated by reference to the section entitled “Independent Registered
Public Accounting Firm’s Fees” in our Proxy Statement.
Table of Contents
Fiscal 2022 Form 10-K
66

PART IV
Item 15. Exhibit and Financial Statement Schedules.
The following documents are filed as part of this report:
1. Financial Statements
The following financial statements are set forth in Item 8 hereof:
• Report of Independent Registered Public Accounting Firm (KPMG LLP, Atlanta, GA, Auditor Firm ID: 185);
• Consolidated Balance Sheets as of January 29, 2023 and January 30, 2022;
• Consolidated Statements of Earnings for fiscal 2022, fiscal 2021, and fiscal 2020;
• Consolidated Statements of Comprehensive Income for fiscal 2022, fiscal 2021, and fiscal 2020;
• Consolidated Statements of Stockholders’ Equity for fiscal 2022, fiscal 2021, and fiscal 2020;
• Consolidated Statements of Cash Flows for fiscal 2022, fiscal 2021, and fiscal 2020; and
• Notes to Consolidated Financial Statements.
2. Financial Statement Schedules
All schedules are omitted as the required information is inapplicable or the information is presented in our
consolidated financial statements or related notes.
3. Exhibits
Exhibits not filed or furnished herewith are incorporated by reference to exhibits previously filed with the SEC, as
reflected in the table below. Our Current, Quarterly, and Annual Reports are filed with the SEC under File
No. 1-8207. Our Registration Statements have the file numbers noted wherever such statements are identified in
the following list of exhibits. We will furnish a copy of any exhibit to shareholders without charge upon written
request to Investor Relations, The Home Depot, Inc., 2455 Paces Ferry Road, Atlanta, Georgia 30339, via the
internet at http://ir.homedepot.com, or by calling Investor Relations at (770) 384-2871.
2.1 Agreement and Plan of Merger, dated as of
November 15, 2020, by and among The Home
Depot, Inc., Coronado Acquisition Sub Inc. and
HD Supply Holdings, Inc.
Form 8-K filed November 18, 2020, Exhibit 2.1
3.1 Amended and Restated Certificate of
Incorporation of The Home Depot, Inc.
Form 10-Q for the fiscal quarter ended July 31,
2011, Exhibit 3.1
3.2 By-Laws of The Home Depot, Inc. (Amended and
Restated Effective February 23, 2023)
Form 8-K filed February 28, 2023, Exhibit 3.2
4.1 Indenture, dated as of May 4, 2005, between The
Home Depot, Inc. and The Bank of New York
Mellon Trust Company, N.A. (fka The Bank of
New York Trust Company, N.A.), as Trustee
Form S-3 (File No. 333-124699) filed May 6,
2005, Exhibit 4.1
4.2 Indenture, dated as of August 24, 2012, between
The Home Depot, Inc. and Deutsche Bank Trust
Company Americas, as Trustee
Form S-3 (File No. 333-183621) filed August 29,
2012, Exhibit 4.3
4.3 Form of 5.875% Senior Note due December 16,
2036
Form 8-K filed December 19, 2006, Exhibit 4.3
4.4 Form of 5.40% Senior Note due September 15,
2040
Form 8-K filed September 10, 2010, Exhibit 4.2
4.5 Form of 5.95% Senior Note due April 1, 2041 Form 8-K filed March 31, 2011, Exhibit 4.2
4.6 Form of 2.700% Senior Note due April 1, 2023 Form 8-K filed April 5, 2013, Exhibit 4.2
4.7 Form of 4.200% Senior Note due April 1, 2043 Form 8-K filed April 5, 2013, Exhibit 4.3
4.8 Form of 3.750% Senior Note due February 15,
2024
Form 8-K filed September 10, 2013, Exhibit 4.3
4.9 Form of 4.875% Senior Note due February 15,
2044
Form 8-K filed September 10, 2013, Exhibit 4.4
4.10 Form of 4.40% Senior Note due March 15, 2045 Form 8-K filed June 12, 2014, Exhibit 4.3
Exhibit Description Reference
Table of Contents
Fiscal 2022 Form 10-K
67
4.11 Form of 4.250% Senior Note due April 1, 2046 Form 8-K filed June 2, 2015, Exhibit 4.3
4.12 Form of 3.35% Note due September 15, 2025 Form 8-K filed September 15, 2015, Exhibit 4.3
4.13 Form of 3.000% Senior Note due April 1, 2026 Form 8-K filed February 12, 2016, Exhibit 4.3
4.14 Form of 4.250% Senior Note due April 1, 2046 Form 8-K filed February 12, 2016, Exhibit 4.4
4.15 Form of 2.125% Note due September 15, 2026 Form 8-K filed September 15, 2016, Exhibit 4.2
4.16 Form of 3.500% Note due September 15, 2056 Form 8-K filed September 15, 2016, Exhibit 4.3
4.17 Form of 3.900% Note due June 15, 2047 Form 8-K filed June 5, 2017, Exhibit 4.4
4.18 Form of 2.800% Note due September 14, 2027
Form 8-K filed September 14, 2017, Exhibit 4.2
4.19 Form of 3.900% Note due December 6, 2028 Form 8-K filed December 6, 2018, Exhibit 4.4
4.20 Form of 4.500% Note due December 6, 2048 Form 8-K filed December 6, 2018, Exhibit 4.5
4.21 Form of 2.950% Note due June 15, 2029 Form 8-K filed June 17, 2019, Exhibit 4.2
4.22 Form of 3.900% Note due June 15, 2047 Form 8-K filed June 17, 2019, Exhibit 4.3
4.23 Form of 2.950% Note due June 15, 2029 Form 8-K filed January 13, 2020, Exhibit 4.2
4.24 Form of 3.125% Note due December 15, 2049 Form 8-K filed January 13, 2020, Exhibit 4.3
4.25 Form of 2.500% Note due April 15, 2027 Form 8-K filed March 30, 2020, Exhibit 4.2
4.26 Form of 2.700% Note due April 15, 2030 Form 8-K filed March 30, 2020, Exhibit 4.3
4.27 Form of 3.300% Note due April 15, 2040 Form 8-K filed March 30, 2020, Exhibit 4.4
4.28 Form of 3.350% Note due April 15, 2050 Form 8-K filed March 30, 2020, Exhibit 4.5
4.29 Form of 0.900% Note due March 15, 2028 Form 8-K filed January 7, 2021, Exhibit 4.2
4.30 Form of 1.375% Note due March 15, 2031 Form 8-K filed January 7, 2021, Exhibit 4.3
4.31 Form of 2.375% Note due March 15, 2051 Form 8-K filed January 7, 2021, Exhibit 4.4
4.32 Form of 1.500% Note due September 15, 2028 Form 8-K filed September 21, 2021, Exhibit 4.2
4.33 Form of 1.875% Note due September 15, 2031 Form 8-K filed September 21, 2021, Exhibit 4.3
4.34 Form of 2.750% Note due September 15, 2051 Form 8-K filed September 21, 2021, Exhibit 4.4
4.35 Form of 2.700% Note due April 15, 2025 Form 8-K filed March 28, 2022, Exhibit 4.2
4.36 Form of 2.875% Note due April 15, 2027 Form 8-K filed March 28, 2022, Exhibit 4.3
4.37 Form of 3.250% Note due April 15, 2032 Form 8-K filed March 28, 2022, Exhibit 4.4
4.38 Form of 3.625% Note due April 15, 2052 Form 8-K filed March 28, 2022, Exhibit 4.5
4.39 Form of 4.000% Note due September 15, 2025 Form 8-K filed September 19, 2022, Exhibit 4.2
4.40 Form of 4.500% Note due September 15, 2032 Form 8-K filed September 19, 2022, Exhibit 4.3
4.41 Form of 4.950% Note due September 15, 2052 Form 8-K filed September 19, 2022, Exhibit 4.4
4.42 Description of Securities Form 10-K for the fiscal year ended February 2,
2020, Exhibit 4.33
10.1
†
The Home Depot, Inc. 1997 Omnibus Stock
Incentive Plan
Form 10-Q for the fiscal quarter ended August 4,
2002, Exhibit 10.1
10.2
†
Form of Executive Employment Death Benefit
Agreement
Form 10-K for the fiscal year ended February 3,
2013, Exhibit 10.2
10.3
†
The Home Depot Deferred Compensation Plan
for Officers (As Amended and Restated Effective
January 1, 2008)
Form 8-K filed August 20, 2007, Exhibit 10.1
10.4
†
Amendment No. 1 to The Home Depot Deferred
Compensation Plan for Officers (As Amended
and Restated Effective January 1, 2008)
Form 10-K for the fiscal year ended January 31,
2010, Exhibit 10.4
10.5
†
Amendment No. 2 to The Home Depot Deferred
Compensation Plan for Officers (As Amended
and Restated Effective January 1, 2008)
Form 10-K for the fiscal year ended January 31,
2021, Exhibit 10.5
10.6
†
The Home Depot, Inc. Omnibus Stock Incentive
Plan, as Amended and Restated May 19, 2022
Form 10-Q for the fiscal quarter ended July 31,
2022, Exhibit 10.1
Exhibit Description Reference
Table of Contents
Fiscal 2022 Form 10-K
68
10.7
†
The Home Depot FutureBuilder Restoration Plan Form 8-K filed August 20, 2007, Exhibit 10.2
10.8
†
Amendment No.1 to The Home Depot
FutureBuilder Restoration Plan
Form 10-K for the fiscal year ended February 2,
2014, Exhibit 10.8
10.9
*
†
HD Supply Restoration Plan
10.10
†
The Home Depot, Inc. Nonemployee Directors’
Deferred Stock Compensation Plan
Form 8-K filed August 20, 2007, Exhibit 10.3
10.11
†
The Home Depot Amended and Restated
Management Incentive Plan (effective January
31, 2022)
Form 8-K filed May 24, 2022, Exhibit 10.1
10.12
†
The Home Depot, Inc. Amended and Restated
Employee Stock Purchase Plan, as amended and
restated effective July 1, 2012
Form 10-Q for the fiscal quarter ended April 29,
2012, Exhibit 10.1
10.13
†
Form of Executive Officer Restricted Stock Award
Pursuant to The Home Depot, Inc. 1997 Omnibus
Stock Incentive Plan
Form 10-Q for the fiscal quarter ended October
31, 2004, Exhibit 10.1
10.14
†
Form of Deferred Share Award (Nonemployee
Director) Pursuant to The Home Depot, Inc. 2005
Omnibus Stock Incentive Plan
Form 8-K filed November 15, 2007, Exhibit 10.1
10.15
†
Form of Equity Award Terms and Conditions
Agreement Pursuant to The Home Depot, Inc.
2005 Omnibus Stock Incentive Plan
Form 8-K filed March 2, 2011, Exhibit 10.1
10.16
†
Form of Executive Officer Equity Award Terms
and Conditions Agreement Pursuant to The
Home Depot, Inc. Amended and Restated 2005
Omnibus Stock Incentive Plan
Form 8-K filed March 6, 2013, Exhibit 10.1
10.17
†
Form of Executive Officer Equity Award
Agreement (Nonqualified Stock Option) Pursuant
to The Home Depot, Inc. Amended and Restated
2005 Omnibus Stock Incentive Plan
Form 8-K filed March 8, 2016, Exhibit 10.1
10.18
†
Form of Executive Officer Equity Award
Agreement (Performance Based Restricted
Stock) Pursuant to The Home Depot, Inc.
Amended and Restated 2005 Omnibus Stock
Incentive Plan
Form 8-K filed March 8, 2016, Exhibit 10.2
10.19
†
Form of Deferred Share Award (Nonemployee
Director) Pursuant to The Home Depot, Inc. 2005
Omnibus Stock Incentive Plan
Form 10-K for the fiscal year ended January 29,
2017, Exhibit 10.21
10.20
†
Form of Executive Officer Equity Award
Agreement (Performance Based Restricted
Stock) Pursuant to The Home Depot, Inc.
Amended and Restated 2005 Omnibus Stock
Incentive Plan
Form 8-K filed February 28, 2018, Exhibit 10.2
10.21
†
Form of Executive Officer Equity Award
Agreement (Nonqualified Stock Option) Pursuant
to The Home Depot, Inc. Amended and Restated
2005 Omnibus Stock Incentive Plan
Form 8-K filed February 28, 2018, Exhibit 10.3
10.22
†
Form of Executive Officer Equity Award
Agreement (Performance-Based Restricted
Stock) Pursuant to The Home Depot, Inc.
Amended and Restated 2005 Omnibus Stock
Incentive Plan
Form 8-K filed March 4, 2019, Exhibit 10.2
10.23
†
Form of Executive Officer Equity Award
Agreement (Nonqualified Stock Option) Pursuant
to The Home Depot, Inc. Amended and Restated
2005 Omnibus Stock Incentive Plan
Form 8-K filed March 4, 2019, Exhibit 10.3
Exhibit Description Reference
Table of Contents
Fiscal 2022 Form 10-K
69
10.24
†
Form of Executive Officer Equity Award
Agreement Pursuant to The Home Depot, Inc.
Amended and Restated 2005 Omnibus Stock
Incentive Plan
Form 8-K filed March 2, 2020, Exhibit 10.1
10.25
†
Form of Executive Officer Restricted Stock and
Stock Option Award Agreement Pursuant to The
Home Depot, Inc. Amended and Restated 2005
Omnibus Stock Incentive Plan
Form 10-Q for the fiscal quarter ended November
1, 2020, Exhibit 10.4
10.26
†
Form of Executive Officer Equity Award
Agreement Pursuant to The Home Depot, Inc.
Amended and Restated 2005 Omnibus Stock
Incentive Plan
Form 8-K filed March 1, 2021, Exhibit 10.1
10.27
†
Form of Executive Officer Equity Award
Agreement (Performance Shares, Performance-
Based Restricted Stock and Nonqualified Stock
Options) Pursuant to The Home Depot, Inc.
Omnibus Stock Incentive Plan, as Amended and
Restated May 19, 2022
Form 8-K filed May 24, 2022, Exhibit 10.2
10.28
†
Form of Executive Officer Equity Award
Agreement (Restricted Stock and Nonqualified
Stock Options) Pursuant to The Home Depot, Inc.
Omnibus Stock Incentive Plan, as Amended and
Restated May 19, 2022
Form 8-K filed May 24, 2022, Exhibit 10.3
10.29
†
Form of Nonemployee Director Deferred Share
Award Agreement Pursuant to The Home Depot,
Inc. Omnibus Stock Incentive Plan, as Amended
and Restated May 19, 2022
Form 8-K filed May 24, 2022, Exhibit 10.4
10.30
†
Employment Arrangement between Edward P.
Decker and The Home Depot, Inc., dated
February 24, 2022
Form 10-Q for the fiscal quarter ended May 1,
2022, Exhibit 10.1
10.31
†
Employment Arrangement between Richard V.
McPhail and The Home Depot, Inc., dated
October 1, 2020
Form 10-Q for the fiscal quarter ended November
1, 2020, Exhibit 10.1
10.32
†
Employment Arrangement between Craig A.
Menear and The Home Depot, Inc., dated
October 16, 2014
Form 10-Q for the fiscal quarter ended November
2, 2014, Exhibit 10.2
10.33
†
Employment Arrangement between Craig A.
Menear and The Home Depot, Inc., dated
February 24, 2022
Form 10-Q for the fiscal quarter ended May 1,
2022, Exhibit 10.2
10.34
†
Employment Arrangement between Ann-Marie
Campbell and The Home Depot, Inc., dated
October 1, 2020
Form 10-Q for the fiscal quarter ended November
1, 2020, Exhibit 10.3
10.35
*
†
Employment Arrangement between Jeff Kinnaird
and The Home Depot, Inc., dated October 1,
2020
10.36
†
Employment Arrangement between Matthew A.
Carey and The Home Depot, Inc., dated April 19,
2022
Form 10-Q for the fiscal quarter ended May 1,
2022, Exhibit 10.3
21
*
List of Subsidiaries of the Company
23
*
Consent of Independent Registered Public
Accounting Firm
31.1
*
Certification of the Chair, President and Chief
Executive Officer pursuant to Rule 13a-14(a)
31.2
*
Certification of Executive Vice President and
Chief Financial Officer pursuant to Rule 13a-14(a)
32.1
‡
Certification of the Chair, President and Chief
Executive Officer furnished pursuant Section 906
of the Sarbanes-Oxley Act of 2002
Exhibit Description Reference
Table of Contents
Fiscal 2022 Form 10-K
70

32.2
‡
Certification of Executive Vice President and
Chief Financial Officer furnished pursuant to
Section 906 of the Sarbanes-Oxley Act of 2002
101.INS
*
XBRL Instance Document - the instance
document does not appear in the Interactive Data
file because its XBRL tags are embedded within
the Inline XBRL document
101.SCH
*
XBRL Taxonomy Extension Schema Document
101.CAL
*
XBRL Taxonomy Extension Calculation Linkbase
Document
101.DEF
*
XBRL Taxonomy Extension Definition Linkbase
Document
101.LAB
*
XBRL Taxonomy Extension Label Linkbase
Document
101.PRE
*
XBRL Taxonomy Extension Presentation
Linkbase Document
104 Cover Page Interactive Data File (formatted as
inline XBRL and contained in Exhibit 101)
Exhibit Description Reference
—————
† Management contract or compensatory plan or arrangement
* Filed herewith
‡ Furnished (and not filed) herewith pursuant to Item 601(b)(32)(ii) of the SEC’s Regulation S-K
Item 16. Form 10-K Summary.
None.
Table of Contents
Fiscal 2022 Form 10-K
71
SIGNATURES
Pursuant to the requirements of Section 13 or 15(d) of the Securities Exchange Act of 1934, the registrant has duly
caused this report to be signed on its behalf by the undersigned, thereunto duly authorized.
THE HOME DEPOT, INC.
(Registrant)
By:
/s/ EDWARD P. DECKER
Edward P. Decker, Chair, President and Chief
Executive Officer
Date:
March 15, 2023
Pursuant to the requirements of the Securities Exchange Act of 1934, this report has been signed below by the
following persons on behalf of the registrant and in the capacities indicated as of March 15, 2023.
Signature Title
/s/ EDWARD P. DECKER
Chair, President and Chief Executive Officer
(Principal Executive Officer)
Edward P. Decker
/s/ RICHARD V. MCPHAIL
Executive Vice President and Chief Financial Officer
(Principal Financial Officer)
Richard V. McPhail
/s/ STEPHEN L. GIBBS
Vice President, Chief Accounting Officer and Corporate Controller
(Principal Accounting Officer)
Stephen L. Gibbs
/s/ GERARD J. ARPEY
Director
Gerard J. Arpey
/s/ ARI BOUSBIB
Director
Ari Bousbib
/s/ JEFFERY H. BOYD
Director
Jeffery H. Boyd
/s/ GREGORY D. BRENNEMAN
Director
Gregory D. Brenneman
/s/ J. FRANK BROWN
Director
J. Frank Brown
/s/ ALBERT P. CAREY
Director
Albert P. Carey
/s/ LINDA R. GOODEN
Director
Linda R. Gooden
/s/ WAYNE M. HEWETT
Director
Wayne M. Hewett
/s/ MANUEL KADRE
Director
Manuel Kadre
/s/ STEPHANIE C. LINNARTZ
Director
Stephanie C. Linnartz
/s/ PAULA A. SANTILLI
Director
Paula A. Santilli
/s/ CARYN SEIDMAN-BECKER
Director
Caryn Seidman-Becker
Table of Contents
Fiscal 2022 Form 10-K
72


LIVING OUR
VALUES
The Home Depot, Inc.
2455 Paces Ferry Road, Atlanta, GA 30339-4024
(770)433-8211
http://ir.homedepot.com
NYSE: HD
of female and underrepresented
minority groups across our
managers and above cohort
in the U.S.
INCREASED
REPRESENTATION
store leaders started as
of our U.S.
~ 90%
HOURLY ASSOCIATES
by 50% in our U.S. stores
since 2010
Decreased
ELECTRICITY
CONSUMPTION
program helped train over
39,000 participants and
introduced over 132,000
people to the skilled trades
Since 2018, our
PATH TO PRO
of nonhazardous waste
Recycled more than
320,000 METRIC TONS
volunteered nearly
Our associate volunteer force,
TEAM DEPOT,
STRENGTHEN OURFOCUS ON
OUR PEOPLE COMMUNITIES
OPERATE
SUSTAINABLY
1.4 MILLION HOURS
in service to veterans since 2011
